Copyright (c) Hyperion Entertainment and contributors.
AmigaOS Manual: AmigaDOS Command Reference
The commands in this chapter are executed from the Shell window. They are described in alphabetic order; however, some commands reserved for system use appear together at the end of the chapter.
Command Documentation
Each command documented in this manual is shown with the format, arguments, options, symbols, and abbreviations required for proper use.
This chapter and Chapter 7 provide command specifications for the AmigaDOS commands and the Workbench programs accessible through the Shell using the following standard outline:
- Format
- All the arguments and options accepted by a command. The special characters that indicate the particular type of argument are described on page 6-6.
- Template
- An optional on-line reminder of the command's format that is embedded in the program's code. Entering a command followed by a space and a question mark (for example, DIR ?) displays the template. A complete description of the template notation is found on page 6-8.
- Location
- The directory where the command is normally stored.
- Examples
- A sample use of the command. Examples are displayed in the courier typeface to distinguish them from normal text. The 1> represents the Shell prompt; do not type it as part of the example command. Lines in the example not prefaced by 1> represent the output of a command. Command names and keywords are shown in all upper case letters and file and directory names usually have the first letter in upper case; however, they do not need to be entered that way. Press Return to execute the command line.
Separate commands and arguments with spaces. Use punctuation only when required in the syntax of specific commands.
Format
The following lists the characters that indicate the type of argument shown in format listings. Do not use these characters as part of the command.
| < > | Angle brackets indicate where additional information, such as a file name, must be included. This argument is required if it is not surrounded by square brackets. (For example, [<filename>]; see below.) |
| [ ] | Square brackets enclose optional arguments and keywords. Although not required, these arguments and keywords are accepted by the command. |
| { } | Braces enclose items that can be given once or repeated any number of times. For example, {<args>} indicates that several items can be given for this argument. |
| | | Vertical bars separate lists of options from which you can choose only one. For example, [OPT R|S|RS] indicates a choice of the R option, the S option, or both options. |
| <n> | A numeric value is expected by the argument. |
| KEYWORD | Italics indicate that the argument's keyword is required if you include that argument. |
| ... | An ellipsis (...) after a string argument indicates that the string must be the final argument on the command line. Including a comment is not allowed. The remainder of the command line is taken as the desired string. Quotation marks are not needed around the string, even if it contains spaces. If you enter quotation marks, they are part of the string. If you specify the keyword, you can put leading and trailing spaces in the string. |
| command line indentation | On command lines that are long enough to wrap to the next line, this manual shows the wrapped lines as indented for documentation purposes only. In practice, the wrapped lines align with the first character of the Shell prompt. |
The format for the COPY command illustrates the use of these conventions:
COPY [FROM] {<name | pattern>} [TO]<name | pattern>[ALL]
[QUIET] [BUF | BUFFER=<n>] [CLONE] [DATES] [NOPRO]
[COM] [NOREQ]
The [FROM] keyword is optional. If it is not specified, the command reads the file name ir pattern to copy by ist position on the command line.
The {<name | pattern>} argument must be provided. You must substitute either a file name or pattern. The braces indicate that more than one name or pattern can be given.
The [TO] keyword is optional. If it is not specified, the command reads the file name or device to copy to by its position on the command line.
The <name | pattern> argument must be provided. You can specify only one destination.
The [ALL], [QUIET], [CLONE], [DATES], [NOPRO], [COM], and [NOREQ] arguments are optional.
The [BUF | BUFFER=<n>] argument is optional. If given, the keyword is required, but you can use either BUF or BUFFER with the numerical argument. For example, both BUF=5 and BUFFER=5 are acceptable. The numerical argument can also be entered without the equals sign; spaces are optional.
Template
The Template is built into the system to serve as an on-line reminder of a command's syntax and to let you run the command from the Template line by providing a prompt at which you enter the command's arguments.
Display the Template by entering a question mark (?) after a command. The Shell assumes that you wish to run the command and it expects you to enter the command's arguments after the colon following the display. For example:
1> TYPE ? FROM/A/M,TO/K,OPT/K,HEX/S,NUMBER/S:
Pressing Return executes the command if it does not require any arguments to run properly. Entering the arguments and their respective keywords and then pressing Return also executes the command. If a command requires arguments and you do not supply them or if you enter anything other than the required arguments, pressing Return results in a non-fatal error message. Remember that you do not need to enter the entire format for a command at this prompt, just the required arguments.
The Templates are listed with the arguments separated by commas, followed by a slash (/), and a capital letter indicating the type of argument. These slash/letter combinations are displayed to remind you of the command's particular requirements and are not entered as part of the command. The following table explains the notation:
| Template Notation | Format Equivalent | Meaning |
|---|---|---|
| argument/A | <name> | The argument is always required. |
| option/K | KEYWORD | The option's keyword is required if the argument is given. |
| option/S | [KEYWORD] | The option works as a switch. The name of the option must be entered to specify it. Most options are switches. |
| value/N | <n> | The argument is numeric. |
| argument/M | {<name>} | Multiple items are accepted for this argument. Although there is no limit to the number of possible arguments, they must be provided before the next argument or option. |
| string/F | argument... | The string must be the final argument on the command line; the remainder of the command line is taken as the desired string. |
| = | KYWD | KEYWORD | Two different forms of the keyword are equivalent and either are accepted. The equals sign is not entered as part of the command. |
The Template for the COPY command illustrates the use of arguments:
FROM/M,TO/A,ALL/S,QUIET/S,BUF=BUFFER/K/N, CLONE/S,DATES/S,NOPRO/S,COM/S,NOREQ/S
FROM/M indicates that the argument is required and more than one argument is acceptable.
TO/A indicates that the argument is required.
ALL/S, QUIET/S, CLONE/S, DATES/S, NOPRO/S, COM/S, and NOREQ/S indicate that the keywords act as switches. If the keyword is present in the line, the option is used.
BUF=BUFFER/K/N indicates that the BUF or BUFFER keyword (/K) is required to specify this numerical (/N) argument. Both BUF and BUFFER are acceptable keywords (=).
Keywords and their arguments can be linked with an equals sign (=) to ensure correct assignments in complex cases. For example, BUF=20.
Command Listing
ADDAUDIOMODES
Manipulates the audio mode list.
- Format
- ADDAUDIOMODES [FILES <file | pattern>] [QUIET] [REMOVE] [DBLSCAN]
- Template
- FILES/M,QUIET/S,REFRESH/S,REMOVE/S,DBLSCAN/S
- Location
- C:
Audio modes supported by the Amiga's audio system (ahi.device) are stored in the DEVS:Audiomodes directory as audio mode description files. Once the ahi.device is initiated, it scans the directory and builds an internal audio mode list based on the description files stored in the Audiomodes directory. The constructed audio mode list exists in RAM and can be manipulated by the ADDAUDIOMODES command.
The internal audio mode list can be cleared, new modes can be added to the list, or the original list can be restored. Note that any changes made to the audio mode list with the ADDAUDIOMODES command are not permanent.
The FILES parameter is used for adding audio modes to the list. The FILES parameter supplies the name or names of the audio mode description files which should be used for adding the new audio modes.
The REMOVE option will remove all audio modes from the internal audio mode list, while the REFRESH option restores the original audio modes by forcing the ahi.device to rebuild the internal audio mode list.
The DBLSCAN option does not have any effect on the audio mode list. Instead it will open and then immediately close a double-scan screen. On the original Amiga hardware this will enable over 28 kHz sample playback frequencies.
If the QUIET option is supplied, ADDAUDIOMODES will not print any messages.
- Example
Rebuild the audio mode list:
1> ADDAUDIOMODES REFRESH
ADDBUFFERS
Instructs the file system to add or display cache buffers for a drive.
- Format
- ADDBUFFERS <drive> [<n>]
- Template
- DRIVE/A,BUFFERS/N
- Location
- C:
ADDBUFFERS adds <n> buffers to the list of buffers available for <drive>. Although adding buffers speeds disk access, each additional buffer reduces free memory by approximately 512 bytes. The default buffer allocation is 5 for floppy drives and 30 for hard disk partitions.
The amount of extra available memory dictates the number of buffers you can add. There is no fixed upper limit; however, adding too many buffers reduces overall system performance by taking RAM away from other system functions. Specifying a negative number subtracts that many buffers from the current allocation. The minimum number of buffers is one; however, using only one is not recommended.
Twenty buffers are recommended for a floppy drive in a 512 KB system. Use the default value recommended by the HDToolBox program for hard disks. (Display this value by selecting the Advanced Options gadget on the Partitioning screen.)
If only the <drive> argument is specified, ADDBUFFERS displays the number of buffers currently allocated for that drive.
- Example
1> ADDBUFFERS DF0: DF0: has 5 buffers
A further example of ADDBUFFERS appears in Chapter 8.
ADDNETINTERFACE
Makes network interfaces known to the protocol stack.
- Format
- ADDNETINTERFACE {<interface>} [QUIET] [TIMEOUT <seconds>]
- Template
- INTERFACE/M,QUIET/S,TIMEOUT/K/N
- Location
- C:
ADDNETINTERFACE starts the specified network interfaces, thus starting the connection. It accepts the following parameters:
| INTERFACE | The name of the interface to add; this can be a plain interface name, such as "Ariadne", or the fully qualified file name which contains the interface configuration information. The tool expects the name of the file in question (without the prefixed path) to become the name of the interface. For historic reasons interface names cannot be longer than 15 characters.
For your convenience, a wild card pattern can be specified in place of the file name to use. If several interface names are specified, they will be sorted in alphabetical order before they are added. If the interface files have icons attached, you can use tool types such as "PRI=5" or "PRIORITY=5" to select the order in which the interfaces will be sorted. Higher priority entries will appear before lower priority entries. If the priorities for two entries is identical, then the interface names will be compared. If no priority is given, the value 0 will be used. |
| QUIET | This option causes the program not to emit any error messages or progress reports. Also, if the program encounters an error it will flag this as failure code 5 which can be looked at using the "IF WARN" shell script command. If this option is not in effect, failure codes will be more severe and all sorts of progress information will be displayed. |
| TIMEOUT | If you're going to use DHCP configuration for any of the interfaces, a default timeout value of 60 seconds will limit the time an interface can take to be configured. This parameter allows you to use a different timeout value. Note that due to how the configuration protocol works, the timeout cannot be shorter than ten seconds. |
The 'AddNetInterface' command can be invoked from Workbench, too. It operates on the same configuration files with the same keywords, etc. To make it work, create an icon for your interface configuration file (it must be a project icon) and put 'AddNetInterface' into its default tool. Make sure that the project has enough stack space assigned (4000 bytes minimum), then double-click on the icon. If things should go wrong, you will see an error requester pop up, and no further initialization will be done. You can configure two options in the project file's tool types: QUIET and TIMEOUT. These are identical to the two parameters of the same name you could pass on the command line; they define whether the command should print any error messages (the default is to print them) and how long the command should wait for DHCP configuration to conclude (default is a timeout of 60 seconds).
| Note |
|---|
| This command is similar to the Unix "ifconfig" command. |
| Note |
|---|
| The program makes two passes over the configuration files to be taken into account. In the first pass information is gathered on the interfaces to add, which is subsequently used to add those interfaces found. In the second pass interfaces are configured, setting their IP addresses, etc. If anything goes wrong in the first pass, processing will stop and no second pass will be done. If anything goes wrong in either the first or the second pass, that pass will not be completed. |
- CONFIGURATION FILES
Interfaces are configured through files stored in the "DEVS:NetInterfaces" or "SYS:Storage/NetInterfaces" directories. These are text files whose contents are described below.
Each line of the file must correspond to an option; if a line is introduced by a '#' or ';' character it will be ignored (so are empty lines). The following options are supported:
| DEVICE/K | Must be provided; the name of the SANA-II device driver. This should be the complete, fully qualified path to the driver. If no complete path is provided, the 'Devs:Networks' drawer will be checked. Thus, "DEVS:Networks/ariadne.device" is equivalent to "ariadne.device". |
| UNIT/K/N | Unit number of the device driver to open. The default is to use unit 0. |
| IPTYPE/K/N | You can use this parameter to override the packet type the stack uses when sending IP packets; default is 2048 (for Ethernet hardware). |
| ARPTYPE/K/N | You can use this parameter to override the packet type the stack uses when sending ARP packets. Default is 2054; this parameter only works with Ethernet hardware and should not be changed. |
| IPREQUESTS/K/N | The number of IP read requests to allocate and queue for the SANA-II device driver to use. The default value is 32, larger values can improve performance, especially with fast device drivers. |
| WRITEREQUESTS/K/N | The number of IP write requests to allocate and queue for the SANA-II device driver to use. The default value is 32, larger values can improve performance, especially with fast device drivers. |
| ARPREQUESTS/K/N | The number of ARP read requests to allocate and queue for the SANA-II device driver to use. The default value is 4. |
| DEBUG/K (possible parameters: YES or NO) | You can enable debug output for this interface (don't worry, you can always disable it later) to help in tracking down configuration problems. At this time of writing, the debug mode will, if enabled, produce information on the progress of the DHCP configuration process. |
| POINTTOPOINT/K (possible parameters: YES or NO) | This indicates that the device is used for point to point connections. The stack automatically figures out whether the SANA-II device driver is of the point to point type, so you should not need to specify this option. |
| MULTICAST/K (possible parameters: YES or NO) | This tells the stack that this device can handle multicast enabled by default anyway). |
| DOWNGOESOFFLINE/K (possible parameters: YES or NO) | This option is useful with point to point devices, like 'ppp.device'. When specified, bringing the interface 'down' (via the 'ConfigureNetInterface' program) or shutting down the stack will cause the associated SANA-II device driver to be switched offline (via the 'S2_OFFLINE' command). |
| REPORTOFFLINE/K (possible parameters: YES or NO) | When a device is switched offline, you may want to know about it. This is helpful with SLIP/PPP connections which run over a serial link which accumulates costs while it is open. When the connection is broken and the device goes offline, you will receive a brief notification of what happened. However, if you tell the library itself to shut down, no notification that a device was switched offline will be shown. |
| REQUIRESINITDELAY/K (possible parameters: YES or NO) | Some devices need a little time to settle after they have been opened or they will hickup and lose data after the first packet has been sent. The original 'Ariadne I' card is one such device. For these devices, the 'REQUIRESINITDELAY=YES' option will cause a delay of about a second before the first packet is sent.
This option defaults to YES. |
| COPYMODE/K (possible parameters: SLOW or FAST) | This option is for chasing subtle bugs in the driver interface with cards like the original 'Ariadne I'. Cards like these do not support writing to the hardware transmit buffer in units other than 16 bits a piece. Default is 'SLOW', which is compatible with the Ariadne I. But if you're feeling adventurous, try the 'FAST' option (and don't complain if it doesn't work for you!). |
| FILTER/K (possible parameters: OFF, LOCAL, IPANDARP or EVERYTHING) | This option enables the use of the Berkeley packet filter for this particular interface. Possible choices for the key are:
FILTER=OFF Disables the filter. FILTER=LOCAL Enables filtering on all IP and ARP packets that are intended for this particular interface. Packets intended for other interfaces or hosts are ignored. FILTER=IPANDARP Enables filtering on all IP and ARP packets that happen to fly by this interface, no matter whether the packets are intended for it or not. This requires that the underlying network device driver is opened for exclusive access in so-called 'promiscuous' mode. This may not work if other clients (Envoy, ACS) need to keep the driver opened. FILTER=EVERYTHING Identical to FILTER=IPANDARP, but will also filter all other kinds of packets that may show up. Default for this option is 'FILTER=LOCAL'. Note that by using this option you merely define what the filter mechanism can do and what it cannot do. The filter is not enabled when you add the interface. |
| HARDWAREADDRESS/K | You can specify the hardware address (layer 2 address, MAC address) this interface should respond to when it is first added and configured. This usually works only once for each interface, which means that once an address has been chosen you have to stick with it until the system is rebooted. And it also means that the first program to configure the address will manage to make its choice stick.
The hardware address must be given as six bytes in hexadecimal notation, separated by colon characters, like this: HARDWAREADDRESS=00:60:30:00:11:22 Take care, there are rules that apply to the choice of the hardware address, which means that you cannot simply pick a convenient number and get away with it. It is assumed that you will want to configure an IEEE 802.3 MAC address, which works for Ethernet hardware and is six bytes (48 bits) in size. |
In addition to the purely static interface configuration information you can also tell the configuration program to do something about the interfaces once they have all been added. That's when the following configuration file parameters will be taken into account:
| ADDRESS/K | This configures the IP address of the interface. The parameter you supply should be an IP address in dotted-decimal notation ("192.168.0.1"). Don't pick a symbolic host name as the system may not yet be in a position to talk to name resolution server and translate the symbolic name.
In place of the IP address you can also specify "DHCP" (Dynamic Host Configuration Protocol). As the name suggests, this will start a configuration process involving the DHCP protocol which should eventually yield the right IP address for this host. Note that this configuration procedure only works for Ethernet hardware. |
| ALIAS/K/M | In addition to the primary interface address you can assign several aliases to it. These must be specified in dotted-decimal notation ("192.168.0.1"). Alias addresses are added after the primary interface address has been configured. |
| STATE/K | By default, interfaces whose addresses are configured will switch automatically to 'up' state, making it possible for the TCP/IP stack to use them for network I/O. You can override this by using the 'STATE=DOWN' switch. The alternatives 'online' (implies 'up', but tells the underlying network interface driver to go online first) and 'offline' (implies 'down' but tells the driver to go offline first) are available as well. |
| NETMASK/K | This selects the subnet mask for the interface, which must be specified in dotted-decimal notation ("192.0.168.1").
In place of the subnet mask you can also specify "DHCP" (Dynamic Host Configuration Protocol). As the name suggests, this will start a configuration process involving the DHCP protocol which should eventually yield the right subnet mask for this host. Note that this configuration procedure only works for Ethernet hardware. |
| DESTINATION=DESTINATIONADDR/K | The address of the point-to-point partner for this interface; must be specified in dotted-decimal notation ("192.168.0.1"). Only works for point-to-point connections, such as PPP. |
| METRIC/K/N | This configures the interface route metric value. Default is 0. |
| MTU/K/N | You can limit the maximum transmission size used by the TCP/IP stack to push data through the interface. The interface driver will have its own ideas about the maximum transmission size. You can therefore only suggest a smaller value than the driver's preferred hardware MTU size. |
| CONFIGURE/K (possible parameters: DHCP, AUTO or FASTAUTO) | You can use DHCP configuration for this interface and protocol stack internals, namely the list of routers (and the default gateway) to use and the domain name servers. This option allows you to bring up the complete network configuration in one single step.
You can request that a particular IP address is assigned to this interface by the DHCP process by specifying CONFIGURE=DHCP and your choice of ADDRESS=xxx.xxx.xxx.xxx. If your network has no DHCP server, you may choose CONFIGURE=AUTO to use automatic IPv4 address selection, based upon a protocol called ZeroConf. This protocol will select a currently unused address from a specially designated address range. If you choose automatic configuration in a wireless network, you might want to use CONFIGURE=FASTAUTO instead of CONFIGURE=AUTO. Note that only the CONFIGURE=DHCP option will attempt to set up a default route and a set of DNS servers for you to use. The alternatives of CONFIGURE=FASTAUTO and CONFIGURE=AUTO are restricted to selecting the network interface IPv4 addresses. |
| LEASE/K | This is a complex option which can be used to request how long an IP address should be bound to an interface, via the DHCP protocol. Several combinations of options are possible. Here is a short list:
LEASE=300 LEASE=300seconds This requests a lease of exactly 300 seconds, or five minutes. LEASE=30min This requests a lease of 30 minutes. LEASE=2hours This requests a lease of 2 hours. LEASE=1day This requests a lease of 1 day. LEASE=4weeks This requests a lease of 4 weeks. LEASE=infinite This requests that the IP address should be permanently bound. Blank spaces between the numbers and the qualifiers are supported. The qualifiers are tested using substring matching, which means for example that "30 minutes" is the same as "30 min" and "30 m". Note that the requested lease time may be ignored by the DHCP server. After all, it is just a suggestion and not an order. |
| ID/K | This option works along with the CONFIGURE=DHCP process. It can be used to tell the DHCP server by which name the local host should be referred to. Some DHCP servers are on good terms with their local name resolution services and will add the name and the associated IP address to the local host database. The name you can supply here cannot be longer than 255 characters and must be at least 2 characters long. Keep it brief: not all DHCP servers have room for the whole 255 characters. |
| DHCPUNICAST/K | Some DHCP servers may not be able to respond to requests for assigning IP addresses unless the responses are sent directly to the computer which sent the requests. In such cases you might want to use DHCPUNICAST=YES option. |
Unsupported keywords in the configuration file (or typos) will be reported, along with the name of the file and the line number.
The name of the configuration file defines the name of the respective interface. Interface names must be unique, and the case of the names does not matter. For historic reasons interface names cannot be longer than 15 characters. Beyond this no restrictions on naming conventions apply.
- DHCP PROTOCOL
A few words on DHCP (Dynamic Host Configuration Protocol). First, it only works for Ethernet hardware, so please don't try it with PPP or SLIP. Now it gets a bit technical. Unless you request an address to be permanently assigned, DHCP will assign addresses only for a limited period of time. This is called a 'lease'. Once an IP address has been assigned through DHCP, the lease will be repeatedly extended. The DHCP server may over time decide not to extend the lease or assign a new IP address to the interface. To stop the lease from getting extended over and over again, you must either change the interface's primary IP address or mark it 'down'. The library will make a brave attempt to get a DHCPRELEASE datagram out to notify the server that the previously allocated IP address is no longer in use. Don't count on it to work, though. First, the protocol stack might be going down so fast that it cannot get the datagram out. Second, when you mark an interface 'down' you will effectively pull it out of circulation, it will not send any further datagrams. Third, DHCP rides on UDP whose second name is 'unreliable datagram protocol', meaning that any datagram may get lost or corrupted and nobody will hear about it; this is rather hard on DHCP since the release message is sent only once. Don't worry. Unless you request permanent leases, the leases will eventually time out and the now unused IP address will finally return to the pool of addresses available for allocation.
- Examples
Start the interface called "DSL" and run quietly.
1> AddNetInterface DSL QUIET
An example configuration file for the "Ariadne" interface, with some options commented out:
1> Type Devs:NetInterfaces/Ariadne device=ariadne.device unit=0 #iprequests=64 #writerequests=64 copymode=fast #configure=dhcp address=192.168.0.1 netmask=255.255.255.0 #alias=192.168.0.9 #hardwareaddress=00:60:30:00:11:22 #id=a3000ux #debug=yes #filter=everything
ADDNETROUTE
Adds message routing paths.
- Format
- ADDNETROUTE [QUIET] [DESTINATION=<IP>] [HOSTDESTINATION=<IP>] [NETDESTINATION=<IP>] [GATEWAY=<IP>] [DEFAULTGATEWAY=<IP>]
- Template
- QUIET/S,DST=DESTINATION/K,HOSTDST=HOSTDESTINATION/K,NETDST=NETDESTINATION/K,VIA=GATEWAY/K,DEFAULT=DEFAULTGATEWAY/K
- Location
- C:
ADDNETROUTE allows to define routes to hosts or networks via an interface.
The options are:
| QUIET | This option causes the program not to emit any error messages or progress reports. Also, if the program encounters an error it will flag this as failure code 5 which can be looked at using the "if warn" shell script command. If this option is not in effect, failure codes will be more severe and all sorts of progress information will be displayed. |
| DST or DESTINATION | The destination address of a route (or in other words, where the route to be added leads to). This must be an IP address or a symbolic name. Some routes may require you to specify a gateway address through which the route has to pass. Depending upon the address you specify, the protocol stack will attempt to figure out whether the destination is supposed to be a host or a network. |
| HOSTDST or HOSTDESTINATION | Same as the DST/DESTINATION parameter, except that the destination is assumed to be a host (rather than a network). |
| NETDST or NETDESTINATION | Same as the DST/DESTINATION parameter, except that the destination is assumed to be a network (rather than a host). |
| DEFAULT or DEFAULTGATEWAY | This parameter selects the default gateway address (which must be specified as an IP address or a symbolic host name) all messages are sent to which don't have any particular other routes associated with them. Another, perhaps less misleading name for "default gateway address" is "default route". |
| Note |
|---|
| The command is similar to the Unix "route" command. |
| Note |
|---|
| If you use the DEFAULT/DEFAULTGATEWAY parameter, all other destination addresses you may have specified will be ignored. Only one of DESTINATION, HOSTDESTINATION or NETDESTINATION will be used; choose only one. Before you add a new default gateway you should delete the old one or you'll get an error message instead. |
- Example 1
Define a route to the host 192.168.10.12 through a gateway at 192.168.1.1
1> ADDNETROUTE HOSTDESTINATION 192.168.10.12 VIA 192.168.1.1
- See also
ALIAS
Sets or displays command aliases.
- Format
- ALIAS [<name>] [<string...>]
- Template
- NAME,STRING/F
- Location
- Internal
ALIAS creates aliases, or alternative names, for AmigaDOS commands. ALIAS can be used to abbreviate frequently used commands or replace standard command names with different names.
When AmigaDOS encounters <name>, it replaces it with the defined <string>, integrate the result with the rest of the command line, and attempts to interpret and execute the resulting line as an AmigaDOS command <Name> is the alias for the command and <string> is the command to be substituted for the alias.
An alias must be entered at the beginning of the command line. You can enter arguments after the alias, but you cannot create an alias to represent a series of command arguments. For example, in the following command line:
1> NEWSHELL WINDOW=CON:0/250/640/150/2SHELL/CLOSE
the WINDOW argument cannot be replaced with an alias.
You can substitute a file name or other instruction within an alias by placing square brackets ([ ]) with nothing between them in the <string>. Any argument entered after the alias is inserted at the brackets.
ALIAS <name> displays the <string> for that alias. Entering ALIAS alone lists all current aliases.
Aliases are local to the Shell in which they are defined. If you create another Shell with the NEWSHELL command, it shares the same aliases as its parent Shell. However, if you create another Shell with the Execute Command menu item, it des not recognize aliases created in your original Shell. A global lais that is recognized by all Shells can be crated by inserting the alias in the Shell-startup file.
To remove an ALIAS, use the UNALIAS command.
- Example 1
1> ALIAS d1 DIR DF1:
Entering d1 displays a directory of the contents of the disk in DF1:; as if you entered DIR DF1:.
- Example 2
1> ALIAS hex TYPE [ ] HEX
creates an alias called HEX that displays the contents of a specified file in hexadecimal format. The empty brackets indicate where the file name is inserted in this example. Entering:
1> hex Myfile
displays the contents of Myfile in hexadecimal format.
- See also
APPLISTINFO
?
- Format
- <file>
- Template
- FILENAME/S
- Location
- C:
Missing description.
ARP
Displays and modifies the address translation tables.
- Format
- ARP [-a|ALL] [-d|DELETE] [-s|SET] [HOSTNAME <host>] [ADDRESS <address>]
- [TEMP] [PUB|PUBLISH] [PRO|PROXY] [{-f|FILE} <file name>] [-n|NONAMES|NUMBERS]
- Template
- -a=ALL/S,-d=DELETE/S,-s=SET/S,HOSTNAME,ADDRESS,TEMP/S,PUB=PUBLISH/S,PRO=PROXY/S,-f=FILE/K,-n=NONAMES/S=NUMBERS/S
- Location
- C:
The ARP command displays and modifies the Internet-to-Ethernet address translation tables used by the Address Resolution Protocol (ARP). The host to be inspected or modified can be specified by name or by number, using the Internet dot notation.
The options are:
| ALL or -a | Display all of the current ARP entries. |
| DELETE or -d | Removes any ARP table entry for the host specified with the HOSTNAME parameter. See example 3. |
| SET or -s | Create a new ARP address mapping entry for the host with the supplied hardware address. The HOSTNAME parameter tells the host and the ADDRESS parameter the hardware address. |
| HOSTNAME | Name of the host which entries will be listed or modified. |
| ADDRESS | A hardware address (Ethernet address) of the host to be added or to be deleted from the ARP table. The address is given as six hex bytes separated by colons. See example 2. |
| TEMP | Add a temporary ARP entry. This option is used only with the SET parameter. |
| PUB or PUBLISH | The added ARP entry will be 'published'. The host will act as an ARP server, responding to requests for hostname even though the host address is not its own. This option is used only with the SET parameter. |
| PRO or PROXY | Adds a proxy ARP entry. This option is used only with the SET parameter. |
| FILE or -f | Causes the file <file name> to be read and multiple entries to be set in the ARP tables. Entries in the file should be of the form
with argument meanings as given for the SET option. |
| NONAMES or -n or NUMBERS | Show network addresses as numbers (normally ARP attempts to display addresses symbolically). |
- Example 1
List the current ARP entries:
1> ARP ALL
- Example 2
Create a temporary ARP entry for the host 'Oberon' and publish it.
1> ARP SET Oberon 00:30:ab:0e:d5:ee TEMP PUB
- Example 3
Delete any ARP entry of the host 'Oberon':
1> ARP DELETE Oberon
ASK
Gets yes or no user input during script file execution.
- Format
- ASK <prompt>
- Template
- PROMPT/A
- Location
- Internal
ASK is used in scripts to write the string specified by <prompt> to the current window and then wait for keyboard input. Valid keyboard responses are Y (yes), N (no), and Return (no). Selecting Y sets the condition flag to 5 (WARN). Selecting N or pressing Return sets the condition flag to 0. Check the response using an IF statement.
If the <prompt> contains spaces, it must be enclosed in quotation marks.
- Example
Assume a script contained the following commands:
ASK Continue?
IF WARN
ECHO Yes
ELSE
ECHO No
ENDIF
At the ASK command, Continue? Is displayed on the screen. If Y is pressed, Yes is displayed on the screen. If N or a Return alone is pressed, No is displayed.
- See also
ASSIGN
Controls assignment of logical device names to files or directories.
- Format
- ASSIGN [<name>:{dir}] [FROM <file name>] [TO <file name>] [LIST]
- [EXISTS] [DISMOUNT] [DEFER] [PATH] [ADD] [PREPEND] [REMOVE] [VOLS]
- [DIRS] [DEVICES] [NOREQ]
- Template
- NAME,TARGET/M,FROM/K,TO/K,LIST/S,EXISTS/S,DISMOUNT/S,DEFER/S,PATH/S,ADD=APPEND/S,PREPEND/S,REMOVE/S,VOLS/S,DIRS/S,DEVICES/S,NOREQ/S
- Location
- C:
ASSIGN allows directories to be referenced via short, convenient logical device names, rather than their usual names or complete paths. ASSIGN gives an alternative directory name, much as ALIAS permits alternative command names. The ASSIGN command can create assignments, remove assignments, or list some or all current assignments.
If the <name> and {dir} arguments are given, ASSIGN assigns the given name to the specified directory. Each time the assigned logical device name is referred to, AmigaDOS accesses the specified directory. If the <name> given is already assigned to a directory, the new directory will replace the previous directory. (Always be sure to include a colon after the <name> argument.)
If only the <name> argument is given, any existing ASSIGN of a directory to that logical device will be cancelled.
You can assign several logical device names to the same directory by using multiple ASSIGN commands.
You can assign one logical device name to several directories by specifying each directory after the <name> argument or by using the ADD or APPEND option. When the APPEND option is specified, any existing directory assigned to <name> is not cancelled. Instead, the newly specified directory is appended to the end of the assign list and the system will search for both directories when <name> is encountered. If the first directory is not available, ASSIGN will be satisfied with the newly added directory.
The PREPEND option does the same thing as the APPEND option except the additional assignment is added at the front of the assing list. The PREPEND option is available with Assing version 53.2 or higher.
To delete a name from the assign list, use the REMOVE option.
If no arguments are given with ASSIGN, or if the LIST keyword is used, a list of all current assignments will be displayed. If the VOLS, DIRS, or DEVICES switch is specified, ASSIGN will limit the display to volumes, directories, or devices, respectively.
When the EXISTS keyword is given along with a logical device name, AmigaDOS will search the ASSIGN list for that name and display the volume and directory assigned to that device. If the device name is not found, the condition flag is set to 5 (WARN). This is commonly used in scripts.
Normally, when the {dir} argument is given, AmigaDOS immediately looks for that directory. If the ASSIGN commands are part of S:startup-sequence, the directories need to be present on a mounted disk during the boot procedure. If an assigned directory cannot be found, a requester appears asking for the volume containing that directory. However, two new options, DEFER and PATH, will wait until the directory is actually needed before searching for it.
| Note |
|---|
| The assigned name does not have to retain the name of the directory and it does not have to be in upper case. For example, the name CLIPS: or Clips: can be assigned to the Ram Disk:Clipboards directory. |
The DEFER option creates a "late-binding" ASSIGN. This ASSIGN only takes effect when the assigned object is first referenced, rather than when the assignment is made. This eliminates the need to insert disks during the boot procedure that contain the directories that are assigned during the startup-sequence. When the DEFER option is used, the disk containing the assigned directory is not needed until the object is actually called upon.
For example, if you assign FONTS: to DF0:Fonts with the DEFER option, the system will associate FONTS: with whatever disk is in DF0: at the time FONTS: is called. If you have Workbench disk in DF0: at the time the FONTS: is needed, the system will associate FONTS: with that particular Workbench disk. If you later remove that Workbench disk and insert another disk containing a Fonts directory, the system will specifically request the original Workbench disk the next time FONTS: is needed.
The PATH option creates a "non-binding" ASSIGN. A non-binding ASSIGN acts like a DEFERed ASSIGN, except that it is re-evaluated each time the assigned name is referenced. This prevents the system from expecting a particular volume in order to use a particular directory (such as the situation described in the example above). For instance, if you assign FONTS: to DF0:Fonts with the PATH option, any disk in DF0: will be searched when FONTS: is referenced. As long as the disk contains a Fonts directory, it will satisfy the ASSIGN. Up until V54 DOS library, you could not assign multiple directories with the PATH option.
The PATH option is especially useful to users with floppy disk systems as it eliminates the need to reinsert the original Workbench disk used to boot the system. As long as the drive you have assigned with the PATH option contains a disk with the assigned directory name, the system will use that disk.
Instead of specifying on the command line which assignments to set up and how, you can tell the ASSIGN command to read a list of specifications from a file using the FROM option. In that file, there must be one assignment specification per line; lines beginning with the ';' character are ignored. The file could look like this:
FONTS: MyFonts:Fontdir LIBS: SYS:Libs BigAssem:Libs PDAssem:Libs WorkDisk: DF0: DEFER C: DF0:C PATH
As you can see, it is possible to set up deferred and path assignments and assignment lists, too.
To complement the FROM option there is the TO option which will store the current list of assignments in a file, suitable for use with the FROM option.
The NOREQ option will prevent any "Please insert volume..." requester windows from appearing which may be triggered by attempts to make assignments to volumes which are currently unavailable. While the command will fail to establish any assignment producing such an error, a script file in which the command is used can keep on running without requiring manual intervention.
| Note |
|---|
| The DISMOUNT option (called REMOVE in V1.3) is no longer active. From V54+ use the new dedicated C:Dismount command instead. |
- Example 1
1> ASSIGN FONTS: MyFonts:Fontdir
assigns the FONTS: directory to Fontdir on MyFonts:
- Example 2
1> ASSIGN LIST Volumes: Ram Disk [Mounted] Workbench [Mounted] MyFonts [Mounted] Directories: LOCALE Workbench:Locale KEYMAPS Workbench:Devs/Keymaps PRINTERS Workbench:Devs/Printers REXX Workbench:S CLIPS Ram Disk:Clipboards ENV Ram Disk:Env T Ram Disk:T ENVARC Workbench:Prefs/Env-Archive SYS Workbench: C Workbench:C S Workbench:S L Workbench:L FONTS MyFonts:Fontdir DEVS Workbench:Devs LIBS Workbench:Libs + Workbench:Classes Devices: PIPE AUX RAM CON RAW PAR SER PRT DF0
Shows a typical list of all current assignments. The plus sign indicates any additional directories with the same assignment.
- Example 3
1> ASSIGN FONTS: EXISTS FONTS: MyFonts:FontDir
is an inquiry into the assignment of FONTS:. AmigaDOS responds by showing that FONTS: is assigned to the FontDir directory of the MyFonts volume. The return code is set to 0 if it exists or to 5 if it does not.
- Example 4
1> ASSIGN LIBS: SYS:Libs BigAssem:Libs ADD
is a multiple-directory assignment that creates a search path containing two Libs directories. Specifying ADD keeps the standard SYS:Classes assignment from being removed. These directories are searched in sequence each time LIBS: is invoked.
- Example 5
1> ASSIGN WorkDisk: DF0: DEFER 1> ASSIGN WorkDisk: EXISTS WorkDisk <DF0:>
sets up a late-binding assignment of the logical device WorkDisk:. Until the first time you refer to the name WorkDisk:, you do not need to insert it in DF0: ASSIGN shows DF0: enclosed in angle brackets to indicate that it is DEFERred. After the first reference to WorkDisk:, the volume name of the disk that was in DF0: replaces <DF0:>.
- Example 6
1> ASSIGN C: DF0:C PATH 1> ASSIGN C: EXISTS C [Df0: C]
will reference the C directory of whatever disk is in DF0: at the time a command is searched for. Notice that ASSIGN shows DF0:C in square brackets to indicate that it is a non-binding ASSIGN.
- Example 7
1> ASSIGN LIBS: Zcad:Libs ADD
adds Zcad:Libs to the list of directories assigned as LIBS:.
- Example 8
1> ASSIGN LIBS: Zcad:Libs REMOVE
removes Zcad:Libs from the list of directories assigned as LIBS:.
For more examples using ASSIGN, see Chapter 8.
AVAIL
Reports the amount of Chip and Fast memory available.
- Format
- AVAIL [CHIP | FAST | VIRTUAL | TOTAL] [FLUSH] [SHOW=<BLOCKS|BYTES|SIZE>]
- Template
- CHIP/S,FAST/S,TOTAL/S,FLUSH/S,VIRTUAL/S,SHOW/K
- Location
- C:
AVAIL reports the amount of installed memory and how musch of it is available free for use.
The figures in the complete summary are localised.
The SHOW option selects the format in which the figures in the complete summary will be printed. This must be one of BYTE, KILO, or MEGA. "BYTE", which is the default, will display plain figures. "KILO" will display the same information in KB. "MEGA" will display the same information in MB.
By using the CHIP, FAST, VIRTUAL, or TOTAL options, you can have AVAIL display only the number of free bytes of Chip, Fast, Virtual, or total RAM available, instead of the complete summary. This value can be used for comparisons in scripts.
These types are obsolete as of AmigaOS 4.x and the options CHIP, FAST, and VIRTUAL are only kept to ensure compatibility with older scripts.
The FLUSH option is obsolete and does nothing.
- Example 1
1> AVAIL Installed: 536.870.912 Free: 437.252.096
- Example 2
1> AVAIL TOTAL 437252096
- Example 3
1> AVAIL SHOW=MEGA Installed: 512,000 M Free: 416,104 M
BREAK
Sets attention flags in the specified process.
- Format
- BREAK <process> [NAME <program name or pattern>] [ALL | C | D | E | F]
- Template
- PROCESS/N,NAME/K,ALL/S,C/S,D/S,E/S,F/S
- Location
- C:
BREAK sets the specified attention flags in the <process> indicated. C sets the Ctrl-C flag, D sets the Ctrl-D flag, and so on. ALL sets all the flags from Ctrl-C to Ctrl-F. By default, AmigaDOS only sets the Ctrl-C flag.
Ctrl-C is used as the default for sending a BREAK signal to halt a process. A process that has been aborted this way will display ***BREAK in the Shell window. Ctrl-D is used to halt execution of a script file. Ctrl-E is used to exit Commodity Exchange programs. Ctrl-F is not currently used.
A process can be signalled by giving a name or a wildcard pattern. The name will be compared against the program's name (including its full path, if available) and the program name (excluding the path), if the first test did not produce a match.
- See also
- Example 1
1> BREAK 7
sets the Ctrl-C attention flag of process 7. This is identical to selecting process 7 and pressing Ctrl-C.
- Example 2
1> BREAK 5 D
sets the Ctrl-D attention flag of process 5.
- Example 3
1> BREAK NAME "DIR#?"
sets the Ctrl-C attention flag of all processes whose name begin with the letters "DIR"; this would include the "DIR" program, for example.
BUILDMAPTABLE
Creates a binary mapping table to Unicode for diskfont library from an ASCII mapping table.
- Format
- BUILDMAPTABLE <ASCII mapping table> [CHARSET]
- Template
- UNICODEMAPTABLE/A,CHARSET/K
- Location
- SDK:C
BUILDMAPTABLE converts Charset-To-Unicode mapping tables in text form (e.g. available at http://www.unicode.org/Public/MAPPINGS/) to mapping tables in binary form usable by diskfont library.
You must specify a charset mapping table file name when using the BUILDMAPTABLE command.
BUILDMAPTABLE can either display a text form of the parsed table or create a binary mapping table in the L:Charsets/ directory. Currently only 8-bit charset mapping tables are supported.
If L:Charsets/character-sets or L:Charsets/custom-character-sets contains a MIME name for an 8-bit charset where no mapping table in L:Charsets/ does exist, and you have a mapping table in text form, use BUILDMAPTABLE to create the binary mapping table and reboot (diskfont library searches tables only once) to be able to use the new charset (e.g. in fonts or catalog files).
The expected format of text mapping tables is as follows:
- Anything from a '#' character to the end of a line is considered a comment.
- A valid line does contain the index on the left and the Unicode code point at the right side, in either hexadecimal (starting with 0x or 0X) or octal (starting with 0) or decimal form, separated by empty space. Example:
0xA4 0x20AC # EURO SIGN
The other options are:
| CHARSET | Specify a MIME charset name or alias. The MIME charset name obtained from diskfont library will be used as file name of the binary charset mapping table which will be stored in L:Charsets/. If the CHARSET parameter is omitted, no file will be written, instead the resulting mapping table is displayed in text form. |
- Example 1
1> BUILDMAPTABLE CP1258.TXT
Will parse the text file CP1258.TXT and display a list of entries with the index on the left and the Unicode codepoint at the right side. Note: unmapped entries (with Unicode codepoint 0) are not displayed.
- Example 2
1> BUILDMAPTABLE 8859-1.TXT CHARSET LATIN1
Will parse the text file 8859-1.TXT and create the file L:Charsets/ISO-8859-1 (latin1 is an alias for ISO-8859-1) which is useless (the ISO-8859-1 mapping table is a builtin part of diskfont library and will not be loaded from disk).
CACHESTAT
Displays information on the system caches.
- Format
- [VERBOSE]
- Template
- VERBOSE/S
- Location
- C:
Missing description.
CD
Sets or displays the current directory.
- Format
- CD [<dir | pattern>]
- Template
- DIR
- Location
- Internal
CD with no arguments displays the name of the current directory. When a valid directory name is given, CD makes the named directory the current directory.
You must specify a complete path to the directory since CD does not search through the disk for it. If CD cannot find the specified directory in the current directory or in the given path, a Can't find <directory> message is displayed.
To move up a level in the filing hierarchy to the parent directory of the current directory, enter CD followed by a space and a single slash (/). You can move to another directory in the parent at the same time by including its name after the slash. If the current directory is a root directory, CD / has no effect. Use multiple slashes with no spaces between them to refer to additional higher levels.
To move directly to the root directory of the current device, use CD followed by a space and a colon; for example, CD :
AmigaDOS supports an implied CD so that the CD command itself can often be left out. Enter the directory name, path, colon, or slashes at the prompt.
CD also supports pattern matching. When a directory matching the specified pattern is found, it becomes the current directory. If more than one directory matches the given pattern, an error message is displayed. You cannot use pattern matching with implied CD. For more information an pattern matching, see Chapter 3.
- Example 1
1> CD DF1:Work
sets the current directory to the Work directory on the disk in drive DF1:.
- Example 2
1> CD SYS:Com/Basic
makes the subdirectory Basic in the Com directory the current directory.
- Example 3
1> //
using the implied CD, moves up two levels in the directory structure.
- Example 4
1> CD SYS:Li#?
uses the #? pattern to match with the LIBS: directory.
For more examples using the CD command, see Chapter 8.
CHANGETASKPRI
Changes the priority of a currently running process.
- Format
- CHANGETASKPRI <priority> [<process>] [NAME <program name or pattern>]
- Template
- PRI=PRIORITY/A/N,PROCESS/K/N,NAME/K
- Location
- C:
Since the Amiga is multitasking, it uses priority numbers to determine the order in which current tasks should be serviced. Normally, most tasks have a priority of 0, and the time and instructions cycles of the CPU are divided equally among them. CHANGETASKPRI changes the priority of the specified Shell process. (If no process is specified, the current Shell process is assumed.) Any started from <process> inherit its priority.
The range of acceptable values for <priority> is the integers from -128 to 127, with higher values yielding a higher priority (a greater proportion of CPU time is allocated). However, do not enter values above +10, or you may disrupt important system tasks. Too low a priority (less than 0) can result in a process taking unreasonably long to execute, priority -128 does not make much sense because at that priority runs the idle.task.
The name of the process whose priority number should be changed can be given, or a wildcard pattern that should match it. The name will be compared against the program's name (including its full path, if available) and the program name (excluding the path), if the first test did not produce a match. If more than one command matches the pattern given, then all these commands will have their priorities changed.
- See also
- Example 1
1> CHANGETASKPRI 4 Process 2
The priority of Process 2 is changed to 4. Any tasks started from this Shell will also have a priority of 4. They will have priority over any other user tasks created without using CHANGETASKPRI (those tasks will have a priority of 0).
- Example 2
1> CHANGETASKPRI 4 NAME "DIR"
The priority of the program "DIR" is changed to 4. Note that if there is more than one command to match the name, CHANGETASKPRI will abort with an error message.
CHARSETCONVERT
Converts a text file from one character set into another.
- Format
- CHARSETCONVERT <from file> <from charset> [to file] [to charset] [EOL [CR] [LF] [CRLF]]
- Template
- FROM/A,FROMCHARSET/A,TO,TOCHARSET,EOL/K
- Location
- C:
CHARSETCONVERT converts the text file specified with the FROM argument from the character set specified with the FROMCHARSET argument to the character set specified with the TOCHARSET argument or to the current system default character set if the TOCHARSET argument is not specified. The result is written to the file specified with the TO argument or output to the current window if the TO argument is not specified.
The FROMCHARSET and TOCHARSET parameters are MIME character set names or aliases registered at IANA stored in L:Charsets/character-sets or custom character set names or aliases stored in L:Charsets/custom-character-sets. Currently only 8-bit character sets with a mapping table to Unicode (which can be created by the BUILDMAPTABLE command) in L:Charsets/ are supported, plus those additional charsets:
- FROMCHARSET may also be UTF-7, UTF-8, UTF-16BE, UTF-16LE, UTF-32BE or UTF-32LE.
- TOCHARSET may also be UTF-8.
CHARSETCONVERT will return with result code 20 (FAILURE) when a severe error occurs, with result code 10 (ERROR) when the input file contains invalid data (NULL or a character or encoding sequence which is undefined or invalid in FROMCHARSET found in FROM file), with result code 5 (WARN) when at least one input character could not be represented in the TOCHARSET and was replaced by an "<UXXXX>" sequence, and with result code 0 (OK) if all went well.
CHARSETCONVERT has options which will change the way the output is displayed. These options are explained below:
| TO <name> | Specifies an output file or device for CHARSETCONVERT; by default, CHARSETCONVERT outputs to the current window. | ||||||
| TOCHARSET <name> | Specifies the destination character set for CHARSETCONVERT; by default, CHARSETCONVERT converts to the current system default character set. | ||||||
| EOL <type> | Converts End-Of-Line (EOL) sequences to the specified type. If not specified, no EOL conversion does happen. The EOL type parameter must match one of the following keywords:
|
- Example 1
1> CHARSETCONVERT russian KOI8-R russian-ISO ISO-8859-5 EOL=LF
Will read the text file russian, convert the character set from KOI8-R to ISO-8859-5, convert the EOL sequences to Amiga style, and write the result to russian-ISO.
- Example 2
1> CHARSETCONVERT czech.txt X-ATO-E2 czech-ISO2.txt ISO-8859-2
Will read the text file czech.txt, convert the character set from X-ATO-E2 (the character set of the OS3.x czech catalog files) to ISO-8859-2, replace unconvertable characters with an <UXXXX> sequence and write the result to czech-ISO2.txt.
- Example 3
1> SETFONT topaz 8 CHARSET ISO-8859-16 1> CHARSETCONVERT polish.txt X-ATO-PL TOCHARSET ISO-8859-16
Will read the text file polish.txt, convert the character set from X-ATO-PL (the character set of the OS3.x polish catalog files) to ISO-8859-16 and display the result in the current window with topaz.font, size 8, in ISO-8859-16.
CLIP
Reads or writes any clipboard unit.
- Format
- CLIP [<unit>] [WAIT] [ GET | PUT <string> | COUNT ]
- Template
- U=UNIT/N/K,W=WAIT/S,G=GET/S,P=PUT=S=SET/S,C=COUNT/S,TEXT
- Location
- C:
CLIP can store some text in the clipboard, retrieve some text from it or count how many clipboard units are filled.
Using the GET argument will retrieve text from the specified unit number (if supplied). Using the SET argument and a <string> will store this <string> into the specified unit number (if supplied). Using the COUNT argument will count and display the number of filled clipboard units.
The UNIT argument is used to specify which of the clipboard units should be used for the GET/PUT action.
The TEXT argument is the text data to be stored in the clipboard unit.
The WAIT argument, used along with the GET action, will wait for the unit to be filled with text data. Then it will perform the GET action. It may be useful in scripts.
If no GET, PUT or COUNT argument is specified, text will be retrieved. i.e. GET is the default action. If no unit number is specified, text will be written to/read from unit 0.
- Example 1
Store the text "Amiga" in the clipboard unit 2
1> CLIP PUT Amiga UNIT 2
- Example 2
Retrieve and display the text stored in the clipboard unit 2
1> CLIP UNIT 2 Amiga
- Example 3
Display how many clipboard units contain data
1> CLIP COUNT 1
- Example 4
Delete the content of clipboard unit 0
1> CLIP SET
CMIBOOST
Boosts microphone input.
- Format
- ?
- Template
- ?
- Location
- C:
Missing description.
CONFIGURENETINTERFACE
Configure network interface parameters.
- Format
- CONFIGURENETINTERFACE [QUIET] [TIMEOUT=<seconds>] INTERFACE Incomplete
- Template
- INTERFACE/A,QUIET/S,ADDRESS/K,NETMASK/K,BROADCASTADDR/K,DESTINATION=DESTINATIONADDR/K,METRIC/K/N,MTU/K/N,ALIASADDR/K,DELETEADDR/K,ONLINE/S,OFFLINE/S,UP/S,DOWN/S,DEBUG/K,COMPLETE/K,CONFIGURE/K,LEASE/K,RELEASE=RELEASEADDRESS/S,ID/K,TIMEOUT/K/N,DHCPUNICAST/K
- Location
- C:
CONFIGURENETINTERFACE is used to define how a network interface will react and how it will interact with your network.
The options are:
| INTERFACE | The name of the interface to be configured. This is a required parameter. | ||||||||
| QUIET | This option causes the program not to emit any error messages or progress reports. Also, if the program encounters an error it will flag this as failure code 5 which can be looked at using the 'if warn' shell script command. If this option is not in effect, failure codes will be more severe and all sorts of progress information will be displayed. | ||||||||
| ADDRESS | The IP address to assign to this interface. This should be specified in dotted-decimal notation ("192.168.0.1") and not as symbolic name since the system may not be in a state to perform a name resolution.
In place of the IP address you can also specify "DHCP". As the name suggests, this will start a configuration process involving the DHCP protocol which should eventually yield the right IP address for this host. Note that this configuration procedure only works for Ethernet hardware. | ||||||||
| NETMASK | The subnet mask to assign to this interface. This must be specified in dotted-decimal notation ("192.168.0.1").
In place of the subnet mask you can also specify "DHCP". As the name suggests, this will start a configuration process involving the DHCP protocol which should eventually yield the right subnet mask for this host. Note that this configuration procedure only works for Ethernet hardware. | ||||||||
| BROADCASTADDR | The broadcast address to be used by this interface; must be specified in dotted-decimal notation ("192.168.0.1") and only works with interfaces that support broadcasts in the first place (i.e. Ethernet hardware). | ||||||||
| DESTINATION or DESTINATIONADDR | The address of the point-to-point partner for this interface; must be specified in dotted-decimal notation ("192.168.0.1"). Only works for point-to-point connections, such as PPP. | ||||||||
| METRIC | Route metric value for this interface. | ||||||||
| MTU | You can limit the maximum transmission size used by the TCP/IP stack to push data through the interface. The interface driver will have its own ideas about the maximum transmission size. You can therefore only suggest a smaller value than the driver's preferred hardware MTU size. | ||||||||
| ALIASADDR | This adds another address to this interface to respond to. You can add as many aliases as you like, provided you don't run out of memory. | ||||||||
| DELETEADDR | This removes an alias address from the list the interface is to respond to. | ||||||||
| Options ONLINE, OFFLINE, UP, and DOWN | The 'line state' of the interface is configured through the following four options:
| ||||||||
| DEBUG | Possible parameters are YES and NO. You can enable debug output for this interface to help in tracking down configuration problems. At this time of writing, the debug mode will, if enabled, produce information on the progress of the DHCP configuration process. | ||||||||
| COMPLETE | Possible parameters are YES and NO. If you configure an interface in several steps, use this parameter in the final invocation of the program. It will tell the TCP/IP stack that the configuration for this interface is complete. This has the effect of causing the static route definition file to be reread, if necessary. | ||||||||
| RELEASEADDRESS | If an IP address was dynamically assigned to an interface, this switch will tell ConfigureNetInterface to release it. Note that you can only release what was previously allocated. | ||||||||
| CONFIGURE | Possible parameters are DHCP, AUTO, and FASTAUTO. You can use DHCP configuration for this interface and protocol stack internals, namely the list of routers (and the default gateway) to use and the domain name servers. This option allows you to bring up the complete network configuration in one single step.
You can request that a particular IP address is assigned to this interface by the DHCP process by specifying CONFIGURE=DHCP and your choice of ADDRESS=xxx.xxx.xxx.xxx. If your network has no DHCP server, you may choose CONFIGURE=AUTO to use automatic IPv4 address selection, based upon a protocol called ZeroConf. This protocol will select a currently unused address from a specially designated address range. If you choose automatic configuration in a wireless network, you might want to use CONFIGURE=FASTAUTO instead of CONFIGURE=AUTO. Note that only the CONFIGURE=DHCP option will attempt to set up a default route and a set of DNS servers for you to use. The alternatives of CONFIGURE=FASTAUTO and CONFIGURE=AUTO are restricted to selecting the network interface IPv4 addresses. | ||||||||
| TIMEOUT | If you're going to use DHCP configuration for any of the interfaces, a default timeout value of 60 seconds will limit the time an interface can take to be configured. This parameter allows you to use a different timeout value. Note that due to how the configuration protocol works, the timeout cannot be shorter than ten seconds. | ||||||||
| LEASE | This is a complex option which can be used to request how long an IP address should be bound to an interface. Several combinations of options are possible. Here is a short list:
This requests a lease of exactly 300 seconds, or five minutes.
This requests a lease of 30 minutes.
This requests a lease of 2 hours.
This requests a lease of 1 day.
This requests a lease of 4 weeks.
This requests that the IP address should be permanently bound. Blank spaces between the numbers and the qualifiers are supported. The qualifiers are tested using substring matching, which means for example that "30 minutes" is the same as "30 min" and "30 m". Note that the requested lease time may be ignored by the DHCP server. After all, it is just a suggestion and not an order. | ||||||||
| ID | This option works along with the CONFIGURE=DHCP process. It can be used to tell the DHCP server by which name the local host should be referred to. Some DHCP servers are on good terms with their local name resolution services and will add the name and the associated IP address to the local host database. The name you can supply here cannot be longer than 255 characters and must be at least 2 characters long. Keep it brief: not all DHCP servers have room for the whole 255 characters. | ||||||||
| DHCPUNICAST | Possible parameters are YES and NO. Some DHCP servers may not be able to respond to requests for assigning IP addresses unless the responses are sent directly to the computer which sent the requests. In such cases you might want to use DHCPUNICAST=YES option. |
| Note |
|---|
| The command is similar to the Unix "ifconfig" command. |
| Note |
|---|
| If you tell an interface to go online then the program's return code will tell you if the command succeeded: a return value of 0 indicates success (the interface is now online), and a value of 5 indicates that it didn't quite work. |
| Note |
|---|
| Configuring the address of an interface has two effects: first, the interface will be marked as 'up', meaning that the protocol stack will attempt to send messages through it when appropriate. Second, a direct route to the interface will be established. |
- See also
COPY
Copies files or directories.
- Format
- COPY [FROM] {<name | pattern>} [TO] <name> [ALL] [QUIET]
- [BUF | BUFFER=<n>] [CLONE] [DATES] [NOPRO] [COM] [NOREQ]
- [NOREPLACE] [INTERACTIVE] [FORCE] [ARCHIVE] [NEWER]
- [COPYLINKS] [FOLLOWLINKS]
- Template
- FROM/A/M,TO/A,ALL/S,QUIET/S,BUF=BUFFER/K/N,CLONE/S,DATES/S,NOPRO/S,COM/S,NOREQ/S,NOREPLACE/S,INTERACTIVE/S,FORCE/S,ARCHIVE/S,NEWER/S,COPYLINKS/S,FOLLOWLINKS/S
- Location
- C:
COPY copies the file or directory specified with the FROM argument to the file or directory specified by the TO argument. You can copy several items at once by giving more than one FROM argument; each argument should be separated by spaces. You can use pattern matching to copy or exclude items whose names share a common set of characters or symbols.
If a TO filename already exists, COPY overwrites the TO file with the FROM file. If you name a destination directory that does not exist, COPY will create a directory with that name. You can also use a pair of double quotes ("") to refer to the current directory when specifying a destination. (Do not put any spaces between the double quotes.)
If the FROM argument is a directory, only the directory's files will be copied; its subdirectories will not be copied. Use the ALL option to copy the complete directory, including its files, subdirectories, and the subdirectories' files. If you want to copy a directory and you want the copy to have the same name as the original, you must include the directory name in the TO argument.
COPY prints to the screen the name of each file as it is copied. This can be overridden by the QUIET option or the local shell variable _Verbosity with a negative value.
The BUF option is used to set the number of 512-byte buffers used during the copy. (Default is 200 buffers, approximately 100K of RAM.) It is often useful to limit the number of buffers when copying to RAM:. BUF=0 uses a buffer the same size as the file to be copied.
Normally, copy gives the TO file the date and time the copy was made. Any comments attached to the original FROM file are ignored. The protection bits of the FROM file are copied to the TO file. Several options allow you to override these defaults:
| DATES | The creation date of the FROM file is copied to the TO file. |
| COM | Any comment attached to the FROM file is copied to the TO file. |
| CLONE | The date, comments and protection bits of the FROM file are copied to the TO file. |
| NOPRO | The protection bits of the FROM file are not copied to the TO file. The TO file will be given standard protection bits of r, w, e and d. |
| NOREPLACE | Checks if the destination file already exists. If this is the case, then the file is not copied. |
| INTERACTIVE | Checks if the destination file already exists. In this case, you will be prompted to confirm that you want the file to be overwritten (answer 'y' for 'yes'). |
| FORCE | If the destination file could not be created because there already is a file of that name which is protected against deletion or writing, then the protection will be removed first before the destination file is created. |
| ARCHIVE | Copy only those files for which the 'archived' flag is unset. After copying, the 'archived' flag will be set on the file just copied. Note that the ARCHIVE option implies the CLONE option which will be enabled by default. |
| NEWER | Overwrite files only if the destination file is older than the source file, or of there is no destination file by the same name as the source file. |
| COPYLINKS | Copy the contents of a file referenced by a hard or soft link; the default is to skip copying linked files. |
| FOLLOWLINKS | When used with the ALL option, the COPY command will follow hard and soft links to directories; the default is to skip links to directories. |
Normally, COPY displays a requester if the COPY cannot continue for some reason. When the NOREQ option is given, all requesters are suppressed. This is useful in scripts and can prevent a COPY failure from stopping the script while it waits for a response. For instance, if a script calls for a certain file to be copied and the system cannot find that file, normally the script would display a requester and would wait until a response was given. With the NOREQ option, the COPY command would be aborted and the script would continue.
- Example 1
1> COPY File1 TO :Work/File2
copies File1 in the current directory to File2 in the Work directory.
- Example 2
1> COPY ~(#?.info) TO DF1:Backup
copies all the files not ending in .info in the current directory to the Backup directory on the disk in DF1:. This is a convenient use of pattern matching to save storage space when icons are not necessary.
- Example 3
1> COPY Work:Test TO ""
copies the files in the Test directory on Work to the current directory; subdirectories in Test will not be copied.
- Example 4
1> COPY Work:Test TO DF0:Test ALL
copies all the files and any subdirectories of the Test directory on Work to the Test directory on DF0:. If a Test directory does not already exist on DF0:, AmigaDOS will create one.
- Example 5
1> COPY Work:Test% TO DF0: ALL
copies the directory Test including all the contained files and subdiretories to DF0:. If DF0:Test does not exist, it will be created.
- Example 6
1> COPY (Dir1|Dir2|%) TO DF0: ALL QUIET
copies the directories Dir1 and Dir2 including all the contained files and subdirectories to DF0:. If any of the directories does not already exist on DF0:, AmigaDOS will create each.
- Example 7
1> COPY DF0: TO DF1: ALL QUIET
copies all files and directories on the disk in DF0: to DF1:, without displaying on the screen any file/directory names as they are copied. (This is quite slow in comparison to DiskCopy.)
COUNTLINES
Counts how many lines a file is made of.
- Format
- COUNTLINES {<filename>}
- Template
- NAME/A/M
- Location
- C:
COUNTLINES counts the number of lines of the file(s) given in argument. If several arguments are given, a sum of all line counts will be returned.
CPU
Adjusts various options of the microprocessor installed in your Amiga. The command also shows the processor and options that are currently enabled.
- Format
- CPU [CACHE | NONCACHE] [BURST | NOBURST] [DATACAHCE | NODATACACHE] [DATABURST | NODATABURST] [INSTCACHE | NOINSTCACHE] [INSTBURST | NOINSTBURST] [FASTROM | NOFASTROM] [TRAP | NOTRAP] [COPYBACK | NOCOPYBACK] [EXTERNALCACHE | NOEXTERNALCACHE] [NOMMUTEST] [CHECK 68010 | 68020 | 68030 | 68040 | 68881 | 68882 | 68851 | MMU | FPU]
- Template
- CACHES/S,BURST/S,NOCACHE/S,NOBURST/",DATACACHE/S,NODATACHE/S,DATABURST/S,NODATABURST/S,INSTCACHE/S,NOINSTCACHE/S,INSTBURST/S,NOINSTBURST/S,COPYBACK/S,NOCOPYBACK/S,EXTERNALCACHE/S,NOEXTERNALCACHE/S,FASTROM/S,NOFASTROM/S,TRAP/S,NOTRAP/S,NOMMUTEST/S,CHECK/K
- Location
- C:
Many options only work with certain members of the 680x0 processor family. The 68020 has a special type of memory known as instruction cache. When instruction cache is used, instructions are executed more quickly. The 68030 and 68040 have two types of cache memory: instruction and data.
If mutually exclusive options are specified, the safest option is used. Availability of the following options depends on the type of microprocessor present.
| CACHE | Turns on all caches. |
| NOCACHE | Turns off all caches. |
| BURST | Turns on burst mode for both data and instructions. |
| NOBURST | Turns off burst mode for data and instructions. |
| DATACACHE | Turns on data cache. |
| NODATACACHE | Turns off data cache. |
| DATABURST | Turns on burst mode for data. |
| NODATABURST | Turns off burst mode for data. |
| INSTCACHE | Turns on instruction cache. |
| NOINSTCACHE | Turns off instruction cache. |
| INSTBURST | Turns on burst mode for instructions. |
| NOINSTBURST | Turns off burst mode for instructions. |
| FASTROM | With a processor having a supported MMU, copies the system ROM into 32-bit RAM, making access to operating system functions significantly faster. CPU then write-protects the RAM area so that the data cannot be changed. |
| NOFASTROM | Turns off FASTROM. |
| TRAP | This option is for developers only. |
| NOTRAP | This option is for developers only. |
| COPYBACK | Turns on 68040 copyback cache. |
| NOCOPYBACK | Turns off 68040 copyback cache. |
| EXTERNALCACHE | Turns on external cache. |
| NOEXTERNALCACHE | Turns off external cache. |
| NOMMUTEST | Allows the MMU settings to be changed without checking to see if an MMU is currently in use. |
The CHECK option, when given with a keyword (68010, 68020, 68030, 68040, 68881, 68882, or 68851, MMU, FPU) checks for the presence of the processor indicated by the keyword.
- Examples
1> CPU System: 68030 68881 (INST: Cache Burst) (DATA: Cache NoBurst)
1> CPU NODATACACHE FASTROM System: 68030 68881 FastRom (INST: Cache Burst) (DATA: NoCache NoBurst)
1> CPU NOBURST DATACACHE NOINSTCACHE System: 68030 68881 (INST: NoCache NoBurst) (DATA: Cache NoBurst)
CUT
Cuts some characters or words from a string.
- Format
- CUT <string> [ CHAR <range> | WORD <range> [SEPARATOR] ]
- Template
- STRING/A,C=CHAR/K,W=WORD/K,S=SEPARATOR
- Location
- C:
CUT will extract any number of characters or words out of a string.
The extracted string is defined by a begin and an end position. Those values will be characters or words positions in the original string. I.e you may want to extract a string beginning with a character at position P1 and ending with a character at position P2. Behaviour is the same with words instead of characters.
Use the CHAR argument if you want to use begin/end values defined in characters. Use the WORD argument if you want to extract any number of words. Words are strings separated by the "space" character (default). Using the SEPARATOR argument, you can specify a string of any length to be used to split the original string in words.
The length of the string to extract will depend on the begin (P1) and the end (P2) position in the original string. This P1-P2 range to give after the CHAR (or WORD) argument follows the template:
P1[-P2] | [P1-]P2 | [P1]-P2 | P1-[P2]
The begin (P1) and end (P2) values are optional.
This allows to extract only one character (or word) if you omit the end value. i.e with the argument like "CHAR P1"
In order to extract several characters (or words), you need to specify a range with the "-" character like "CHAR P1-P2"
You can omit P1 if you want a string starting at the beginning of <string> with "CHAR -P2". And you do not need to know the string length because P2 can be omited like "CHAR P1-". This will extract the string beginning with character at position P1 and ending at the end of the original <string>.
- Example 1
To extract one character:
1> CUT "Hello world" CHAR=2 -> e
- Example 2
To extract from character 1 to 5:
1> CUT "Hello world" CHAR=1-5 -> Hello
- Example 3
The same without specifying the beginning position.
1> CUT "Hello world" CHAR=-5 -> Hello
- Example 4
To extract from character 7 of the string till the end:
1> CUT "Hello world" CHAR=7- -> world
- Example 5
To extract one word (with another separator):
1> CUT "Hello world" WORD=1 separator="ll" -> He
DATE
Displays or sets the system date and/or time.
- Format
- DATE [<day>] [<date>] [< time >] [SERVER <name>] [PORT <n>] [OFFSET <n>]
- [LFORMAT <string>] [TO | VER <filename>]
- Template
- DAY,DATE,TIME,SERVER/K,PORT/K/N,OFFSET/K/N,LFORMAT/K,TO=VER/K
- Location
- C:
DATE with no argument displays the currently set system date and time, including the day of the week. Time is displayed using a 24-hour clock.
DATE <date> sets just the date. The date can be specified either in the current default locale format or in the AmigaDOS format DD-MMM-YY (day-month-year). If the AmigaDOS format is used, the hyphens between the arguments are required. A leading zero in the date is not necessary. The first 3 letters of the month (in the current locale language) must be used, as well as the last two digits of the year.
The date can also be reset by specifying a day name, thus setting the date forward to that day of the week. You can also use tomorrow or yesterday as the <day> argument.
DATE
The SERVER option is used to retrieve the current date and time from a remote server over a TCP/IP connection using the Network Time Protocol (NTP). A list of NTP time servers and some good background information can be found at http://www.eecis.udel.edu/~mills/ntp/servers.html.
The SERVER option may be set to the special value "PREFS" which will retrieve the date and time from the currently configured remote server information stored in the Time preferences.
By using PORT you can specify a port number different to the default 123.
The OFFSET argument allows to set the offset in minutes of your location with respect to Greenwich Mean Time (GMT). If OFFSET is not specified, the locale offset will be used.
The LFORMAT option modifies the output of DATE using one or more substitution operators. See below for available substitution operators.
| %a | abbreviated weekday name |
| %A | weekday name |
| %b | abbreviated month name |
| %B | month name |
| %c | same as "%a %b %d %H:%M:%S %Y" |
| %d | day number with leading 0s |
| %D | same as "%m/%d/%y" |
| %e | day number with leading spaces |
| %h | abbreviated month name |
| %H | hour using 24-hour style with leading 0s |
| %I | hour using 12-hour style with leading 0s |
| %j | julian date |
| %m | month number with leading 0s |
| %M | the number of minutes with leading 0s |
| %n | insert a linefeed |
| %p | AM or PM strings |
| %q | hour using 24-hour style |
| %Q | hour using 12-hour style |
| %r | same as "%I:%M:%S %p" |
| %R | same as "%H:%M" |
| %S | number of seconds with leadings 0s |
| %t | insert a tab character |
| %T | same as "%H:%M:%S" |
| %U | week number, taking Sunday as first day of week |
| %w | weekday number |
| %W | week number, taking Monday as first day of week |
| %x | same as "%m/%d/%y" |
| %X | same as "%H:%M:%S" |
| %y | year using two digits with leading 0s |
| %Y | year using four digits with leading 0s |
If you specify the TO or VER option, followed by a filename, the output of the DATE command is sent to that file, overwriting any existing contents.
If your Amiga does not have a battery backed-up hardware clock and you do not set the date, the system, upon booting, will set the date to the date of the most recently created file on the boot disk.
| Note |
|---|
| Adjustments made with DATE only change the software clock. They will not survive past power-down. To set the battery backed-up hardware clock from the Shell, you must set the date and use SETCLOCK SAVE. |
If DATE succeeded in setting the system date and/or time, the primary return code (RC) will be set to 0. A return code of 5 or 20 indicates that DATE failed partially or completely. If an error occurred when trying to get time from a remote server, the primary return code will be set to 21. In this case the secondary return code (RESULT2) may contain a TCP stack socket/resolver error number and the corresponding error message will be displayed.
- Example 1
1> DATE 6-Sep-92
displays the current date and time.
- Example 2
1> DATE LFORMAT "Today it's %A, %m/%d/%Y, %T"
displays a message like "Today it's Monday, 02/17/2003, 22:30:56".
- Example 3
1> DATE 1-jan-04
sets the date to January 1st, 2004 (the earliest date you can set is January 1, 1978). The time is not reset.
- Example 4
1> DATE tomorrow
resets the date to one day ahead.
- Example 5
1> DATE TO Fred
sends the current date to the file Fred.
- Example 6
1> DATE 23:00
sets the current time to 11:00 p.m.
- Example 7
1> DATE SERVER foo.bar.com OFFSET -480
gets the current date and time from the foo.bar.com NTP server for a location based on the Pacific Standard Time used in the United States.
DELETE
Deletes files or directories.
- Format
- DELETE {<name|pattern>} [ALL] [QUIET] [INTER|INTERACTIVE]
- [FORCE] [WIPE]
- Template
- FILE/M/A,ALL/S,QUIET/S,INTER=INTERACTIVE,FORCE/S,WIPE/S
- Location
- C:
DELETE attempts to delete (erase) the specified file(s). If more than one file was specified, AmigaDOS continues to the next file in the list.
You can use pattern matching to delete files. The pattern may specify directory levels as well as filenames. All files that match the pattern are deleted. To abort a multiple-file DELETE, press Ctrl-C.
AmigaDOS does not request confirmation of deletions. An error in a pattern-matching DELETE can have severe consequences, as deleted files are unrecoverable. Be sure you understand pattern matching before you use this feature, and keep backups of important files.
Warning: If you try to delete a directory that contains files, you will receive a message stating that the directory could not be deleted as it is not empty. To override this, use the ALL option. DELETE ALL deletes the named directory, its subdirectories, and all files.
Filenames are displayed on the screen as they are deleted. To suppress the screen output, use the QUIET option or the local shell variable _Verbosity with a negative value.
If the d (deletable) protection bit of a file has been cleared, that file cannot be deleted unless the FORCE option is used.
If the INTERACTIVE option is used, you will be prompted to confirm each single deletion (enter 'y' to confirm). Note that the FORCE option will override the INTERACTIVE option, turning it off.
For most file systems deleting a single file will only make the storage space previously reserved for it available again, but will not render the contents of the file unrecoverable. In order to make recovery of sensitive data much harder, use the WIPE option which, prior to deleting the file, will overwrite the contents of the file up to 7 times using the United States Department of Defense 5220-22.M standard procedure for this purpose. This can take long to complete.
| Note |
|---|
| The WIPE operation implemented by the DELETE command is suitable only for magnetic storage media, such as floppy disks or hard disk drives. To wipe optical, magneto-optical or solid state memory storage devices you would need a different method, which is not currently implemented by the DELETE command.
While the contents of the file will be overwritten, the name of the file and any directories to be deleted will not be overwritten. You may want to move or rename file and directories prior to deletion. While the contents of the file will be overwritten, the name of the file and any directories to be deleted will not be overwritten. You may want to move or rename file and directories prior to deletion. The DELETE command does not guarantee that the file contents will be securely deleted because the file system and the underlying storage hardware may reduce the effectiveness of the overwrite operations. The FORMAT command may be more effective in securely wiping a storage medium, albeit at the expense of wiping the entire partition/disk rather than just a single file. If the FORCE and WIPE options are combined, then each file will have its write and delete protection removed before it is wiped. |
- Example 1
1> DELETE Old-file
deletes the Old-file file in the current directory.
- Example 2
1> DELETE Work/Prog1 Work/Prog2 Work
deletes the files Prog1 and Prog2 in the Work directory, and then deletes the Work directory (if there are no other files left in it).
- Example 3
1> DELETE T#?/#?(1|2)
deletes all files that end in 1 or 2 in directories that start with T.
- Example 4
1> DELETE DF1:#? ALL FORCE
deletes all the files on DF1:, even these set as not deletable.
- See also
DELETENETROUTE
Deletes a message routing path currently in use.
- Format
- DELETENETROUTE [QUIET] [DESTINATION=<ip>] [DEFAULTGATEWAY=<ip>]
- Template
- QUIET/S,DST=DESTINATION/K,DEFAULT=DEFAULTGATEWAY/K
- Location
- C:
The commands removes a route that was defined in your network. The available options are:
| QUIET | This option causes the program not to emit any error messages or progress reports. Also, if the program encounters an error it will flag this as failure code 5 which can be looked at using the "if warn" shell script command. If this option is not in effect, failure codes will be more severe and all sorts of progress information will be displayed. |
| DST or DESTINATION | The destination address of a route (or in other words, where the route to be added leads to) that should be deleted. This must be an IP address or a symbolic name. |
| DEFAULT or DEFAULTGATEWAY | The default gateway address to be deleted. This must be an IP address or a symbolic name. |
| Note |
|---|
| This command is similar to the Unix "route" command. |
| Note |
|---|
| You can try to delete a route that doesn't exist, but it will get you an error message instead of failing gracefully. |
- See also
DIR
Displays a sorted list of the files in a directory.
- Format
- [<dir|pattern>] [OPT A|I|AI|D|F] [ALL] [DIRS] [FILES] [INTER]
- [SHOWPROGRAMS] [MAXCOLUMNS <number of columns>]
- Template
- DIR,OPT/K,ALL/S,DIRS/S,FILES/S,INTER/S,SHOWPROGRAMS/S,MAXCOLUMNS/K/N
- Location
- C:
DIR displays the file and directory names contained in the specified directory, or the current directory if no name is given. Directories are listed first, followed by an alphabetical list of the files in two columns. Pressing Ctrl-C aborts a directory listing.
The options are:
| ALL | Displays all subdirectories and their files. |
| DIRS | Displays only directories. |
| FILES | Displays only files. |
| INTER | Enters an interactive listing mode.
|
| SHOWPROGRAMS | Executable programs and script files will be highlighted in the listing, by printing their names in boldfaced script. |
| MAXCOLUMNS | How many file names will be printed per line depends upon the width of the output window and the lengths of the file names. You can, however, limit how many names will be printed in each line by specifying the maximum number of columns. |
| Note |
|---|
| The ALL, DIRS, FILES and INTER keywords supersede the OPT A, D, F and I options, respectively. The older keywords are retained for compatibility with earlier versions of AmigaDOS. Do not use OPT with the full keywords--ALL, DIRS, FILES, or INTER. |
The interactive listing mode stops after each name and displays a question mark at which you can enter commands. The acceptable responses are shown below:
| Return | Displays the next name on the list. |
| E | Enters a directory; the files in that directory are displayed. |
| B | Goes back one directory level. |
| DEL or DELETE | Deletes a file or empty directory. DEL does not refer to the Del key; enter the letters D, E, and L. |
| T | Types the contents of a file. |
| C or COMMAND | Allows you to enter additional AmigaDOS commands. |
| Q | Quits interactive editing. |
| ? | Displays a list of the available interactive-mode commands. |
The COMMAND option allows almost any AmigaDOS command to be executed during the interactive directory list. When you want to issue a command, type C (or COM) at the question mark prompt. DIR will ask you for the command. Type the desired command, then press Return. The command will be executed and DIR will continue. You can also combine the C and the command on one line, by putting the command in quotes following the C.
For instance, C "type prefs.info hex" is equivalent to pressing Q to exit interactive listing mode and return to a regular Shell prompt, and typing:
1> TYPE Prefs.info HEX
The Prefs.info file would be typed to the screen in hexadecimal format.
It is dangerous to format a disk from the DIR interactive mode, as the format will take place immediately, without any confirmation requesters appearing. Also, starting another interactive DIR from interactive mode will result in garbled output.
- Example 1
1> DIR Workbench:
displays a list of the directories and files on the Workbench disk.
- Example 2
1> DIR MyDisk:#?.memo
displays all the directories and files on MyDisk that end in .memo.
- Example 3
1> DIR Extras: ALL
displays the complete contents of the Extras drawer: all directories, all subdirectories, and all files, including those in the subdirectories.
- Example 4
1> DIR Workbench: DIRS
displays only the directories on Workbench.
- Example 5
1> DIR Workbench: INTER
begins an interactive list of the contents of the Workbench disk.
- See also
DISKCHANGE
Informs the Amiga that you have changed a disk in a disk drive.
- Format
- DISKCHANGE <device>
- Template
- DRIVE/A
- Location
- C:
The DISKCHANGE command is only necessary when you are using 5.25 inch floppy disk drives or removable media drives without automatic diskchange hardware. Whenever you change the disk or cartridge of such a drive, you must use DISKCHANGE to inform the system of the switch.
DISKCHANGE can also be used if you edit a disk icon image and wish to see the new icon on the Workbench screen immediately. This is the only way to display an altered hard disk icon without rebooting.
- Example
If a requester appears and asks you to insert a new disk into your 5.25 inch drive, known as DF2:, you must insert the disk and then type:
1> DISKCHANGE DF2:
AmigaDOS then recognizes the new disk and you can proceed.
DISMOUNT
Shuts down a file system device and all its associated volumes.
- Format
- DISMOUNT <device> [SOFT] [FORCE]
- Template
- DEVICE/A,SOFT/S,FORCE/S
- Location
- C:
DISMOUNT can be used to shut down a file system device, such as "DF0:" and all its associated volumes. If the request to shut down a file system device is acknowledged, by default, it will appear as if the file system had never been mounted in the first place.
Using the SOFT keyword, will only cause the current volume to dismount, the device (and associated geometry) will remain mounted so that the next access to the device name will cause dos.library to restart the filesystem process once again, with the same characteristics as before.
The options are:
| DEVICE | This must be the name of a file system device, such as "DF0:". It is not permitted to use the name of an assignment or volume instead. |
| SOFT | This switch will cause only the volume to be dismounted, the device will remain mounted and will restart a new filesystem process upon the next access to the device name. |
| FORCE | Attempt to remove the file system device data from memory even if the file system itself is unwilling to go. This is a potentially dangerous option and should be used only as a last resort when everything else has failed. Note that this option may not succeed in cleaning up all the resources the file system may still be using. |
| Note |
|---|
| A file system device has to acknowledge the request to be shut down, which means that it might not respond to your request at all. |
DUMPDEBUGBUFFER
Dumps kernel's debug output to a shell.
- Format
- DUMPDEBUGBUFFER [<file>] [CLEAR]
- Template
- FILE,CLEAR/S
- Location
- C:
DUMPDEBUGBUFFER dumps the current content of the kernel's debug buffer to the standard output (shell). Optionally the buffer content can be saved to a file with the FILE parameter. If the CLEAR option is given, the debug buffer is cleared.
- Example 1
Print the debug buffer content:
1> DUMPDEBUGBUFFER gfx AltiVec/VMX enabled gfx PPC64xx optimizations enabled a1ide.device 53.20 (24.9.2014) [a1ide/ata_read_drive_properties] unit refused ATACMD_SET_FEATURES, SETFEATURES_EN_RLA it8212ide.device 53.20 (24.9.2014) lsi53c8xx.device 53.20 (24.9.2014) sii0680ide.device 53.20 (24.9.2014) sii3112ide.device 53.20 (24.9.2014) sii3114ide.device 53.20 (24.9.2014) sii3512ide.device 53.20 (24.9.2014) CS4281 DRIVEINIT No card present. No CMI8738 found! :-( No Envy24 found! :-( No SB128 found! :-( No SOLO_ONE found! :-( [VIA-AC97] Error: sorry, you don't seem to have the AC'97 codec! Unable to initialize Card subsystem
- Example 2
Save the debug buffer content to a file "debug.log".
1> DUMPDEBUGBUFFER "debug.log" Buffer saved as 'debug.log'
- See also
ECHO
Displays a string.
- Format
- ECHO [<string>] [NOLINE] [FIRST <n>] [LEN <n>] [TO <filename>]
- Template
- /M,LINE/S,FIRST/K/N,LEN/K/N,TO/K
- Location
- Internal
ECHO writes the specified string to the current output window or device. By default the string is sent to the screen, but if you use the TO option, you can send the string to any specified device or file.
When the NOLINE option is specified, ECHO does not automatically move the cursor to the next line after printing the string.
The FIRST and LEN options allow the echoing of a substring. FIRST <n> indicate the character position from which to begin the echo; LEN <n> indicates the number of characters of the substring to echo, beginning with the FIRST character. If the FIRST option is omitted and only the LEN keyword is given, the substring printed consists of the rightmost <n> characters of the main string. For example, if your string is 20 characters long and you specify LEN 4, the 17th, 18th, 19th and 20th characters of the string are echoed.
- Examples
1> ECHO "hello out there!"
hello out there!
1> ECHO "hello out there!" NOLINE FIRST 0 LEN 5 hello1>
For further examples using the ECHO command, see Chapter 8.
ED
Edits text files (a screen editor).
- Format
- ED [FROM] <filename> [Size <n>] [WITH <filename>] [WINDOW <window specification>] [TABS <n>] [WIDTH | COLS <n>] [HEIGHT | ROWS <n>]
- Template
- FROM/A,SIZE/N,WITH/K,WINDOW/K,TABS/N,WIDTH=COLS/N,HEIGHT=ROWS/N
- Location
- C:
See ED for more information. See Chapter 8 for an example using ED.
EDIT
Edits text files by processing the source file sequentially (a line editor).
- Format
- EDIT [FROM] <filename> [[TO <filename>] [WITH <filename>] [VER <filename>] [OPT P <lines> | W <chars> | P<lines>W<chars>] [WIDTH <chars>] [PREVIOUS <lines>]
- Template
- FROM/A,TO,WITH/K,VER/K,OPT/K,WIDTH/N,PREVIOUS/N
- Location
- C:
See EDIT for more information.
ELSE
Specifies an alternative for an IF statement in a script file.
- Format
- ELSE
- Template
- (none)
- Location
- Internal
ELSE must be used in conjunction with the IF command. ELSE is used in an IF block of a script to specify an alternative action if the IF condition is not true. If the IF condition is not true, execution of the script jumps from the IF line to the line after ELSE; all intervening commands are skipped. If the IF condition is true, the commands immediately following the IF statement are executed up to the ELSE. Then, execution skips to the ENDIF statement that concludes the IF block.
- Example
Assume a script, called Display, contains the following block:
IF exists picfile
MultiView picfile
ELSE
ECHO "picfile is not in this directory"
ENDIF
If picfile can be found in the current directory, the MultiView program is executed and picfile is displayed on the screen.
If picfile cannot be found in the current directory, the script skips to the ECHO command. The following message is displayed in the Shell window:
picfile is not in this directory
- See also
ENDCLI
Ends a Shell process.
- Format
- ENDCLI
- Template
- (none)
- Location
- Internal
ENDCLI ends a Shell process.
- See also
ENDIF
Terminates an IF block in a script file.
- Format
- ENDIF
- Template
- (none)
- Location
- Internal
ENDIF must be used when an IF commands is used. ENDIF is used in scripts at the end of an IF block. If the IF condition is not true or if the true-condition commands are executed and an ELSE is encountered, the execution of the script skips to the next ENDIF command. Every IF statement must be terminated by an ENDIF.
The ENDIF applies to the most recent IF or ELSE command.
- See also
ENDSHELL
Ends a Shell process.
- Format
- ENDSHELL
- Template
- (none)
- Location
- Internal
ENDSHELL ends a Shell process and closes the Shell window.
The Shell process can also be ended by ENDCLI, by clicking on the close gadget, or by pressing CTRL-\.
Use ENDSHELL only when the Workbench or another Shell is running. If you quit the Workbench and you close your only Shell, you cannot communicate with the Amiga without rebooting.
The Shell window cannot close if any process that were launched from the Shell and not detached are still running. Even though the window stays open, the Shell does not accept new input. You must terminate those processes before the window closes. For example, if you opened an editor from the Shell, the Shell window does not close until you exit the editor.
For examples using the ENDSHELL command, see Chapter 8.
ENDSKIP
Terminates a SKIP block in a script file.
- Format
- ENDSKIP
- Template
- (none)
- Location
- Internal
ENDSKIP is used in scripts to terminate the execution of a SKIP block. A SKIP block allows you to jump over intervening commands if a certain condition is met. When an ENDSKIP is encountered, execution of the script resumes at the line following the ENDSKIP. The condition flag is set to 5 (WARN).
- See also
EVAL
Evaluates integer or Boolean expressions.
- Format
- EVAL <value1> {[<operation>] [<value2>]} [TO <file>] [LFORMAT=<string>]
- Template
- VALUE1/A,OP,VALUE2/M,TO/K,LFORMAT/K
- Location
- C:
EVAL is used to evaluate and print the answer of an integer expression. The fractional portion of input values and final results, if any, is truncated (cut off). If a non-integer is given as an input value, evaluation stops at the decimal point.
<Value1> and <value2> can be decimal (the default), hexadecimal, or octal numbers. Hexadecimal numbers are indicated by either a leading Ox or #x. Octal numbers are indicated by either a leading 0 or a leading #. Alphabetical characters are indicated by a leading single quotation mark (`) and are evaluated as their ASCII equivalent.
The LFORMAT keyword specifies the formatting string used to print the answer. You can use %X (hexadecimal), %O (octal), %N (decimal), or %C (character). The %X and %O options require a number of digits using the LFORMAT keyword, you can specify to print a new line by including *N in your string.
The supported operations and their corresponding symbols are shown in the following table.
| addition | + |
| subtraction | - |
| multiplication | * |
| division | / |
| modulo | mod, M, m, or % |
| bitwise AND | & |
| bitwise OR | | |
| bitwise NOT | ~ |
| left shift | Ish, L, or l |
| right shift | rsh, R, or r |
| negation | - |
| exclusive OR | xor, X, or x |
| bitwise equivalence | eqv, E, or e |
EVAL can be used in scripts as a counter for loops. In that case, use the TO option to send the output of EVAL to a file.
Parentheses can be used in the expressions.
- Example 1
1> EVAL 64 / 8 + 2 10
- Example 2
1> EVAL 0x5f / 010 LFORMAT="The answer is %X4*N" The answer is 000B 1>
This divides hexadecimal 5f (95) by octal 10 (8), yielding 000B, the integer portion of the decimal answer 11.875. (The 1> prompt appears immediately after the 000B if *N is not specified in the LFORMAT string.)
For more examples using the EVAL command, see Chapter 8.
EXECUTE
Executes a script with optional argument substitution.
- Format
- EXECUTE <script> [{<arguments>}]
- Template
- FILE/A/F
- Location
- C:
EXECUTE is used to run scripts of AmigaDOS commands. The lines in the script are executed just as if they had been typed at a Shell prompt. If the s protection bit of a file is set and the file is in the search path, you only need to type the filename--the EXECUTE command is not needed.
You can use parameter substitution in scripts by including special keywords in the script. When these keywords are used, you can pass variables to the script by including the variable in the EXECUTE command line. Before the script is executed, AmigaDOS checks the parameter names in the script against any arguments given on the command line. If any match, AmigaDOS substitutes the values you specified on the command line for the parameter name in the script. You can also specify default values for AmigaDOS to use if no variables are given. If you have not specified a variable, and there is no default specified in the script, then the value of the parameter is empty (no substitution is made). EXECUTE is generally made resident during the startup-sequence.
The permissible keywords for parameter substitution are explained below. Each keyword must be prefaced with a dot character (.).
The .KEY (or .K) keyword specifies both keyword names and positions in a script. It tells EXECUTE how many parameters to expect and how to interpret them. In other words, .KEY serves as a template for the parameter values you specify. Only one .KEY statement is allowed per script. If present, it should be the first line in the file.
The arguments on the .KEY line can be given with the /A and /K directives, which work the same as in an AmigaDOS template. Arguments followed by /A are required; arguments followed by /K require the name of that argument as a keyword. For example, if a script starts with .KEY filename/A it indicates that a filename must be given on the EXECUTE command line after the name of the script. This filename will be substituted in subsequent lines of the script. For instance, if the first line of a script is:
.KEY filename/A, TOname/K
You must specify a filename variable. The TOname variable is optional, but if specified the TOname keyword must be used. For instance:
1> EXECUTE Script Textfile TOname NewFile
Before execution, AmigaDOS scans the script for any items enclosed by BRA and KET characters (< and >). Such items may consist of a keyword or a keyword and a default value. Wherever EXECUTE finds a keyword enclosed in angle brackets, it tries to substitute a parameter. However, if you want to use a string in your script file that contains angle brackets, you will have to define substitute "bracket" characters with the .BRA and .KET commands. .BRA <ch> changes the opening bracket character to <ch>, while .KEY changes the closing bracket character to <ch>. For example:
.KEY filename
ECHO "This line does NOT print <angle> brackets."
.BRA {
.KET }
ECHO "This line DOES print <angle> brackets."
ECHO "The specified filename is {filename}."
would result in the following output:
1> EXECUTE script TestFile This line does NOT print brackets. This line DOES print <angle> brackets. The specified filename is TestFile.
AmigaDOS provides a number of commands that are useful in scripts, such as IF, ELSE, SKIP, LAB, and QUIT. These commands, as well as the EXECUTE command, can be nested in a script. That is, a script can contain EXECUTE commands.
To stop the execution of a script, press Ctrl-D. If you have nested script files, you can stop the set of EXECUTE commands by pressing Ctrl-C. Ctrl-D only stops the current script from executing.
The current Shell number can be referenced by the characters <$$>. This is useful in creating unique temporary files, logical assignments, and PIPE names.
- Example 1
Assume the script List contains the following:
.K filename
RUN COPY <filename> TO PRT: +
ECHO "Printing of <filename> done"
The following command:
1> EXECUTE List Test/Prg
acts as though you had typed the following commands at the keyboard:
1> RUN COPY Test/Prg TO PRT: + 1> ECHO "Printing of Test/Prg done"
- Example 2
Another example, Display, uses more of the features described above:
.Key name/A
IF EXISTS <name>
TYPE <name> NUMBER ;if the file is in the given directory, type it with line numbers
ELSE
ECHO "<name> is not in this directory"
ENDIF
The command:
1> RUN EXECUTE Display Work/Prg2
should display the Work/Prg2 file, with line numbers on the screen, if it exists on the current directory. If the file is not there, the screen displays an error message. Because of the /A, if a filename is not given on the command line after display, an error will occur.
- See also
FAILAT
Instructs a command sequence not to fail unless a given error condition is returned.
- Format
- FAILAT [<n>]
- Template
- RCLIM/N
- Location
- Internal
Commands indicate that they have failed by setting a nonzero return code. The return code, normally 5, 10, or 20, indicates the severity of the error. A return code greater than or equal to a certain limit, the fail limit, terminates a sequence of non-interactive commands (commands specified after RUN or in a script).
Use the FAILAT command to alter the fail limit RCLIM (Return Code Limit) from its initial value of 10. If you increase the limit, you indicate that certain classes of error should not be regarded as fatal and that execution of subsequent commands can proceed after the error. The argument must be a positive number. The fail limit is reset to the initial value of 10 on exit from the command sequence.
If the argument is omitted, the current fail limit is displayed.
- Example
Assume a script contains the following lines:
COPY DF0:MyFile to RAM:
ECHO "MyFile being copied."
If MyFile cannot be found, the scripts is aborted and the following message appears in the Shell window:
COPY: object not found COPY failed returncode 20:
However, if you changed the return code limit to higher than 20, the script continues even if the COPY command fails. For example, if you changed the script to read:
FAILAT 21
COPY DF0:MyFile to RAM:
ECHO "MyFile being copied."
Even if MyFile cannot be found, the script continues. The following message appears in the Shell window:
COPY: object not found MyFile being copied.
- See also
FAULT
Prints the messages for the specified error codes.
- Format
- FAULT [<error number>] [[,]<error number>[[,]<error number>...]]
- Template
- /N/M
- Location
- Internal
FAULT prints the messages corresponding to the error numbers supplied. If several error numbers are given, they can be separated by spaces or commas.
- Example
If you received an error message:
Error when opening DF1:TestFile 205
and need more information, type:
1> FAULT 205 FAULT 205: object not found
This tells you that the error occurred because TestFile could not be found on DF1:.
A complete list of error messages appears in Appendix A.
FC-CACHE
Builds FreeType font information cache files.
- Format
- FC-CACHE [ -EfrsvVh ] [ -y <sysroot> ] [ --error-on-no-fonts ] [ --force | --really-force ] [ --sysroot=<sysroot>] [ --system-only ] [ --verbose ] [ --version ] [ --help ] [ <directories> ]
- Template
- -E=--error-on-no-fonts,-f=--force,-r=--really-force,-s=--system-only,-v=--verbose,-V=--version,-h=--help,-y=--sysroot,DIRECTORY/M
- Location
- C:
FC-CACHE scans the font directories on the system and builds font information cache files for applications using fontconfig for their font handling.
If directory arguments are not given, FC-CACHE uses each directory in the current font configuration. Each directory is scanned for font files readable by FreeType. A cache is created which contains properties of each font and the associated filename. This cache is used to speed up application startup when using the fontconfig library.
| Note |
|---|
| FC-CACHE must be executed once per architecture to generate font information customized for that architecture. |
The command parameters are:
| -E or --error-on no-fonts | Raise an error if there are no fonts in <directories>. |
| -f or --force | Scan directories with apparently valid caches. |
| -r or --really-force | Erase all existing caches, then rescan. |
| -s or --system-only | Scan system-wide directories only. |
| -y or --sysroot <sysroot> | Prepend <sysroot> to all paths for scanning. |
| -v or --verbose | Display status information while busy. |
| -V or --version | Display font config version and exit. |
| -h or --help | Display command help and exit |
- See also
FC-CAT
Reads FreeType font information cache files.
- Format
- FC-CAT [ -rvVh ] [ --recurse ] [ --verbose ] [ --version ] [ --help ] [ [ <fonts-cache-2-files> ] [ <directories> ] ... ]
- Template
- -r=--recurse,-v=--verbose,-V=--version,-h=--help,FILE/M,DIRECTORY/M
- Location
- C:
FC-CAT reads the FreeType font information from cache files or related to font directories and emits it in ASCII form. The command parameters are:
| -r or --recurse | Recurse into subdirectories. |
| -v or --verbose | Be verbose. |
| -V or --version | Show version of the program and exit. |
| -h or --help | Show command help. |
- See also
FC-LIST
Lists the available FreeType fonts.
- Format
- FC-LIST [ -vqVh ] [ -f <format> ] [ --verbose ] [ --format=<format> ] [ --quiet ] [ --version ] [ --help ] [ <pattern> ] [ <element>... ]
- Template
- -v=--verbose,-q=--quiet,-V=--version,-h=--help,-f=--format,PATTERN,ELEMENT/M
- Location
- C:
FC-LIST lists TrueType fonts and styles which are available for the applications using fontconfig.
| -v or --verbose | Print verbose output of the whole font pattern for each match, or elements if any is provided. |
| -q or --quiet | Suppress all normal output. The command returns 1, if there were no font matches. |
| -V or --version | Show version of the program and exit. |
| -h or --help | Show command help and exit. |
| -f or --format | Format output according to the format specifier <format>. |
| <pattern> | If this argument is set, only fonts matching <pattern> are displayed. |
| <element> | If set, the <element> property is displayed for matching fonts. |
- Example 1
List all font faces.
1> FC-LIST
- Example 2
List font faces that cover Hindi.
1> FC-LIST :lang=hi
- Example 3
List the filename and spacing value for each font face. ":" is an empty pattern that matches all fonts.
1> FC-LIST : family style file spacing
- See also
FC-MATCH
Matches available FreeType fonts.
- Format
- FC-MATCH [ -savVh ] [ -f <format> ] [ --sort ] [ --all ] [ --verbose ] [ --format=<format> ] [ --version ] [ --help ] [ <pattern> ] [ <element>... ]
- Template
- -s=--sort,-a=--all,-v=--verbose,-V=--version,-h=--help,-f=--format,PATTERN,ELEMENT/M
- Location
- C:
FC-MATCH matches pattern (empty pattern by default) using the normal fontconfig matching rules to find the best FreeType font available. If --sort is given, the sorted list of best matching fonts is displayed. The --all option works like --sort except that no pruning is done on the list of fonts.
If any elements are specified, only those are printed. Otherwise short file name, family, and style are printed, unless verbose output is requested.
The command parameters are:
| -s or --sort | Displays sorted list of best matching fonts. |
| -a or --all | Displays sorted list of best matching fonts, but do not do any pruning on the list. |
| -v or --verbose | Print verbose output of the whole font pattern for each match, or <elements> if any is provided. |
| -V or --version | Show version of the command and exit. |
| -h or --help | Show the command help and exit. |
| -f or --format | Format output according to the format specifier <format>. |
| <pattern> | Displays fonts matching <pattern> (uses empty pattern by default). |
| <element> | If set, the element property is displayed for matching fonts. |
- See also
FDTOOL
Control and examine the current state of floppy drives.
- Format
- FDTOOL [U | UNIT <unit number>] [D | DEBUG <debug level>] [A | AUTO]
- [M | MANUAL] [C | CHECKNOW] [I | INFO] [V | VERS | VERSION]
- Template
- U=UNIT/K/N,D=DEBUG/K/N,A=AUTO/S,M=MANUAL/S,C=CHECKNOW/S,I=INFO/S,V=VERS=VERSION/S
- Location
- C:
The current state of floppy drives controlled by the a1floppy device can be externally controlled and examined with the FDTOOL. The command options are as follows:
| U or UNIT | The target floppy drive: 0 or 1. Unit number 0 is the first floppy drive and 1 is the second drive. The default unit number is 0. |
| D or DEBUG | Set the current debug level. The valid levels are between 0 and 30. The default is 0 (debugging off). |
| A or AUTO | Start auto checking. |
| M or MANUAL | Stop auto checking. |
| C or CHECKNOW | Force a single disk check. |
| I or INFO | Print information about a floppy drive and the controlling device. |
| V, VERS, or VERSION | Print the FDTOOL and a1floppy device versions. |
FDTOOL has a built-in debugging system which provides profound information on error situations. How detailed debugging information, if any, will be printed is controlled by the DEBUG argument which sets the debug level. When the debugging system is active, the debugging information is printed to the debug port (which may be serial port 0) and not to the standard output. The debug levels are:
| Level | Output type |
|---|---|
| 0 - 4 | No output. This is the default setting. |
| 5 - 10 | Fatal errors |
| 11 - 15 | Recoverable errors (retries, etc) |
| 16 - 20 | Explanatory notes about recoverable errors (reasons, etc) |
| 21 - 25 | Explanatory notes about intermediate values (good data) |
| 26 - 30 | Flow of control ("Kilroy wuz here" messages) |
To detect if the user has ejected or inserted a disk, the a1floppy device checks the disk drives regularly for any change. On every check the drive's led will light and you will hear a click from the drive's mechanism. On some drives a single check will start the drive's motor for several seconds, which will cause the motor to run continuously because of the regular checks. To prevent the drive from spinning countinuously and wearing out, the automatic disk checking can be turned off with the MANUAL option.
Note that when the automatic disk checking function is turned off, Amiga will no longer detect disk changes. In order to notify the system that a disk has been ejected or inserted, use the DISKCHANGE command or FDTOOL's CHECKNOW option.
- Example 1
Print information about the first floppy drive (unit number 0):
1> FDTOOL UNIT=0 INFO Current state of A1Floppy Drive Unit 0 Version: 53 Revision: 2 Controller state: free Debug level: 0 Task readiness state: ready Disk state: drive empty Drive status: ST0=20 ST1=00 ST2=00 ST3=38 Drive currently on cylinder 0 Drive state: Interrupt state 0 Data count 0, status count 0 Unit Open count: 2 Change number: 0 Recovered errors this disk: 1 Config word: 00000200
- Example 2
Turn off the automatic disk change detection on drive 0:
1> FDTOOL MANUAL Regular check not set on drive 0
- Example 3
Enable the automatic disk change detection on drive 0:
1> FDTOOL AUTO Starting regular check on drive 0
- Example 4
Manually check if the user has ejected or inserted a disk on drive 0:
1> FDTOOL CHECKNOW Requesting a check now on drive 0
- See also
FILENOTE
Attaches a comment to a file.
- Format
- FILENOTE [FILE] {<file|pattern>} [COMMENT] <comment> [ALL]
- [QUIET] [FILES] [DIRS]
- Template
- FILE/A/M,COMMENT/A,ALL/S,QUIET/S,FILES/S,DIRS/S
- Location
- C:
FILENOTE attaches an optional comment characters to the specified file or to all files matching the given pattern. The size of the comment is limited, which means that the <comment> argument may be truncated before it is used.
If the <comment> includes spaces, it must be enclosed in double quotes. To include double quotes in a filenote, each literal quote mark must be immediately preceded by an asterisk (*), and the entire comment must be enclosed in quotes, regardless of whether the comment contains any spaces.
To delete an existing filenote from a file, use "" as the <comment> argument.
Creating a comment with FILENOTE is the same as entering a comment into the Comment gadget of an icon's Information window. Changes made with FILENOTE will be reflected in the Information window, and vice versa.
When an existing file is copied to (specified as the TO argument of a COPY command), it will be overwritten, but its comment will be retained. Any comment attached to a FROM file will not be copied unless the CLONE or COM option of COPY is specified.
FILENOTE's options are:
| ALL | If the ALL option is given, FILENOTE will add the <comment> to all the files in the specified directory. |
| QUIET | If the QUIET option is given, screen output is suppressed. The local shell variable _Verbosity with a negative value has the same effect. |
| FILES | Only change the comments of the files found. |
| DIRS | Only change the comments of the directories found. |
| Note |
|---|
| The FILES and DIRS options work together: if you use FILES and omit DIRS, then only the files will be affected and the other way round. If none of FILES and DIRS is used, all files and directories will have their comments changed. |
- Example 1
1> FILENOTE Sonata "allegro non troppo"
attaches the filenote allegro non troppo to the Sonata file.
- Example 2
1> FILENOTE Toccata "*"presto*""
Here the filenote is "presto".
FILESIZE
Collects information on the size of files.
- Format
- FILESIZE [{<dir|file|pattern|device>}] [FORM <file name>] [ALL]
- Template
- FILES/M,FROM/K,ALL/S,REPORT/S,FORMAT/K
- Location
- C:
FILESIZE will collect information on files stored on a disk, adding up the number of bytes and blocks used, counting the number of files found. If you specify a <dir>, <pattern> or <filename> argument, FILESIZE will add the file data for the specified directory, all directories or files that match the pattern, or the specified file or device, respectively. Instead of providing the names on the command line, you can also specify the name of a file from which the names should be read.
The options are:
| FILES | A list of files, directories or wildcard patterns which should be examined. You either need to provide this parameter or the a file name with the FROM option. | ||||||||||||||||||
| FROM | The name of a text file which contains the names of files, directories or wildcard patterns which should be examined. You either need to provide this parameter or a list of names with the FILES option. | ||||||||||||||||||
| ALL | Also examines the files in all directories and subdirectories. | ||||||||||||||||||
| REPORT | Print progress reports as directory contents are scanned. Each such report will be prefixed by the name of the directory and final total number of files, blocks, bytes will be prefixed by "TOTAL". | ||||||||||||||||||
| FORMAT | Defines a string to specially format FILESIZE output. Supported format specifiers are:
The escape sequences '*E' and '*N' are expanded, too. If you do not specify a special format, FILESIZE will use "%F files, %L bytes, %B blocks" and, if the "REPORT" option is used, "%N: %F files, %L bytes, %B blocks". Output formatting follows 'C' conventions, e.g. "%10l" will print at least 10 digits for the number of bytes used, right justified. |
- Example 1
Examine the contents of the C: directory, adding up the sizes of all files found, then print just the number of bytes used:
1> FILESIZE C: FORMAT "%l" 1958872
- Example 2
Same as above, but print the size as a rounded number. Note that a Kilobyte is worth 1024 bytes (and not 1000).
1> FILESIZE C: FORMAT "%s" 1912K
- Example 3
Find out how many files are stored in the LIBS: directory:
1> FILESIZE LIBS: ALL FORMAT "%F files found" 178 files found
- Example 4
Print reports on the individual directories found on SYS:
1> FILESIZE SYS:#? ALL REPORT SYS:C: 71 files, 354,230 bytes, 722 blocks SYS:Classes: 49 files, 786,244 bytes, 1,560 blocks SYS:Devs: 278 files, 1,734,474 bytes, 3,502 blocks SYS:Expansion: 0 files, 0 bytes, 0 blocks SYS:Fonts: 62 files, 777,024 bytes, 1,554 blocks SYS:L: 10 files, 106,488 bytes, 215 blocks SYS:Libs: 73 files, 2,147,780 bytes, 4,232 blocks SYS:Prefs: 585 files, 14,115,024 bytes, 27,836 blocks SYS:Rexxc: 10 files, 4,628 bytes, 13 blocks SYS:S: 19 files, 14,100 bytes, 38 blocks SYS:Storage: 292 files, 1,408,042 bytes, 2,868 blocks SYS:System: 16 files, 154,916 bytes, 310 blocks SYS:T: 0 files, 0 bytes, 0 blocks SYS:Tools: 49 files, 686,316 bytes, 1,364 blocks SYS:Utilities: 88 files, 2,267,465 bytes, 4,470 blocks SYS:WBStartup: 11 files, 257,923 bytes, 509 blocks SYS:Locale: 460 files, 2,581,114 bytes, 5,295 blocks TOTAL: 2,082 files, 27,422,060 bytes, 54,545 blocks
FLASHTOOL
Reading, writing, and erasing for EEPROM memory chips.
- Format
- FLASHTOOL <command> [<command arguments>]
- Template
- COMMAND,ARGS/M
- Location
- C:
FLASHTOOL is used for reading, erasing, and writing to EEPROM non-volatile memory chips. To utilize FLASHTOOL, an IDE Flasher must be installed in the primary or secondary IDE port.
FLASHTOOL provides the following commands:
| Name | Command | Description |
|---|---|---|
| ISPRESENT | -p <device name> <unit> | Check if a flasher device is present. |
| TYPE | -t <device name> <unit> | Return EEPROM type. |
| ERASE | -e <device name> <unit> | Erase an EEPROM. |
| ISBLANK | -b <device name> <unit> | Check if EEPROM is empty. |
| SAVE | -s <device name> <unit> <file name> | Save EEPROM content to a file. The saved file is in binary (raw) format. |
| WRITE | -w <device name> <unit> <file name> | Write a binary (raw) file to EEPROM. |
| VERIFY | -c <device name> <unit> <file name> | Check if EEPROM content matches the file's content. The file must be in binary (raw) form. |
| LISTSUPPORTED | -l | List supported EEPROMs. |
| VERSION | -v | Print FLASHTOOL version. |
The <device name> argument tells which Amiga device is controlling the IDE Flasher, and the <unit> argument tells which device is used.
FLASHTOOL supports the following EEPROMs:
- ATMEL AT29C512 512 Kbit (64K x 8-bit)
- ATMEL AT29C010A 1 Mbit (128K x 8-bit)
- ATMEL AT29C020 2 Mbit (256K x 8-bit)
- ATMEL AT29C040 4 Mbit (512K x 8-bit)
- ATMEL AT29C040A 4 Mbit (512K x 8-bit)
- ATMEL AT49F004N 4 Mbit (512K x 8-bit)
- ATMEL AT49F004T 4 Mbit (512K x 8-bit)
- ATMEL AT49F010 1 Mbit (128K x 8-bit)
- ATMEL AT49F020 2 Mbit (256K x 8-bit)
- AMD AM29F010 1 Mbit (128K x 8-bit)
- AMD AM29F010A 1 Mbit (128K x 8-bit)
- AMD AM29F040B 4 Mbit (512K x 8-bit)
- AMD AM29F002 2 Mbit (256K x 8-bit) Top Boot Block
- AMD AM29F002 2 Mbit (256K x 8-bit) Bottom Boot Block
- AMD AM29F004 4 Mbit (512K x 8-bit) Top Boot Block
- AMD AM29F004 4 Mbit (512K x 8-bit) Bottom Boot Block
- MOSEL VITELIC V29C51000T 512 Kbit (64K x 8-bit)
- MOSEL VITELIC V29C51000B 512 Kbit (64K x 8-bit)
- MOSEL VITELIC V29C51001T 1 Mbit (128K x 8-bit)
- MOSEL VITELIC V29C51001B 1 Mbit (128K x 8-bit)
- MOSEL VITELIC V29C51002T 2 Mbit (256K x 8-bit)
- MOSEL VITELIC V29C51002B 2 Mbit (256K x 8-bit)
- MOSEL VITELIC V29C51004T 4 Mbit (512K x 8-bit)
- MOSEL VITELIC V29C51004B 4 Mbit (512K x 8-bit)
- HYUNDAI HY29F002T 2 Mbit (256K x 8-bit)
- HYUNDAI HY29F002B 2 Mbit (256K x 8-bit)
- HYUNDAI HY29F040A 4 Mbit (512K x 8-bit)
- SST SST29EE512 512 Kbit (64K x 8-bit)
- SST SST29EE010 1 Mbit (128K x 8-bit)
- SST SST29EE020 2 Mbit (256K x 8-bit)
- SST SST39SF512 512Kbit (64K x 8-bit)
- SST SST39SF010(A) 1 Mbit (128K x 8-bit)
- SST SST39SF020A 2 Mbit (256K x 8-bit)
- SST SST39SF040 4 Mbit (512K x 8-bit)
- ST M29F010B 1 Mbit (128K x 8-bit)
- ST M29F002T 1 Mbit (256K x 8-bit)
- ST M29F002B 1 Mbit (256K x 8-bit)
- ST M29F040B 4 Mbit (512K x 8-bit)
- ST M29F040 4 Mbit (512K x 8-bit)
- WINBOND W29C512A 512 Kbit (64K x 8-bit)
- WINBOND W29C010M 1 Mbit (128K x 8-bit)
- WINBOND W29C020 2 Mbit (256K x 8-bit)
- WINBOND W29C040 4 Mbit (512K x 8-bit)
- WINBOND W49C020 2 Mbit (256K x 8-bit)
- WINBOND W49F002U 2 Mbit (256K x 8-bit)
- WINBOND W49F002U mod 2 Mbit (256K x 8-bit)
- MACRONIX MX29F040 4 Mbit (512K x 8-bit)
- AMIC A29010 1 Mbit (128K x 8-bit)
- AMIC A29040A 4 Mbit (512K x 8-bit)
- AMIC A29001T 1 Mbit (128K x 8-bit)
- AMIC A29001B 1 Mbit (128K x 8-bit)
- AMIC A29002T 2 Mbit (256K x 8-bit)
- AMIC A29002B 2 Mbit (256K x 8-bit)
- Texas Instruments TMS29F040 4 Mbit (512K x 8-bit)
- IMT IM29F001T 1 Mbit (128K x 8-bit)
- IMT IM29F001B 1 Mbit (128K x 8-bit)
- IMT IM29F002T 2 Mbit (256K x 8-bit)
- IMT IM29F002B 2 Mbit (256K x 8-bit)
- IMT IM29F004T 4 Mbit (512K x 8-bit)
- IMT IM29F004B 4 Mbit (512K x 8-bit)
- Fujitsu MBM29F002TC 2 Mbit (256K x 8-bit)
- Fujitsu MBM29F002BC 2 Mbit (256K x 8-bit)
- Fujitsu MBM29F004TC 4 Mbit (512K x 8-bit)
- Fujitsu MBM29F004BC 4 Mbit (512K x 8-bit)
- Fujitsu MBM29F040C 4 Mbit (512K x 8-bit)
- Example 1
Check if an IDE Flasher device is installed:
1> FLASHTOOL -p a1ide.device 0
- Example 2
Erase an EEPROM:
1> FLASHTOOL -e a1ide.device 0
- Example 3
Write file "uboot.bin" to EEPROM:
1> FLASHTOOL -w a1ide.device 0 uboot.bin
- Example 4
Verify the written data:
1> FLASHTOOL -c a1ide.device 0 uboot.bin
- Example 5
Save EEPROM content to file "backup.bin":
1> FLASHTOOL -s a1ide.device 0 backup.bin
FOREACH
Executes a script for each file encountered.
- Format
- FOREACH {<file|pattern>} [PATH <path name>] {<name>} [FROM <number>] [TO <number>]
- [STEP <number>] [SCRIPT <name>] [COM "<command string>"] [WITH <name>] [ALL]
- [FILES] [DIRS] [SORT] [SINCE <date>] [UPTO <date>]
- Template
- NAME,PATH/K,IN/M,FROM/K/N,TO/K/N,STEP/K/N,SCRIPT/K,COM/K,WITH/K,ALL/S,FILES/S,DIRS/S,SORT/S,SINCE/K,UPTO/K
- Location
- C:
The FOREACH command allows you to loop within scripts with a loop variable set to a value selected from a list of names. FOREACH will execute a script of your choice; if no script is given, the FOREACH command allows you to type a temporary one in from the command line. If used from within a script, the FOREACH command will loop within the script.
The FOREACH loop is bounded by a END directive (or an EOF, or a control-\).
The FOREACH loop is executed once for each name specified by the IN keyword. Full pattern matching is supported. Names specified with the IN option don't necessarily have to actually exist as files or directories to be used, which allows you to create files.
The NAME keyword allows you to pick a variable name; each time through the loop, that variable is set to the name currently selected from the list of names specified with the IN keyword.
If no name is specified, no local variables will be created.
The PATH keyword allows you to select a local variable name where the PATH will be stored; if no PATH keyword is specified, this will be stored in a variable with the same name as NAME but with .PATH appended.
The basename and extension local variables work in a similar manner, except that the names are always based on the name specied by the NAME keyword with an appended extension. The extension for the basename of the file found is .BASE The extension (if any) will be found in the variable name with the .EXT extension.
The nametype local variable contains the type of thing, either dir (for directory), file (for file), or name (for couldn't find one of those).
Remember, to access variables that contain non-alphanumeric characters (like a .) on the command line (like a .) you have to surround the name with { } like: ${i.base}
The ALL keyword causes any pattern matching used in any member of the IN namelist to be recursive.
The FILES keyword is a 'files only' keyword. When this is used, only files (non-directories) will be selected from the list of IN names.
The DIRS keyword is a 'directories only' keyword. When this is used, only directories (non-files) will be selected from the list of IN names.
In either the file only or the directory only mode all names which are neither files or directories (ie names that don't exist) are selected as well.
Even if the FILES only keyword is used, if the ALL option is specified, directories _will_ be entered.
| Note |
|---|
| Directories are listed _last_ after all files (and/or subdirectories) in them are used. This allows the FOREACH command to be used as an interactive Delete command. |
The COM keyword allows you to specify a single command to execute. Remember to use quotes around the entire command; if one of the arguments inside requires quotes, you must escape those quotes using the *. Within the COM argument, all variables must be preceeded by an additional $, to avoid expansion on the command line before the command is executed. By using *N within the COM string, you can define multi-command COM arguments, which is especially useful when making aliases that use the FOREACH command.
The SCRIPT keyword allows you to specify a script file to execute. If no script keyword is used (and no COM keyword is specified) you will be prompted to create a temporary script.
The WITH keyword allows you to specify a file containing a list of names. This list is used after any command line names are used.
The FROM, TO and (optional) STEP keywords allow you to specify a numeric range; the loop variable will be set to each of the values in the range in turn. Both are required to be specified to use this feature. The STEP keyword is optional; it allows you to pick an increment other than 1. FROM, TO, and STEP can be negative. STEP cannot be zero, however.
The SORT keyword causes the FOREACH command to do an alphanumeric sort on the name list before doing any script execution.
The SINCE and UPTO keywords are for date comparisons; SINCE will limit operations to files/directories since (and including) the specified date/time. UPTO will limit operations to files/directories up to (and including) the specified date/time. The usual AmigaDOS shortcuts (today, yesterday, and so on) are allowed.
The FOREACH command nests. WARNING: The same variable name should not be used for nested FOREACH commands; make sure the inner loop variable name is not the same as the outside loop variable name.
The FOREACH command places its temporary files in T:. If T: is not assigned then RAM: is used instead.
- Bugs
It is sometimes hard to stop the FOREACH command from the Shell. Many things are looking at the signal bits, and the FOREACH command is low on the chain. It is often easier to go to another Shell, use STATUS to find out the process number of the FOREACH command, and send that process a BREAK ALL. Like this, for instance:
1> BREAK `STATUS com=foreach` all
- Example 1
foreach i in qwe1 qwe2 ram:#$
echo "file is $i, path is ${i.path}"
foreach j in test1 test2
echo "subname is $j"
echo "Current local vars are:"
set
end
end
- Example 2
Here's a handy alias using FOREACH that gives an interactive delete command. Note: The alias must be defined on one line. It is shown on two lines for clarity.
1> alias del foreach i []
com "failat 21*Nask *"delete $i ?*"*N if warn *Ndelete ${i.path}$i*N endif"
- Example 3
Rename all the .a files to .asm.
foreach i in #?.a
rename $i ${i.base}.asm
end
FS_PLUGIN_CACHE
Increases performance of a FFS2 file system.
- Format
- FS_PLUGIN_CACHE <device name> [ CACHESIZE=<cache size>] [ READAHEAD=<blocks>]
- [ MEMLIMIT=<limit> ] [ QUIET ] [ WRITEAROUND ] [ NOCHECKSUM ]
- Template
- DEVICE/A,S=CACHESIZE/K/N,R=READAHEAD/K/N,MEMLIMIT/K/N,QUIET/S,WA=WRITEAROUND/S,NC=NOCHECKSUMS/S
- Location
- C:
FS_PLUGIN_CACHE starts a FastFileSystem 2 (FFS2) cache plug-in on a device <device name>. The plug-in will increase file system performance by buffering disk data that was accessed before and might be accessed again, or which was never accessed before but has a good chance of being needed soon.
You can tell the plug-in how large the cache should become that it is supposed to maintain. By default it will try to use cache about 1% the size of the device it is installed on. You can override this number with the CACHESIZE parameter. The size you specify will be multiplied by 1024. Thus, a cache size of 8192 would result in a cache size of 8 MB.
The cache plug-in supports also a feature called read-ahead. With this feature enabled, the file system will always read a little more data than is strictly necessary in the hope that the data read will be useful later. You can tell the file system how many blocks should be read using the READAHEAD parameter. Note that a read-ahead cache makes sense only if reading the extra data does not noticeably increase the overhead of transferring data from the disk. Thus, smaller read-aheads sizes are likely to be more successful than larger ones.
The other command options are:
| MEMLIMIT | Missing description. |
| QUIET | Missing description. |
| WRITEAROUND or WA | Missing description. |
| NOCHECKSUMS or NC | Missing description. |
Missing examples.
FS_PLUGIN_ENCRYPT
Enables FFS2 file system's data encryption.
- Format
- FS_PLUGIN_ENCRYPT <device name> [ BLOCKS=<blocks> ] [ QUIET ]
- Template
- DEVICE/A,BLOCKS/K/N,QUIET/S
- Location
- C:
FS_PLUGIN_ENCRYPT starts a FastFileSystem 2 (FFS2) data encryption plug-in on a device <device name>. The plug-in performs on the fly data encryption and decryption on the device it works.
The plug-in begins by asking you for a password to use for encryption. Enter your password and press Enter to begin. Note that you can abort the password entry by pressing Ctrl-C.
Your password will be used to set up a block cipher algorithm by the name of Blowfish. Next, the file system will be taken out of service temporarily, the plug-in will be installed and the file system will be reactivated. If you entered the correct password, the file system will suddenly start to make sense of the encrypted data.
| Note |
|---|
| You have to reformat a file system with the encryption plug-in installed in order to use it. |
The FFS2 file system's block transform plug-in feature permits you to cascade plug-ins. That is, you can set up several plug-ins with different passwords on the same device. Note that the order in which the plug-ins are set up defines the order in which the encryption will be applied. When you want to access your data later, you will have to set up the different encryptions in exactly the same order again.
There are two further parameters for the FS_PLUGIN_ENCRYPT command in addition to the mandatory DEVICE parameter. Using the BLOCKS parameter you can tell the file system how many data blocks it should try to encrypt at a time. The more blocks it uses, the faster it can encrypt data to be written to disk. The QUIET parameter tells the plug-in not to announce what it is about to do, except for printing error messages and prompting you to enter the password.
- Warning
Do not forget you password! The Blowfish cipher is hard to break, and it does not get any easier because the password does not go directly into the cipher algorithm.
FS_SET_FLUSH_STRATEGY
Changes volume's flushing strategy.
- Format
- FS_SET_FLUSH_STRATEGY [ <volume name> ] [ <strategy> ]
- Template
- VOLUME,STRATEGY/N
- Location
- C:
The FS_SET_FLUSH_STRATEGY command can be used for changing the flush strategy of a volume <volume name>.
Whenever changes are made to the contents of a FastFileSystem 2 (FFS2) file system, the file system data structures may need to be updated. The updating process can involve changing several disk data blocks. If this process is interrupted, the data on the disk may no longer be consistent and require repairs. The FastFileSystem 2 tries hard not to leave the disk's data structures in an inconsistent state when changes are made. Unfortunately, for this goal to be reached, the data block manipulations have to be carried out in a certain order, and the changes need to be written back to disk at once. This takes time and has a negative impact on write performance.
If you are certain that you can do without this elaborate and slow data management scheme, you can change the file system's data flushing strategy. The default is "strict", which means that for each change made, the respective data block changes are immediately written back ("flushed") to disk. The alternative is the "relaxed" strategy, which will delay writing back block changes until either no disk activity has taken place in a while or further block changes are making it necessary to write older modified blocks back to disk. The relaxed strategy is generally faster, but also generally less reliable than the strict one.
The VOLUME parameter tells which FFS2 formatted volume's flushing strategy will be displayed or changed and the STRATEGY parameter which strategy will be selected. Value of 0 chooses the strict flushing strategy and 1 chooses the relaxed strategy. If you leave out the STRATEGY parameter, FS_SET_FLUSH_STRATEGY displays the current flushing strategy of the supplied volume.
- Example 1
Display volume's "Workbench" current flushing strategy.
1> FS_SET_FLUSH_STRATEGY Workbench: 'Workbench:' flush strategy = strict (was strinct).
- Example 2
Select "relaxed" flushing strategy for volume "Workbench".
1> FS_SET_FLUSH_STRATEGY Workbench: 1 'Workbench:' flush strategy = relaxed (was strinct).
FTP
ARPANET file transfer program.
- Format
- FTP [-v|VERBOSE] [-d|DEBUG] [-t|TRACE] [-i|NOPROMPT] [-n|NOAUTOLOGIN] [-g|NOGLOBBING] [<host>] [<n>]
- Template
- -v=VERBOSE/S,-d=DEBUG/S,-t=TRACE/S,-i=NOPROMPT/S,-n=NOAUTOLOGIN/S,-g=NOGLOBBING/S,HOST,PORT/N
- Location
- C:
FTP is the user interface to the ARPANET standard File Transfer Protocol. The program allows a user to transfer files to and from a remote network site.
Options may be specified at the command line, or to the command interpreter.
| -v or VERBOSE | Verbose option forces FTP to show all responses from the remote server, as well as report on data transfer statistics. |
| -n or NOAUTOLOGIN | Restrains FTP from attempting "auto-login" upon initial connection. If auto-login is enabled, FTP will check the .netrc (see below) file in the user's home directory for an entry describing an account on the remote machine. If no entry exists, FTP will prompt for the remote machine login name (default is the user identity on the local machine), and, if necessary, prompt for a password and an account with which to login. |
| -i or NOPROMPT | Turns off interactive prompting during multiple file transfers. |
| -d or DEBUG | Enables debugging. |
| -g or NOGLOBBING | Disables file name globbing. |
The client host with which FTP is to communicate may be specified on the command line. If this is done, FTP will immediately attempt to establish a connection to an FTP server on that host; otherwise, FTP will enter its command interpreter and await instructions from the user. When FTP is awaiting commands from the user the prompt "ftp>" is provided to the user. The following commands are recognized by FTP:
| $ <macro-name> [<args>] | Execute the <macro macro-name> that was defined with the macdef command. Arguments are passed to the macro unglobbed. |
| account [<passwd>] | Supply a supplemental password required by a remote system for access to resources once a login has been successfully completed. If no argument is included, the user will be prompted for an account password in a non-echoing input mode. |
| append <local-file> [<remote-file>] | Append a local file to a file on the remote machine. If remote-file is left unspecified, the local file name is used in naming the remote file after being altered by any ntrans or nmap setting. File transfer uses the current settings for type, format, mode, and structure. |
| ascii | Set the file transfer type to network ASCII. This is the default type. |
| bell | Arrange that a bell be sounded after each file transfer command is completed. |
| binary | Set the file transfer type to support binary image transfer. |
| bye | Terminate the FTP session with the remote server and exit FTP. An end of file will also terminate the session and exit. |
| case | Toggle remote computer file name case mapping during mget commands. When case is on (default is off), remote computer file names with all letters in upper case are written in the local directory with the letters mapped to lower case. |
| cd <remote-directory> | Change the working directory on the remote machine to <remote-directory>. |
| cdup | Change the remote machine working directory to the parent of the current remote machine working directory. |
| chmod <mode> <file-name> | Change the permission modes of the file <file-name> on the remote system to <mode>. |
| close | Terminate the FTP session with the remote server, and return to the command interpreter. Any defined macros are erased. |
| cr | Toggle carriage return stripping during ascii type file retrieval. Records are denoted by a carriage return/linefeed sequence during ascii type file transfer. When cr is on (the default), carriage returns are stripped from this sequence to conform with the UNIX single linefeed record delimiter. Records on non-UNIX remote systems may contain single linefeeds; when an ascii type transfer is made, these linefeeds may be distinguished from a record delimiter only when cr is off. |
| delete <remote-file> | Delete the file <remote-file> on the remote machine. |
| debug [<debug-value>] | Toggle debugging mode. If an optional debug value is specified it is used to set the debugging level. When debugging is on, FTP prints each command sent to the remote machine, preceded by the string "-->" |
| dir [<remote-directory>] [<local-file>] | Print a listing of the directory contents in the directory, <remote-directory>, and, optionally, placing the output in <local-file>. If interactive prompting is on, FTP will prompt the user to verify that the last argument is indeed the target local file for receiving dir output. If no directory is specified, the current working directory on the remote machine is used. If no local file is specified, or local-file is -, output comes to the terminal. |
| disconnect | A synonym for close. |
| form <format> | Set the file transfer form to <format>. The default format is "file". |
| get <remote-file> [<local-file>] | Retrieve the <remote-file> and store it on the local machine. If the local file name is not specified, it is given the same name it has on the remote machine, subject to alteration by the current case, ntrans, and nmap settings. The current settings for type, form, mode, and structure are used while transferring the file. |
| glob | Toggle filename expansion for mdelete, mget and mput. If globbing is turned off with glob, the file name arguments are taken literally and not expanded. Globbing for mput is done as in csh(1). For mdelete and mget, each remote file name is expanded separately on the remote machine and the lists are not merged. Expansion of a directory name is likely to be different from expansion of the name of an ordinary file: the exact result depends on the foreign operating system and FTP server, and can be previewed by doing "mls remote-files -" Note: mget and mput are not meant to transfer entire directory subtrees of files. That can be done by transferring a tar(1) archive of the subtree (in binary mode). |
| hash | Toggle hash-sign ("#") printing for each data block transferred. The size of a data block is 1024 bytes. |
| help [<command>] | Print an informative message about the meaning of command. If no argument is given, FTP prints a list of the known commands. |
| idle [<seconds>] | Set the inactivity timer on the remote server to seconds seconds. If seconds is omitted, the current inactivity timer is printed. |
| lcd [<directory>] | Change the working directory on the local machine. If no directory is specified, the user's home directory is used. |
| ls [<remote-directory>] [<local-file>] | Print a listing of the contents of a directory on the remote machine. The listing includes any system-dependent information that the server chooses to include; for example, most UNIX systems will produce output from the command "ls -l". (See also nlist.) If remote directory is left unspecified, the current working directory is used. If interactive prompting is on, FTP will prompt the user to verify that the last argument is indeed the target local file for receiving ls output. If no local file is specified, or if <local-file> is "-", the output is sent to the terminal. |
| macdef <macro-name> | Define a macro. Subsequent lines are stored as the macro <macro-name>; a null line (consecutive newline characters in a file or carriage returns from the terminal) terminates macro input mode. There is a limit of 16 macros and 4096 total characters in all defined macros. Macros remain defined until a close command is executed. The macro processor interprets "$" and "\" as special characters. A "$" followed by a number (or numbers) is replaced by the corresponding argument on the macro invocation command line. A "$" followed by an "i" signals that macro processor that the executing macro is to be looped. On the first pass "$i" is replaced by the first argument on the macro invocation command line, on the second pass it is replaced by the second argument, and so on. A "\" followed by any character is replaced by that character. Use the "\" to prevent special treatment of the "$". |
| mdelete [<remote-files>] | Delete the <remote-files> on the remote machine. |
| mdir <remote-files> <local-file> | Like dir, except multiple remote files may be specified. If interactive prompting is on, FTP will prompt the user to verify that the last argument is indeed the target local file for receiving mdir output. |
| mget <remote-files> | Expand the <remote-files> on the remote machine and do a get for each file name thus produced. See glob for details on the filename expansion. Resulting file names will then be processed according to case, ntrans, and nmap settings. Files are transferred into the local working directory, which can be changed with "lcd directory"; new local directories can be created with "! mkdir directory". |
| mkdir <directory-name> | Make a directory on the remote machine. |
| mls <remote-files> <local-file> | Like nlist, except multiple remote files may be specified, and the <local-file> must be specified. If interactive prompting is on, FTP will prompt the user to verify that the last argument is indeed the target local file for receiving mls output. |
| mode [<mode-name>] | Set the file transfer mode to <mode-name>. The default mode is "stream" mode. |
| modtime <file-name> | Show the last modification time of the file on the remote machine. |
| mput <local-files> | Expand wild cards in the list of local files given as arguments and do a put for each file in the resulting list. See glob for details of filename expansion. Resulting file names will then be processed according to ntrans and nmap settings. |
| newer <file-name> | Get the file only if the modification time of the remote file is more recent that the file on the current system. If the file does not exist on the current system, the remote file is considered newer. Otherwise, this command is identical to get. |
| nlist [<remote-directory>] [<local-file>] | Print a list of the files in a directory on the remote machine. If remote directory is left unspecified, the current working directory is used. If interactive prompting is on, FTP will prompt the user to verify that the last argument is indeed the target local file for receiving nlist output. If no local file is specified, or if local-file is -, the output is sent to the terminal. |
| nmap [<inpattern> <outpattern>] | Set or unset the filename mapping mechanism. If no arguments are specified, the filename mapping mechanism is unset. If arguments are specified, remote filenames are mapped during mput commands and put commands issued without a specified remote target filename. If arguments are specified, local filenames are mapped during mget commands and get commands issued without a specified local target filename. This command is useful when connecting to a non-UNIX remote computer with different file naming conventions or practices. The mapping follows the pattern set by <inpattern> and <outpattern>. <inpattern> is a template for incoming filenames (which may have already been processed according to the ntrans and case settings). Variable templating is accomplished by including the sequences "$1", "$2", ..., "$9" in <inpattern>. Use "\" to prevent this special treatment of the "$" character. All other characters are treated literally, and are used to determine the nmap [<inpattern>] variable values. For example, given inpattern $1.$2 and the remote file name "mydata.data", $1 would have the value "mydata", and $2 would have the value "data". The <outpattern> determines the resulting mapped filename. The sequences "$1", "$2", ...., "$9" are replaced by any value resulting from the inpattern template. The sequence "$0" is replace by the original filename. Additionally, the sequence "[seq1, seq2]" is replaced by [seq1] if seq1 is not a null string; otherwise it is replaced by seq2. For example, the command
would yield the output filename "myfile.data" for input filenames "myfile.data" and "myfile.data.old", "myfile.file" for the input filename "myfile", and "myfile.myfile" for the input filename ".myfile". Spaces may be included in <outpattern>, as in the example: nmap $1 sed "s/ *$//" > $1. Use the "\" character to prevent special treatment of the "$",'[','[', and "," characters. |
| ntrans [<inchars> [<outchars>]] | Set or unset the filename character translation mechanism. If no arguments are specified, the filename character translation mechanism is unset. If arguments are specified, characters in remote filenames are translated during mput commands and put commands issued without a specified remote target filename. If arguments are specified, characters in local filenames are translated during mget commands and get commands issued without a specified local target filename. This command is useful when connecting to a non-UNIX remote computer with different file naming conventions or practices. Characters in a filename matching a character in <inchars> are replaced with the corresponding character in <outchars>. If the character's position in <inchars> is longer than the length of <outchars>, the character is deleted from the file name. |
| open <host> [<port>] | Establish a connection to the specified host FTP server. An optional port number may be supplied, in which case, FTP will attempt to contact an FTP server at that port. If the auto-login option is on (default), FTP will also attempt to automatically log the user in to the FTP server (see below). |
| passive | Toggle passive mode. If passive mode is turned on (default is off), the FTP client will send a PASV command for all data connections instead of the usual PORT command. The PASV command requests that the remote server open a port for the data connection and return the address of that port. The remote server listens on that port and the client connects to it. When using the more traditional PORT command, the client listens on a port and sends that address to the remote server, who connects back to it. Passive mode is useful when using FTP through a gateway router or host that controls the directionality of traffic. (Note that though FTP servers are required to support the PASV command by RFC 1123, some do not.) |
| prompt | Toggle interactive prompting. Interactive prompting occurs during multiple file transfers to allow the user to selectively retrieve or store files. If prompting is turned off (default is on), any mget or mput will transfer all files, and any mdelete will delete all files. |
| proxy <ftp-command> | Execute an FTP command on a secondary control connection. This command allows simultaneous connection to two remote FTP servers for transferring files between the two servers. The first proxy command should be an open, to establish the secondary control connection. Enter the command "proxy ?" to see other FTP commands executable on the secondary connection. The following commands behave differently when prefaced by proxy: open will not define new macros during the auto-login process, close will not erase existing macro definitions, get and mget transfer files from the host on the primary control connection to the host on the secondary control connection, and put, mput, and append transfer files from the host on the secondary control connection to the host on the primary control connection. Third party file transfers depend upon support of the FTP protocol PASV command by the server on the secondary control connection. |
| put <local-file> [<remote-file>] | Store a local file on the remote machine. If <remote-file> is left unspecified, the local file name is used after processing according to any ntrans or nmap settings in naming the remote file. File transfer uses the current settings for type, format, mode, and structure. |
| pwd | Print the name of the current working directory on the remote machine. |
| quit | A synonym for bye. |
| quote <arg1> <arg2> ... | The arguments specified are sent, verbatim, to the remote FTP server. |
| recv <remote-file> [<local-file>] | A synonym for get. |
| reget <remote-file> [<local-file>] | Reget acts like get, except that if <local-file> exists and is smaller than <remote-file>, <local-file> is presumed to be a partially transferred copy of <remote-file> and the transfer is continued from the apparent point of failure. This command is useful when transferring very large files over networks that are prone to dropping connections. |
| remotehelp [<command-name>] | Request help from the remote FTP server. If a <command-name> is specified it is supplied to the server as well. |
| remotestatus [<file-name>] | With no arguments, show status of remote machine. If <file-name> is specified, show status of <file-name> on remote machine. |
| rename [<from>] [<to>] | Rename the file <from> on the remote machine, to the file <to>. |
| reset | Clear reply queue. This command re-synchronizes command/reply sequencing with the remote FTP server. Resynchronization may be necessary following a violation of the FTP protocol by the remote server. |
| restart <marker> | Restart the immediately following get or put at the indicated marker. On UNIX systems, marker is usually a byte offset into the file. |
| rmdir <directory-name> | Delete a directory on the remote machine. |
| runique | Toggle storing of files on the local system with unique filenames. If a file already exists with a name equal to the target local filename for a get or mget command, a ".1" is appended to the name. If the resulting name matches another existing file, a ".2" is appended to the original name. If this process continues up to ".99", an error message is printed, and the transfer does not take place. The generated unique filename will be reported. Note that runique will not affect local files generated from a shell command (see below). The default value is off. |
| send <local-file> [<remote-file>] | A synonym for put. |
| sendport | Toggle the use of PORT commands. By default, FTP will attempt to use a PORT command when establishing a connection for each data transfer. The use of PORT commands can prevent delays when performing multiple file transfers. If the PORT command fails, FTP will use the default data port. When the use of PORT commands is disabled, no attempt will be made to use PORT commands for each data transfer. This is useful for certain FTP implementations which do ignore PORT commands but, incorrectly, indicate they've been accepted. |
| site <arg1> <arg2> ... | The arguments specified are sent, verbatim, to the remote FTP server as a SITE command. |
| size <file-name> | Return size of <file-name> on remote machine. |
| status | Show the current status of FTP. |
| struct [<struct-name>] | Set the file transfer structure to struct-name. By default "stream" structure is used. |
| sunique | Toggle storing of files on remote machine under unique file names. Remote FTP server must support FTP protocol STOU command for successful completion. The remote server will report unique name. Default value is off. |
| system | Show the type of operating system running on the remote machine. |
| tenex | Set the file transfer type to that needed to talk to TENEX machines. |
| trace | Toggle packet tracing. |
| type [<type-name>] | Set the file transfer type to <type-name>. If no type is specified, the current type is printed. The default type is network ASCII. |
| umask [<newmask>] | Set the default umask on the remote server to <newmask>. If <newmask> is omitted, the current umask is printed. |
| user <user-name> [<password>] [<account>] | Identify yourself to the remote FTP server. If the password is not specified and the server requires it, FTP will prompt the user for it (after disabling local echo). If an account field is not specified, and the FTP server requires it, the user will be prompted for it. If an account field is specified, an account command will be relayed to the remote server after the login sequence is completed if the remote server did not require it for logging in. Unless FTP is invoked with "auto-login" disabled, this process is done automatically on initial connection to the FTP server. |
| verbose | Toggle verbose mode. In verbose mode, all responses from the FTP server are displayed to the user. In addition, if verbose is on, when a file transfer completes, statistics regarding the efficiency of the transfer are reported. By default, verbose is on. |
| ? [<command>] | A synonym for help. |
- Aborting a file transfer
To abort a file transfer, use the terminal interrupt key (usually Ctrl-C). Sending transfers will be immediately halted. Receiving transfers will be halted by sending a FTP protocol ABOR command to the remote server, and discarding any further data received. The speed at which this is accomplished depends upon the remote server's support for ABOR processing. If the remote server does not support the ABOR command, an "ftp>" prompt will not appear until the remote server has completed sending the requested file.
The terminal interrupt key sequence will be ignored when FTP has completed any local processing and is awaiting a reply from the remote server. A long delay in this mode may result from the ABOR processing described above, or from unexpected behavior by the remote server, including violations of the FTP protocol. If the delay results from unexpected remote server behavior, the local FTP program must be killed by hand.
- File naming conventions
Files specified as arguments to FTP commands are processed according to the following rules.
- If the file name "-" is specified, the stdin (for reading) or stdout (for writing) is used.
- If the first character of the file name is "|", the remainder of the argument is interpreted as a shell command. FTP then forks a shell, using popen(3) with the argument supplied, and reads (writes) from the stdout (stdin). If the shell command includes spaces, the argument must be quoted; e.g. "ls -lt". A particularly useful example of this mechanism is: "dir more".
- Failing the above checks, if "globbing" is enabled, local file names are expanded according to the rules used in the csh(1); c.f. the glob command. If the FTP command expects a single local file (.e.g. put), only the first filename generated by the "globbing" operation is used.
- For mget commands and get commands with unspecified local file names, the local filename is the remote filename, which may be altered by a case, ntrans, or nmap setting. The resulting filename may then be altered if runique is on.
- For mput commands and put commands with unspecified remote file names, the remote filename is the local filename, which may be altered by a ntrans or nmap setting. The resulting filename may then be altered by the remote server if sunique is on.
- File transfer parameters
The FTP specification specifies many parameters which may affect a file transfer. The type may be one of "ascii", "image" (binary), "ebcdic", and "local byte size" (for PDP-10's and PDP-20's mostly). FTP supports the ascii and image types of file transfer, plus local byte size 8 for tenex mode transfers.
FTP supports only the default values for the remaining file transfer parameters: mode, form, and struct.
- The .netrc file
The .netrc file contains login and initialization information used by the auto-login process. It resides in the user's home directory. The following tokens are recognized; they may be separated by spaces, tabs, or new-lines:
| machine name | Identify a remote machine name. The auto-login process searches the .netrc file for a machine token that matches the remote machine specified on the FTP command line or as an open command argument. Once a match is made, the subsequent .netrc tokens are processed, stopping when the end of file is reached or another machine or a default token is encountered. |
| default | This is the same as machine name except that default matches any name. There can be only one default token, and it must beafter all machine tokens. This is normally used as:
thereby giving the user automatic anonymous FTP login to machines not specified in .netrc. This can be overridden by using the -n flag to disable auto-login. |
| login name | Identify a user on the remote machine. If this token is present, the auto-login process will initiate a login using the specified name. |
| password string | Supply a password. If this token is present, the auto-login process will supply the specified string if the remote server requires a password as part of the login process. Note that if this token is present in the .netrc file for any user other than anonymous, FTP will abort the auto-login process if the .netrc is readable by anyone besides the user. |
| account string | Supply an additional account password. If this token is present, the auto-login process will supply the specified string if the remote server requires an additional account password, or the auto-login process will initiate an ACCT command if it does not. |
| macdef name | Define a macro. This token functions like the FTP macdef command functions. A macro is defined with the specified name; its contents begin with the next .netrc line and continue until a null line (consecutive new-line characters) is encountered. If a macro named init is defined, it is automatically executed as the last step in the auto-login process. |
- Environment
FTP utilizes the following environment variables.
| HOME | For default location of a .netrc file, if one exists. |
| SHELL | For default shell. |
- Bugs
Correct execution of many commands depends upon proper behavior by the remote server.
An error in the treatment of carriage returns in the 4.2BSD ascii-mode transfer code has been corrected. This correction may result in incorrect transfers of binary files to and from 4.2BSD servers using the ascii type. Avoid this problem by using the binary image type.
- Example 1
Missing examples.
GET
Gets the value of a local variable.
- Format
- GET <name>
- Template
- NAME/A
- Location
- Internal
GET is used to retrieve and display the value of a local environment variable. The value is displayed in the current window.
Local environment variables are only recognized by the Shell in which they are created or by any Shells created from a NEWSHELL command executed in the original Shell. If you open an additional Shell by opening the Shell icon or by using the Execute Command menu item, previously created local environment variables are not available.
- Example
1> GET editor Extras:Tools/MEmacs
- See also
GETENV
Gets the value of a global variable.
- Format
- GETENV <name>
- Template
- NAME/A
- Location
- Internal
GETENV is used to retrieve and display the value of a global environment variable. The value is displayed in the current window. Global variables are stored in ENV: and are recognized by all Shells.
- Example
1> GETENV editor Extras:Tools/MEmacs
- See also
GETNETSTATUS
Queries whether the network is operational.
- Format
- GETNETSTATUS [CHECK=condition[,condition...]] [QUIET]
- Template
- CHECK/K,QUIET
- Location
- C:
The command is used to check/display which interfaces are currently running and which settings are being configured. It can be used in script files or for quick diagnostic purposes. The options are:
| CHECK | A list of conditions to check, which must be separated by commas. The following conditions can be checked:
If any of the conditions to test for is not satisfied, a message to this effect will be printed and the command will exit with status 5, which can be tested in script files using the 'IF WARN' command. | ||||||||||||
| QUIET | Whatever happens, except for errors no output will be produced. |
If no conditions are to be checked for, then this command will print version information and the list of conditions that can be tested for, indicating which ones are satisfied and which are not.
- Example 1
Find out which conditions can be tested.
1> GETNETSTATUS bsdsocket.library 4.307 (9.2.2012) [Roadshow 4.307 (9.2.2012)] Networking interfaces are available and configured. No point-to-point networking interfaces are available and configured. Broadcast networking interfaces are available and configured. Name resolution servers are configured. Routing information is configured. The default route is configured.
- Example 2
A script to test if the interfaces are operational.
GETNETSTATUS CHECK="INTERFACES" QUIET
IF NOT WARN
ECHO "All interfaces are operational."
ELSE
GETNETSTATUS
ENDIF
GROUP
Changes the access rights of a file or directory.
- Format
- GROUP [FILE] {<file | pattern>} [GROUP] <name or number> [ALL] [QUIET]
- Template
- FILE/A/M,GROUP/A,ALL/S,QUIET/S
- Location
- C:
Each file or directory bears information which describes who may access it. This information can be displayed by the LIST command and is important if that file or directory is made accessible through a networked file system.
The GROUP command will change the access rights of one or more files or directories. The 'group' must be given either as a name or a number. The file system will have to understand the name given, or you will see an error message to this effect. If you know in advance which numeric group ID should be used in place of a name, you can provide this instead. Note that group names cannot be longer than 31 characters and that numeric group IDs must be in the range 0..65535. An empty name given for the group will remove the access rights information.
The options are:
| ALL | If the ALL option is given, GROUP will change the access rights of all the files in the specified directory. |
| QUIET | If the QUIET option is given, screen output is suppressed. The local shell variable _Verbosity with a negative value has the same effect. |
- Example 1
1> GROUP textfile admin
Grants access rights to "textfile" to the group "admin"
- Example 2
1> GROUP textfile ""
Removes any access rights from "textfile".
HELP
Text based help command.
- Format
- HELP [<command name> [SHORT | LFORMAT]] | [SHOWLIST]
- Template
- COMMANDNAME,SHORT/S,LFORMAT/S,SHOWLIST/S
- Location
- Rexx:
HELP will display the help text of a command given in argument. If no arguments is given, a brief description of this help system is displayed.
By default all the available text for the supplied command name will be printed in the Shell.
If the SHORT argument is supplied, only a short description will be printed. This text is extracted from the section "NAME" of the help text.
Some commands use the LFORMAT argument to customize the command output. This argument is always used with several output qualifiers. Supplying the LFORMAT argument to the HELP command, only the details on the usage of the LFORMAT argument will be printed. This text is extracted from the section "LFORMAT" of the help text.
If the SHOWLIST argument is supplied, a list of all available help texts with the short description will be displayed.
The HELP command will look for text help files in HELP:<your language>/Shell and if it could not be found, it will look into HELP:english/Shell.
HELP will display the help texts with the program you specify in the PAGER environment variable. By default, help texts will be displayed with the MORE program. As an example, if you want to use the TYPE command, store it into the PAGER variable with "SETENV PAGER TYPE".
HI
Halts all ARexx programs.
- Format
- HI
- Template
- (none)
- Location
- C:
Sets the global halt flag, which causes all active ARexx programs to receive an external halt request. Each program will exit immediately unless its HALT interrupt has been enabled. The halt flag does not remain set, but is cleared automatically after all current programs have received the request.
- Example
1> HI Command returned 10/2: Execution halted rx failed returncode 10
HISTORY
Displays, recalls, or stores the command line history.
- Format
- HISTORY [[LINES] <number>] [START <number>] [LOAD <file name>]
- [SAVE <file name>] [SIZE <number>] [CLEAR] [SHOW] [NONUM]
- Template
- LINES/N,START/K/N,LOAD/K,SAVE/K,SIZE/K/N,CLEAR/S,SHOW/S,NONUM/S
- Location
- C:
HISTORY can be used to show the past command line history, to save it to a file or load it from a file. If no other options are specified, it will show the command line history, each line prefixed by a number.
To restrict the number of history lines shown, use the LINES parameter; the default is to list all history lines, starting with the first one. To start the listing with a different line, use the START parameter. Each line will be prefixed by a number; to ignore the number, use the NONUM parameter.
The command history can be stored in or loaded from a file. To do either, specify the name of the file to be used with the LOAD or SAVE commands. These commands can be combined: the history command will always perform the SAVE command first before it performs the LOAD command. Note that the command line history will be added to the current list if loaded with the LOAD parameter unless you use the CLEAR parameter, too. Used all by itself, the CLEAR parameter will drop the current command line history.
The SIZE parameter controls the size of the command line history buffer which by default has room for about four complete command lines of maximum length. Changing the size tries to retain the contents of the current command line history buffer.
- Example 1
1> HISTORY
Lists the current command line history, starting with the first line, printing all lines in the buffer.
- Example 2
1> HISTORY LINES 5 START 3
Prints five lines of command line history, starting with the third line. If fewer lines are stored in the buffer, fewer will be printed.
- Example 3
1> HISTORY SAVE old-history LOAD new-history CLEAR
Saves the current command line history in the file 'old-history', then clears the history buffer and eventually loads the command line history from the file 'new-history'. Note that if either the save or the load command fails no changes will be made to the contents of the current history buffer.
- Example 4
1> HISTORY SIZE 16
Sets the maximum size of the history buffer to about 8,000 characters.
- Example 5
1> HISTORY START -2 LINES 1 NONUM
Displays the last command line entered (preceding the 'HISTORY START -2 LINES 1 NONUM' command).
ICONX
| Note |
|---|
| ICONX is used only as a default tool in a project icon and cannot be used as a Shell command. |
Allows execution of a script file of AmigaDOS commands from an icon.
- Format
- ICONX
- Template
- (none)
- Location
- C:
To use ICONX, create or copy a project icon for the script. Open the icon's Information window and change the Default Tool of the icon to C:ICONX and select Save to store the changed .info file. The script can then be executed by double-clicking on the icon.
When the icon is opened, ICONX changes the current directory to the directory containing the project icon before executing the script. A console window can be opened on the Workbench screen if the script produces output.
Several Tool Types can be specified in the script icon. The WINDOW Tool Type provides an alternate window specification for the input/output window. By default, the window's specification is:
WINDOW=CON:0/50//80/IconX/AUTO/WAIT/CLOSE
The AUTO option opens a window only if there is output created by the script. If a window opens, the WAIT option forces it to remain open after the script terminates until you specifically close it. The CLOSE option gives the window a close gadget.
The WAIT Tool Type (not to be confused with the WAIT option of the WINDOW Tool Type) specifies the number of seconds the input/output window should remain open after the script terminates. If you use this option the default input/output window cannot be closed before the WAIT period has expired. There is also a DELAY Tool Type that works in very similar way, except that its parameter is in 1/50th of a second, instead of in seconds.
The STACK Tool Type specifies the number of bytes to use for stack during script execution. If this Tool Type is not provided, the default 4096 bytes is used.
Finally, the USERSHELL Tool Type runs the script file using the current Use Shell instead of the normal ROM Shell. You must specify USERSHELL=YES. User Shells are third party shells that you can purchase and install in your system to replace the standard Amiga Shell environment that comes with the operating system.
Extended selection passes files that have icons to the script. Their file names appear to the script as keywords. To use this facility, the .KEY keyword must appear at the start of the script. In this case, the AmigaDOS EXECUTE command is used to execute the script file.
- See also
IDENTD
TCP/IP IDENT protocol server.
- Format
- IDENTD
- Template
- (none)
- Location
- C:
When running IDENTD returns user information to a remote host that a user is requesting a service from.
IDETOOL
Modfies ATA/ATAPI device driver parameters.
- Format
- IDETOOL [ <command> [ <argument>... ] ]...
- Template
- -v,-c,-l,-u,-d,-r,-x,-p,-i,-o,-j,-m,-w,-s,-a,-b,-e,-f,-t,-g,-0,-1,-2,-3,-4,-5,-6,-7,-8,-9
- Location
- C:
IDETOOL allows querying and modifying internal parameters of the following ATA/ATAPI device drivers:
- a1ide.device, which controls the VIA686B PATA IDE controller
- sii0680ide.device, which controls Silicon Image SiI0680(A)-based PCI PATA IDE controller
- sii3112ide.device, which controls Silicon Image SiI3112(A)-based PCI SATA IDE controller
- sii3114ide.device, which controls Silicon Image SiI3114-based PCI SATA IDE controller
- sii3512ide.device, which controls Silicon Image SiI3512-based PCI SATA IDE controller
- lsi53c8xx.device, which controls LSI Logic 53c8xx-based SCSI PCI controllers
IDETOOL can also be used to examine and modify any PCI device configuration and I/O space (only use this feature if you really know what you are doing). A word on PCI device configuration space:
- All PCI devices are uniquely identified by a Vendor and a Product code. Those are 16 bit figures, which can be represented as 4 hex digit values. Example: the VIA IDE controller is identified by vendor code 0x1106 and product code 0x0571.
- All PCI devices expose on the bus, 256 bytes of configuration data called the "configuration space". This configuration space contains a part which is rigidly defined in the PCI specification, and a part which structure is up to the device manufacturer. In the standardized part, we find things like the vendor & product codes, the PCI latency setting for the device, the interrupt pin / line settings for the device etc.
- Additionnally to this configuration space, each PCI device can have up to 5 address ranges, which can either be "IO space" or "memory space", for whatever usage. Example: a graphics card will probably have a memory mapped area which contains a linearly addressed image of its framebuffer memory.
The purpose of the PCI configuration and IO manipulation features in IDETOOL is primarily to be able to finetune the IDE device operation, but it can also be used as a general purpose diagnostic and tuning tool for all other PCI devices (USB, Ethernet, Audio, Graphic cards etc.).
IDETOOL recognizes the following commads:
| -v | tell version |
| -c | tell CPU configuration |
| -l <device name> | tell unit info for all device <device name> units |
| -u <device name> <unit> | tell unit info for unit <unit> |
| -d <device name> <unit> | tell drive info for unit <unit> |
| -r <device name> <unit> | tell raw drive info for unit <unit> |
| -x <device name> <unit> <mode> | put drive <unit> into transfer mode <mode> |
| -p <device name> <unit> <mode> | put drive <unit> into power mode <mode>: 2 = spin up, 3 = spin down, 5 = sleep forever |
| -i <device name> <unit> <mode> | put drive <unit> into interrupt mode <mode>: 0 = don't use irq's, 1 = use irq's |
| -o <device name> <unit> | just open & close <device name>/<unit> |
| -j <device name> <unit> e | l | eject/load disk in drive <unit>. e = eject, l = load |
| -m <device name> <unit> <read speed> <write speed> | set <unit> medium read / write speed: 1 .. n for x1 ... xn, or 0xFFFF for max. |
| -w | tell VIA686b PCI IDE configuration |
| -s | tell SiI0680 PCI IDE configuration |
| -a | tell SiI3112 PCI IDE configuration |
| -b | tell SiI3114 PCI IDE configuration |
| -e | tell SiI3512 PCI IDE configuration |
| -f | tell LSI53cxxx PCI SCSI configuration |
| -t <vendor> <device> | tell PCI device <vendor>/<device> configuration |
| -g <reg> <val> | patch LSI53cxxx configspace byte <reg> with value <val> |
| -0 <reg> <val> | patch VIA function 0 (ISA) configspace byte <reg> with value <val> |
| -1 <reg> <val> | patch VIA function 1 (IDE) configspace byte <reg> with value <val> |
| -2 <reg> <val> | patch SiI0680 configspace byte <reg> with value <val> |
| -3 <reg> <val> | patch SiI3112 configspace byte <reg> with value <val> |
| -4 <reg> <val> | patch SiI3114 configspace byte <reg> with value <val> |
| -5 <reg> <val> | patch SiI3512 configspace byte <reg> with value <val> |
| -6 <vendor> <device> <reg> | tell PCI device <vendor>/<device> I/O byte <reg> value |
| -7 <vendor> <device> <reg> <val> | patch PCI device <vendor>/<device> I/O byte <reg> with value <val> |
| -8 <vendor> <device> <reg> | tell PCI device <vendor>/<device> configspace byte <reg> value |
| -9 <vendor> <device> <reg> <val> | patch PCI device <vendor>/<device> configspace byte <reg> with value <val> |
| Note |
|---|
| Note on inputting numeric values: if the first character is 0 and the second character is not 'x' or 'X', the string is interpreted as an octal integer; otherwise, it is interpreted as a decimal number. If the first character is '0' and the second character is 'x' or 'X', the string is interpreted as a hexadecimal integer. |
Beware: Do not use IDETOOL except if you really know what you are doing.
IF
Evaluates conditional operations in script files.
- Format
- IF [NOT] [WARN | ERROR | FAIL] [<string> EQ| GT | GE <string>] [VAL] [EXISTS <filename>]
- Template
- NOT/S,WARN/S,ERROR/S,FAIL/S,EQ/K,GT/K,GE/K,VAL/S,EXISTS/K
- Location
- Internal
In a script file, IF, when its conditional is true, carries out all the subsequent commands until an ENDIF or ELSE command is found. IF must be used in conjunction with ENDIF, however, ELSE is optional. When the conditional is not true, execution skips directly to the ENDIF or to an ELSE. The conditions and commands in IF and ELSE blocks can span more than one line before their corresponding ENDIFs.
Nested Ifs jump to the matching ENDIF.
The additional keywords are as follows:
| NOT | Reverses the interpretation of the result. |
| WARN | True if previous return code is greater than or equal to 5. |
| ERROR | True if previous return codes is greater than or equal to 10; only available if FAILAT is set to greater than 10. |
| FAIL | True if previous return code is greater than or equal to 20; only available if FAILAT is set to greater than 20. |
| <a> GT | True if the test of a is greater than the text of b (disregarding case). Use NOT GT for less than. |
| <a> GE | True if the text of a is greater than or equal to the text of b (disregarding case). Use NOT GE for less than or equal to. |
| <a> EQ | True if the text of a and b is identical (disregarding case). |
| VAL | Specifies a numeric comparison. |
| EXISTS <file> | True if the file exists. |
If more than one of the three condition-flag keywords (WARN, ERROR, FAIL) are given, the one with the lowest value is used.
You can use local or global variables with IF by prefacing the variable name with a $ character.
- Example 1
IF EXISTS Work/Prog
TYPE Work/Prog HEX
ELSE
ECHO "It's not here"
ENDIF
AmigaDOS displays the file Work/Prog if it exists in the current directory. Otherwise, AmigaDOS displays the message It's not here and continues after the ENDIF.
- Example 2
IF ERROR
SKIP errlab
ENDIF
ECHO "No error"
LAB errlab
If the previous command produces a return code greater than or equal to 10, AmigaDOS skips over the ECHO command to the errlab label.
- See also
INFO
Gives information about the mounted devices.
- Format
- INFO [<device>] [DEVICES] [VOLUMES] [SHOW=<BLOCKS|BYTES|SIZE>]
- [SORT=<NAME|FREE|USED|SIZE|VOLUME>]
- Template
- DEVICE,DEVICES/S,VOLUMES/S,SHOW/K,SORT/K
- Location
- C:
INFO displays a line of information about each disk or partition. This includes the maximum size of the disk, the used and free space, the number of soft disk errors that have occurred, the status of the disk and the DOS type if available.
With the DEVICE argument, INFO provides information on just one device or volume.
The options are:
| DEVICES | Show only device information, omit volume data. |
| VOLUMES | Show only volume information, omit device data. |
| SHOW | Select the format in which the Free/Full column data should be printed. This must be one of BLOCKS, BYTES or SIZE. "BLOCKS", which is the default, will display the number blocks available for use and already allocated. "BYTES" will display the same information in bytes. Note that due to how the file system allocates storage space, this may not be an accurate figure. Typically, a file needs more storage space on disk than just the data stored in it. "SIZE" will print an approximate rough figure in the KByte/MByte/GByte range, similar to the "Size" column. |
| SORT | Choose by which criterion the device list should be sorted. This must be one of NAME (the default), FREE (by free space), USED (by allocated space), SIZE (total size) or VOLUME (volume name). Note that because block sizes may vary, for FREE, USED and SIZE the number of bytes is used account, not the number of blocks. |
- Example 1
1> INFO Unit Size Used Free Full Errors Status Name DOS Type DF0: 837K 1742 16 98% 0 Read Only Workbench2.0 DOS\01 DF1: 837K 211 1547 12% 0 Read/Write Text-6 DOS\03 Volumes available: Workbench2.0 [Mounted] Text-6 [Mounted]
- Example 2
1> INFO SHOW=BYTES Mounted disks: Unit Size Used Free Full Errors Status Name DOS Type DF0: 837K 850096 7808 98% 0 Read Only Workbench2.0 DOS\01 DF1: 837K 102968 754936 12% 0 Read/Write Text-6 DOS\03 Volumes available: Workbench2.0 [Mounted] Text-6 [Mounted]
- Example 3
1> INFO VOLUMES Volumes available: Workbench2.0 [Mounted] Text-6 [Mounted]
INSTALL
Writes or inspects a boot blocks on a formatted floppy disk or PCMCIA card, specifying whether it should be bootable.
- Format
- INSTALL [DRIVE] <DF0: | DF1: | DF2: | DF3: | CC0:> [NOBOOT] [CHECK] [FFS]
- Template
- DRIVE/A,NOBOOT/S,CHECK/S,FFS/S
- Location
- C:
INSTALL clears a floppy disk's or PCMCIA memory card's boot block area and writes a valid boot onto it. INSTALL does not affect any files or directories on the disk or card. The necessary files and directories must still be present on a device to boot from it successfully.
The NOBOOT option removes the boot block from an AmigaDOS disk or card, making it not bootable.
The CHECK option checks for valid boot code. It reports whether a disk or card is bootable and whether standard Amiga boot code is present on the media. This is useful in detecting some viruses.
The FFS switch is ignored. It remains part of the template to ensure compatibility with earlier scripts and programs.
- Example 1
1> INSTALL DF0: CHECK No bootblock installed
indicates that there is a non-bootable floppy in DF0:.
- Example 2
1> INSTALL DF0:
makes the disk in drive DF0: a bootable disk.
- Example 3
1> INSTALL DF0: CHECK Appears to be FFS bootblock
indicates that there is a bootable FFS floppy in DF0:.
IPF
Alters packet filtering lists for IP packet input and output.
- Format
- IPF [-AdDEInoPrsvVyzZ] [-l <block | pass | nomatch>] [-F < i | o | a | s | S >] -f <filename> [-f <filename> [...]]
- Template
- -A,-d,-D,-E,-I,-n,-o,-P,-r,-s,-v,-V,-y,-z,-Z,-l,-F,-f
- Location
- C:
IPF opens the filenames listed (treating "-" as stdin) and parses the file for a set of rules which are to be added or removed from the packet filter rule set.
Each rule processed by IPF is added to the kernel's internal lists if there are no parsing problems. Rules are added to the end of the internal lists, matching the order in which they appear when given to IPF.
The options are:
| -A | Set the list to make changes to the active list (default). |
| -d | Turn debug mode on.Causes a hexdump of filter rules to be generated as it processes each one. |
| -D | Disable the filter (if enabled). Not effective for loadable kernel versions. |
| -E | Enable the filter (if disabled). Not effective for loadable kernel versions. |
| -F | This option specifies which filter list to flush. The parameter should either be "i" (input), "o" (output) or "a" (remove all filter rules). Either a single letter or an entire word starting with the appropriate letter maybe used. This option maybe before, or after, any other with the order on the command line being that used to execute options. |
| -F |
To flush entries from the state table, the -F option is used in conjuction with either "s" (removes state information about any non-fully established connections) or "S" (deletes the entire state table). Only one of the two options may be given. A fully established connection will show up in IPFSTAT -s output as 4/4, with deviations either way indicating it is not fully established any more. |
| -f <filename> | This option specifies which files IPF should use to get input from for modifying the packet filter rule lists. |
| -I | Set the list to make changes to the inactive list. |
| -l <pass | block | nomatch> | Use of the -l flag toggles default logging of packets. Valid arguments to this option are pass, block and nomatch. When an option is set, any packet which exits filtering and matches the set category is logged. This is most useful for causing all packets which don't match any of the loaded rules to be logged. |
| -n | This flag (no-change) prevents IPF from actually making any ioctl calls or doing anything which would alter the currently running kernel. |
| -o | Force rules by default to be added/deleted to/from the output list, rather than the (default) input list. |
| -P | Add rules as temporary entries in the authentication rule table. |
| -r | Remove matching filter rules rather than add them to the internal lists |
| -s | Swap the active filter list in use to be the "other" one. |
| -v | Turn verbose mode on. Displays information relating to rule processing. |
| -V | Show version information. This will display the version information compiled into the IPF binary and retrieve it from the kernel code (if running/present). If it is present in the kernel, information about its current state will be displayed (whether logging is active, default filtering, etc). |
| -y | Manually resync the in-kernel interface list maintained by IP Filter with the current interface status list. |
| -z | For each rule in the input file, reset the statistics for it t zero and display the statistics prior to them being zero'd. |
| -Z | Zero global statistics held in the kernel for filtering only (this doesn't affect fragment or state statistics). |
- See also
IPFSTAT
Reports on packet filter statistics and filter list.
- Format
- IPFSTAT [ -aAfghIinosv ] [ -d <device> ]
- IPFSTAT -t [ -C ] [ -D <addrport> ] [ -P <protocol> ] [ -S <addrport> ] [ -T <refresh time> ] [ -d <device> ]
- Template
- -a,-A,-f,-g,-h,-I,-i,-n,-o,-s,-v,-d
- -t,-C,-D,-P,-S,-T,-d
- Location
- C:
IPFSTAT examines /dev/kmem using the symbols _fr_flags, _frstats, _filterin, and _filterout. To run and work, it needs to be able to read both /dev/kmem and the kernel itself. The kernel name defaults to /vmunix.
The default behaviour of IPFSTAT is to retrieve and display the accumulated statistics which have been accumulated over time as the kernel has put packets through the filter.
The options are:
| -a | Display the accounting filter list and show bytes counted against each rule. |
| -A | Display packet authentication statistics. |
| -C | This option is only valid in combination with -t. Display "closed" states as well in the top. Normally, a TCP connection is not displayed when it reaches the CLOSE_WAIT protocol state. With this option enabled, all state entries are displayed. |
| -d <device> | Use a device other than /dev/ipl for interfacing with the kernel. |
| -D <addrport> | This option is only valid in combination with -t. Limit the state top display to show only state entries whose destination IP address and port match the addport argument. The addrport specification is of the form ipaddress[,port]. The ipaddress and port should be either numerical or the string "any" (specifying any ip address resp. any port). If the -D option is not specified, it defaults to "-D any,any". |
| -f | Show fragment state information (statistics) and held state information (in the kernel) if any is present. |
| -g | Show groups currently configured (both active and inactive). |
| -h | Show per-rule the number of times each one scores a "hit". For use in combination with -i. |
| -i | Display the filter list used for the input side of the kernel IP processing. |
| -I | Swap between retrieving "inactive"/"active" filter list details. For use in combination with -i. |
| -n | Show the "rule number" for each rule as it is printed. |
| -o | Display the filter list used for the output side of the kernel IP processing. |
| -P <protocol> | This option is only valid in combination with -t. Limit the state top display to show only state entries that match a specific protocol. The argument can be a protocol name (as defined in /etc/protocols) or a protocol number. If this option is not specified, state entries for any protocol are specified. |
| -s | Show packet/flow state information (statistics only). |
| -sl | Show held state information (in the kernel) if any is present (no statistics). |
| -S <addrport> | This option is only valid in combination with -t. Limit the state top display to show only state entries whose source IP address and port match the addport argument. The addrport specification is of the form ipaddress[,port]. The ipaddress and port should be either numerical or the string "any" (specifying any ip address resp. any port). If the -S option is not specified, it defaults to "-S any,any". |
| -t | Show the state table in a way similar to they way top(1) shows the process table. States can be sorted using a number of different ways. This options requires ncurses(3) and needs to be compiled in. It may not be available on all operating systems. See below, for more information on the keys that can be used while IPFSTAT is in top mode. |
| -T <refreshtime> | This option is only valid in combination with -t. Specifies how often the state top display should be updated. The refresh time is the number of seconds between an update. Any postive integer can be used. The default (and minimal update time) is 1. |
| -v | Turn verbose mode on. Displays more debugging information. |
- Synopsis
The role of IPFSTAT is to display current kernel statistics gathered as a result of applying the filters in place (if any) to packets going in and out of the kernel. This is the default operation when no command line parameters are present.
When supplied with either -i or -o, it will retrieve and display the appropriate list of filter rules currently installed and in use by the kernel.
- State top
Using the -t option IPFSTAT will enter the state top mode. In this mode the state table is displayed similar to the way top displays the process table. The -C, -D, -P, -S and -T commandline options can be used to restrict the state entries that will be shown and to specify the frequency of display updates.
In state top mode, the following keys can be used to influence the displayed information:
| d | select information to display. |
| l | redraw the screen. |
| q | quit the program. |
| s | switch between different sorting criterion. |
| r | reverse the sorting criterion. |
States can be sorted by protocol number, by number of IP packets, by number of bytes and by time-to-live of the state entry. The default is to sort by the number of bytes. States are sorted in descending order, but you can use the r key to sort them in ascending order.
- State top limitations
It is currently not possible to interactively change the source, destination and protocol filters or the refresh frequency. This must be done from the command line.
The screen must have at least 80 columns. This is however not checked.
Only the first X-5 entries that match the sort and filter criteria are displayed (where X is the number of rows on the display. There is no way to see more entries.
No support for IPv6
- Files
- /dev/kmem
- /dev/ipl
- /dev/ipstate
- /vmunix
- See also
IPMON
Monitors /dev/ipl for logged packets.
- Format
- IPMON [-aDFhnpstvxX] [-N <device>] [-o [NSI]] [-O [NSI]] [-P <pidfile>] [-S <device>] [-f <device>] [<filename>]
- Template
- -N,-F,-h,-s,-t,-v,-x,-X,-f
- Location
- C:
IPMON opens /dev/ipl for reading and awaits data to be saved from the packet filter. The binary data read from the device is reprinted in human readable for, however, IP#'s are not mapped back to hostnames, nor are ports mapped back to service names. The output goes to standard output by default or a filename, if given on the command line. Should the -s option be used, output is instead sent to SYSLOGD. Messages sent via syslog have the day, month and year removed from the message, but the time (including microseconds), as recorded in the log, is still included.
Messages generated by IPMON consist of whitespace separated fields. Fields common to all messages are:
- The date of packet receipt. This is suppressed when the message is sent to syslog.
- The time of packet receipt. This is in the form HH:MM:SS.F, for hours, minutes seconds, and fractions of a second (which can be several digits long).
- The name of the interface the packet was processed on, e.g., we1.
- The group and rule number of the rule, e.g., @0:17. These can be viewed with IPFSTAT -n.
- The action: p for passed or b for blocked.
- The addresses. This is actually three fields: the source address and port (separted by a comma), the -> symbol, and the destination address and port. E.g.: 209.53.17.22,80 -> 198.73.220.17,1722.
- PR followed by the protocol name or number, e.g., PR tcp.
- len followed by the header length and total length of the packet, e.g., len 20 40.
If the packet is a TCP packet, there will be an additional field starting with a hyphen followed by letters corresponding to any flags that were set. See the ipf.conf manual page for a list of letters and their flags. If the packet is an ICMP packet, there will be two fields at the end, the first always being "icmp", and the next being the ICMP message and submessage type, separated by a slash, e.g., icmp 3/3 for a port unreachable message.
In order for IPMON to properly work, the kernel option IPFILTER_LOG must be turned on in your kernel. Please see options for more details.
The options are:
| -a | Open all of the device logfiles for reading log entries from. All entries are displayed to the same output "device" (stderr or syslog). | ||||||||
| -D | Cause IPMON to turn itself into a daemon. Using subshells or backgrounding of IPMON is not required to turn it into an orphan so it can run indefinately. | ||||||||
| -f <device> | specify an alternative device/file from which to read the log information for normal IP Filter log records. | ||||||||
| -F | Flush the current packet log buffer. The number of bytes flushed is displayed, even should the result be zero. | ||||||||
| -n | IP addresses and port numbers will be mapped, where possible, back into hostnames and service names. | ||||||||
| -N <device> | Set the logfile to be opened for reading NAT log records from to <device>. | ||||||||
| -o | Specify which log files to actually read data from. N - NAT logfile, S - State logfile, I - normal IP Filter logfile. The -a option is equivalent to using -o NSI. | ||||||||
| -O | Specify which log files you do not wish to read from. This is most sensibly used with the -a. Letters available as paramters to this are the same as for -o. | ||||||||
| -p | Cause the port number in log messages to always be printed as a number and never attempt to look it up as from /etc/services, etc. | ||||||||
| -P <pidfile> | Write the pid of the IPMON process to a file. By default this is //etc/opt/ipf/IPMON.pid (Solaris), /var/run/IPMON.pid (44BSD or later) or /etc/IPMON.pid for all others. | ||||||||
| -s | Packet information read in will be sent through SYSLOGD rather than saved to a file. The default facility when compiled and installed is local0.
The following levels are used:
| ||||||||
| -S <device> | Set the logfile to be opened for reading state log records from to <device>. | ||||||||
| -t | read the input file/device in a manner akin to TAIL. | ||||||||
| -v | show tcp window, ack and sequence fields. | ||||||||
| -x | show the packet data in hex. | ||||||||
| -X | show the log header record data in hex. |
- Diagnostics
IPMON expects data that it reads to be consistent with how it should be saved and will abort if it fails an assertion which detects an anomaly in the recorded data.
- Files
- /dev/ipl
- /dev/ipnat
- /dev/ipstate
- /etc/services
- See also
IPNAT
Defines NAT (Network Address Translation) rules.
- Format
- IPNAT [ -lnrsvCF ] -f <filename>
- Template
- -l,-n,-r,-s,-v,-C,-F,-f
- Location
- C:
IPNAT opens the filename given (treating "-" as stdin) and parses the file for a set of rules which are to be added or removed from the IP NAT.
Each rule processed by IPNAT is added to the kernels internal lists if there are no parsing problems. Rules are added to the end of the internal lists, matching the order in which they appear when given to IPNAT.
The options are:
| -C | delete all entries in the current NAT rule listing (NAT rules) |
| -F | delete all active entries in the current NAT translation table (currently active NAT mappings) |
| -l | Show the list of current NAT table entry mappings. |
| -n | This flag (no-change) prevents ipf from actually making any ioctl calls or doing anything which would alter the currently running kernel. |
| -s | Retrieve and display NAT statistics |
| -r | Remove matching NAT rules rather than add them to the internal lists |
| -v | Turn verbose mode on. Displays information relating to rule processing and active rules/table entries. |
- Files
- /dev/IPNAT
- See also
JOIN
Concatenates two or more files into a new file.
- Format
- JOIN [FILE] <file | pattern>} AS | TO <filename>
- Template
- FILE/M/A,AS=TO/K/A
- Location
- C:
JOIN copies all the listed files, in the order given, to one new file. This destination file cannot have the same name as any of the source files. You must supply a destination file name. The original files remain unchanged. Any number of files can be JOINed in one operation.
TO can be used as a synonym for AS.
- Example
1> JOIN Part1 Part2 Part3 AS Textfile
For another example using JOIN, see Chapter 8.
KDEBUG
Controls kernel debug options.
- Format
- <command>
- Template
- COMMAND/F
- Location
- C:
KDEBUG is a simple interface to set kernel parameters from the command line. The command is sent verbatim for further processing and the actual parsing is left to the kernel itself.
The following kernel commands are available:
| debuglevel <level> | Sets the verbosity of debug output of the kernel.
| ||||||||
| console <name> | Select the console. This is either "serial" or "memory".
Kernels before version 51.44 default to the serial console, 8N1, the baudrate can be specified in UBoot (AmigaOne) or the BootLoader commandline (classic machines). Since kernel version 51.44 the default console is the memory console, to use the serial port instead you can specify the "serial" or "serial=1" keyword on the kernel commandline in UBoot or BootLoader. To view the memory buffer use the DumpDebugBuffer command. When switching the console, this setting survives a soft reboot. Note: the memory console has no input parameters. | ||||||||
| alignment [ warn | nowarn ] | Controls alignment exception warnings. This is either "warn" or "nowarn". Defaults to not warn about alignment exceptions. | ||||||||
| memorymap | Dumps the current memory map if the debug level is 3 or higher. | ||||||||
| pagestat [numpages] | Dumps memory paging statistics. The number of pages to output may be specified. Defaults to print out 20 pages. | ||||||||
| status | Dumps the status of various kernel options. |
- Example 1
Set the kernel debug level to 5.
1> KDEBUG debuglevel 5
- Example 2
Enable serial debug output.
1> KDEBUG console serial
- Example 3
Dump the memory map.
1> KDEBUG debuglevel 3 1> KDEBUG memorymap
- See also
LAB
Specified a label in a script file.
- Format
- LAB [<string>]
- Template
- (none)
- Location
- Internal
LAB is used in script to define a label that is searched for by the SKIP command. The label <string> can be of any length, but must be alphanumeric. No symbols are allowed. If the <string> contains spaces, it must be enclosed in quotation marks.
- See also
LIST
Lists specified information about directories and files.
- Format
- LIST [{<dir|pattern>}] [P|PAT <pattern>] [KEYS] [DATES] [NODATES]
- [TO <name>] [SUB <string>] [SINCE <date>] [UPTO <date>] [QUICK]
- [BLOCK] [NOHEAD] [FILES] [DIRS] [LFORMAT <string>]
- [SORT [NAME] [SIZE] [DATE] [REVERSENAME] [REVERSESIZE]
- [REVERSEDATE]] [USERS] [GROUPS] [MULTI] [ALL]
- Template
- DIR/M,P=PAT/K,KEYS/S,DATES/S,NODATES/S,TO/K,SUB/K,SINCE/K,UPTO/K,QUICK/S,BLOCK/S,NOHEAD/S,FILES/S,DIRS/S,LFORMAT/K,SORT/K,USERS/S,GROUPS/S,MULTI/S,ALL/S
- Location
- C:
LIST displays information about the contents of the current directory. If you specify a <dir>, <pattern>, or <filename> argument, LIST will display information about the specified directory, all directories or files that match the pattern, or the specified file, respectively.
Unless other options are specified, LIST displays the following:
| name | The name of the file or directory. |
| size | The size of the file in bytes. If there is nothing in this file, the field will read empty. For directories, this entry reads Dir. |
| protection | The protection bits that are set for this file are shown as letters. The clear (unset) bits are shown as hyphens. Most files will show the default protection bits, ----rwed for readable/writable/executable/deleteable. See the PROTECT command for more on protection bits. |
| date and time | The date and time the file was created or last altered. |
| comment | The comment, if any, placed on the file using the FILENOTE command. It is preceded by a colon (:). |
LIST uses the following options to change the way the output is displayed:
| PAT <pattern> | Lists only files which match the pattern <pattern>. |
| KEYS | Displays the block number of each file header or directory. |
| DATES | Displays dates in the form DD-MMM-YY (the default unless you use QUICK). |
| NODATES | Will not display date and time information. |
| TO <name> | Specifies an output file or device for LIST; by default, LIST outputs to the current window. |
| SUB <string> | Lists only files containing the substring <string>. |
| SINCE <date> | Lists only files created on or after a certain date. |
| UPTO <date> | Lists only files created on or before a certain date. |
| QUICK | Lists only the names of files and directories. |
| BLOCK | Displays file sizes in blocks, rather than bytes. |
| NOHEAD | Suppresses the printing of the header information. |
| FILES | Lists files only (no directories). |
| DIRS | Lists directories only (no files). |
| LFORMAT | Defines a string to specially format LIST output. |
| SORT <order> | Sorts the directory entries before displaying it, based upon certain criteria. The SORT option requires a list of parameters which define in which order and by which criteria the output should be sorted. The SORT option parameter must match the following template:
N=NAME,D=DATE,S=SIZE,T=TYPE,RN=REVERSENAME,RD=REVERSEDATE, RS=REVERSESIZE,RT=REVERSETYPE The order in which you specify the single options determines the order in which the criteria are matched. Thus, if you want the list to be sorted descending size and by name you would specify SORT=REVERSESIZE,NAME. |
| USERS | Attempt to resolve the name of the 'owner' of a file. If no name resolution is possible, then the numeric owner ID number will be displayed instead. |
| GROUPS | Attempt to resolve the name of the group the 'owner' of a file belongs to. If no name resolution is possible, then the numeric group ID number will be displayed instead. |
| MULTI | Display all linked directories in a multi-assignment. (V53) |
| ALL | Lists all files in directories and subdirectories. |
The LFORMAT option modifies the output of LIST and can be used as a quick method of generating script files. When LFORMAT is specified, the QUICK and NOHEAD options are automatically selected. When using LFORMAT you must specify an output format specification string; this string is incorporated into the script file. If you want the output to be saved, you must redirect it to a file by using the > operator or specifying a TO file.
The format for the output format specification string is LFORMAT=<string>. To include the output of LIST in this string, use the substitution operator %S. The path and filename can be made part of the string this way. Whether the path or the filename is substituted for an occurrence of %S depends on how many occurrences are in the LFORMAT line, and their order, as follows:
| Substituted with each occurrence | ||||
| Occurrences of %S | 1st | 2nd | 3rd | 4th |
| 1 | filename | |||
| 2 | path | filename | ||
| 3 | path | filename | filename | |
| 4 | path | filename | path | filename |
Some new options allow you to specify fields to be printed in the LFORMAT output. These options are:
| %A | Prints file attributes (protection bits). |
| %B | Prints size of file in blocks. |
| %C | Prints any comments attached to the file. |
| %D | Prints the date associated with the file. |
| %E | Prints the file extension. |
| %F | Prints the full file parent path. |
| %G | Prints the name of the group which 'owns' the file. |
| %K | Prints the file key block number. |
| %L | Prints the length of the file in bytes. |
| %M | Prints the file name only, omitting any extension. |
| %N | Prints the name of the file. |
| %P | Prints the file parent path. |
| %R | Prints the name of the object the file/directory is linked to. |
| %T | Prints the time associated with the file. |
| %U | Prints the name user who 'owns' the file. |
| %V | Prints group/other file attributes (protection bits). |
You can put a length specifier and/or a justification specifier between the percent size (%) and the field specifier.
- Example 1
> LIST Dirs Monitors Dir ---- rwed 27-June-90 11:43:59 T Dir ---- rwed Wednesday 11:37:43 Trashcan Dir ---- rwed 21-Jun-90 17:54:20
Only the directories in the current directory, in this case SYS:, are listed. (A shortened version of the typical output is shown above.)
- Example 2
1> LIST LI#? TO RAM:Libs.file
LIST will search for any directories or files that start with LI. The output of LIST will be sent to the Libs.file in RAM:.
- Example 3
1> LIST DF0:Documents UPTO 09-Oct-90
Only the files or directories on the Documents directory of DF0: that have not been changed since October 9, 1990, will be listed.
- Example 4
1> LIST >RAM:Scriptnotes #? LFORMAT="filenote %S%S Testnote"
A new script file, Scriptnotes, is created in RAM:. The contents will include a list of all the files in the current directory. When Scriptnotes is executed, it will add the filenote Testnote to each file. For instance, if the current directory is S:, the contents of Scriptnotes as produced by this command might look like this:
- filenote s:HDBackup.config Testnote
- filenote s:DPat Testnote
- filenote s:Ed-startup Testnote
- filenote s:PCD Testnote
- filenote s:Shell-startup Testnote
- filenote s:SPat Testnote
- filenote s:Startup-sequence Testnote
- See also
LOADRESOURCE
Preloads resources into memory to avoid excessive disk swaps.
NOTE: This command is obsolete.
- Format
- LOADRESOURCE {<name>} [LOCK | UNLOCK]
- Template
- NAME/M,LOCK/S,UNLOCK/S
- Location
- C:
LOADRESOURCE reduces the need for excessive disk swaps on floppy-only systems by preloading the following of resources into memory:
| Libraries | Specify the path name to the library. |
| Devices | Specify the path name to the device; you cannot LOCK devices into memory. |
| Fonts | Specify the path name to the exact font file to be loaded. |
| Catalogs | Specify a path name as LOCALE:Catalogs/<language>/Sys/<catalog>. |
The {<name>} option specifies the paths of the resources to load. The LOCK option tells the command to lock resources, such as libraries, fonts, and catalogs, into memory. This prevents the system from flushing the resource from RAM if memory is low. Although you can preload devices into memory using LOADRESOURCE, you cannot force them to stay in memory using the LOCK option. The UNLOCK option tells the command to unlock the resource from memory, allowing it to be flushed from RAM.
Entering LOADRESOURCE with no options lists all the LOCKed resources in RAM.
- Example 1
1> LOADRESOURCE LIBS:asl.library
loads asl.library into memory. The system can flush this library from RAM the next time it runs low on memory, unless the LOCK option is included in the command line.
- Example 2
1> LOADRESOURCE FONTS:topaz/11
loads the Topaz 11 font into memory.
- Example 3
1> LOADRESOURCE LOCALE:Catalogs/English/Sys/monitors.catalog
is a valid path name.
LOADWB
Starts Workbench.
- Format
- LOADWB [-DEBUG] [DELAY] [CLEANUP] [NEWPATH] [SKIP=SKIPWBSTARTUP] [SIMPLEGELS]
- Template
- -DEBUG/S,DELAY/S,CLEANUP/S,NEWPATH/S,SKIP=SKIPWBSTARTUP/S,SIMPLEGELS/S
- Location
- C:
LOADWB starts the Workbench. Normally, this is done when booting, by placing the LOADWB command in the Startup-Sequence file. If you shut down the Workbench, LOADWB can be used from a Shell to restart it.
Workbench snapshots the current paths in effect when the LOADWB command is executed. It uses these paths for each Shell started from Workbench.
LOADWB's command line options are:
| -DEBUG | Adds two additional menus which can assist software debugging. You should not use this feature unless you know how to use these menus. |
| DELAY | The LoadWB command will wait until the Workbench is loaded and initialized; otherwise, LoadWB will launch the Workbench and return immediately. |
| CLEANUP | Clean up the contents of the main Workbench window once Workbench has been launched. |
| NEWPATH | Update the Workbench command search path to use the settings of the shell the LoadWB program runs in. Workbench uses the search path (maintained through the shell PATH command) to find programs whose names do not include a directory name. |
| SKIPWBSTARTUP | Do not look into the "SYS:WBStartup" drawer and launch the programs stored in it. |
| SIMPLEGELS | When moving icons on the screen, try to use only the technique that Workbench has been using through versions 1.2-3.1. This is a compatibility switch which can be used to prevent Workbench from crashing if the graphics support software does not support the new icon rendering methods introduced in Workbench 3.5. |
- Example 1
If you have quit the Workbench and are working through a Shell, typing:
1> LOADWB
will bring the Workbench back. Typing LOADWB when the Workbench is already loaded has no effect.
- Example 2
1> PATH DF2:bin ADD 1> LOADWB NEWPATH
loads the Workbench. Any Shells started from the icon have the same path as the Shell used to run the LOADWB NEWPATH command.
LOCK
Sets the write-protect status of a device.
- Format
- LOCK <drive> [ON | OFF] [<passkey>]
- Template
- DRIVE/A,ON/S,OFF/S,PASSKEY
- Location
- C:
LOCK sets or unsets the write-protect status of a device or partition. The LOCK remains on until the system is rebooted or until the LOCK is turned off with the LOCK OFF command.
An optional passkey can be specified. If the passkey is used to lock a hard disk partition, the same passkey must be specified to unlock the partition. The passkey can be any number of characters long.
- Example
1> LOCK Work: ON SecretCode
The Work partition is locked. You can read the contents of Work with commands such as DIR, LIST, or MORE but you cannot alter the contents of the partition. If you try to edit the contents of a file on Work, a requester indicates that Work is write-protected. For example, if you try to create a new directory by entering the following:
1> MAKEDIR WORK:Test
the following message appears:
Can't create directory Work:Test Disk is write-protected
To unlock the partition, enter:
1> LOCK Work: OFF SecretCode
Locking a device is only good for the duration of the current session. Resetting or turning off the Amiga cancels the lock.
MAGTAPE
Retensions, rewinds, or skips forward SCSI (Small Computer System Interface) tapes.
- Format
- MAGTAPE [DEVICE <device name>] [UNIT <n>] [RET | RETENSION] [REW | REWIND] [SKIP <n>]
- Template
- DEVICE/K,UNIT/N/K,RET=RETENSION/S,REW=REWIND/S,SKIP/N/K
- Location
- C:
By default, MAGTAPE uses SCSI device unit 4. To change the default, you must use both the DEVICE and UNIT keywords.
The RET | RETENSION option runs the tape to the end and rewinds it. The REW | REWIND option rewinds the tape. The SKIP <n> option skips <n> files on the tape.
MAGTAPE tests to see if the unit is ready before sending the command. If your tape is not on-line, repeat the command.
- Example
1> MAGTAPE DEVICE second_scsi.device UNIT 0 REW
MAKEDIR
Creates a new directory.
- Format
- MAKEDIR {<name>} [ALL] [FORCE]
- Template
- NAME=DIRS/M/A,ALL/S,FORCE/S
- Location
- C:
MAKEDIR creates one (or several) empty directory(s) with the name(s) you specify. By default, the command works within only one directory level at a time, so any directories on the given path(s) must already exist. When using the ALL option, directories missing on the path(s) are automatically created, if necessary. The command fails if a directory or a file of the same name already exists in the directory above it in the hierarchy. To avoid this, use the FORCE option which makes the command ignore directories which already exist.
| Note |
|---|
| MAKEDIR does not create a drawer icon for the new directory(s). |
- Example 1
1> MAKEDIR Tests
creates a directory called Tests in the current directory.
- Example 2
1> MAKEDIR DF1:Abc/Xyz ALL
creates a directory Abc in the root directory of the disk in DF1: if it doesnt exist yet, then creates directory Xyz in DF1:Abc/.
- Example 3
1> CD DF0: 1> MAKEDIR Documents Payables Orders
creates three directories, Documents, Payables, and Orders, on the disk in DF0:.
MAKELINK
Creates a link between files or directories.
- Format
- MAKELINK [FROM] <link> [TO] <file or directory> [SOFT] [HARD] [FORCE]
- Template
- LINK=FROM/A,FILE=DIR=DIRECTORY=TO/A,SOFT/S,HARD/S,FORCE/S
- Location
- C:
MAKELINK creates a special file on a disk that is a pointer to another file or directory, this is known as a link. When an application or command tries to use the FROM file, the TO file or directory is actually used.
There exist two types of links, hard links and soft links.
A hard link is some sort of "physical" link handled by the file system itself, it points to the physical location (e.g. a disk block) of the destination. This implies that both the link and the destination must be on the same volume, that renaming the destination (including renaming into another directory) cannot "break" the link (it will continue to point to the same object) and that even deleting the destination wont cause problems (the link will be replaced with the file or directory before the file or directory is deleted). Not all file systems support hard links.
A soft link is some sort of "logical" link handled by the file system, dos.library and the applications, it points to a name which describes the path of the destination. All types of paths can be used (absolute and relative, with or without file name). This implies that both the link and the destination can be located on different volumes and that renaming or deleting the destination will "break" the link (it will point to a no longer existing object). Old applications are sometimes not aware of soft links and will consider them to be directories or ignore them altogether. Not all file systems support soft links. Old file systems may have problems with relative path names in soft links ("///dir2/file3"). Some applications may have problems with "broken" soft links for which the respective destinations do not exist any more.
By default, or when the SOFT keyword is given, MAKELINK tries to create a soft link. When the HARD keyword is given, MAKELINK tries to create a hard link. (Note that the default changed to this from version 53.3+)
Also by default when doing soft links, if the destination path is relative (i.e. a path not prefixed by a volume name), MAKELINK will try to resolve it relative to the directory which will contain the link, it will not resolve it relative to the current directory like other commands. See examples below.
When creating a hard link, and the TO argument is a directory name, MAKELINK does not normally allow the creation of a hard link to a directory. When the FORCE keyword is also given, it allows it.
When creating a soft link, the link destination should exist, and MAKELINK will consider it an error if this is not the case. However, it is sometimes necessary to create a soft link before the link destination itself has been made available. In such a case, the FORCE keyword will cause MAKELINK to create the soft link regardless of whether the destination already exists or not.
- Example 1
SYS:> MakeLink RAM:Link S/User-Startup SOFT
will create a soft link to RAM:S/User-Startup (this file must exist) and not to SYS:S/User-Startup as one could expect.
- Example 2
SYS:> MakeLink RAM:Link SYS:S/User-Startup SOFT
will create a soft link to SYS:S/User-Startup (absolute path)
MD5SUM
Calculates and compares checksums of files.
- Format
- MD5SUM [{dir|file|pattern|device}] [ALL] [DEVICES] [TO <name>] [SORT] [BUF=BUFFERSIZE <size>] [CHECK|FROM <name>] [STATUS] [QUIET] [WARN] [ALGORITHM {?|<name>}]
- Template
- NAMES/M,ALL/S,TO/K,DEVICES/S,SORT/S,BUF=BUFFERSIZE/K/N,CHECK=FROM/K,STATUS/S,WARN/S,QUIET/S,ALGORITHM/K
- Location
- C:
MD5SUM will read the contents of files or devices and calculate a checksum for each individual item. If you specify a <dir>, <pattern>, <filename>, or <device> argument, MD5SUM will calculate checksums for the specified directory, all directories, or files that match the pattern, or the specified file or device, respectively. MD5SUM can also determine whether a file or a checksum are consistent.
MD5SUM has options which will change the way the output is displayed and how input is processed. These options are explained below.
ALL calculates checksums for all files in directories and subdirectories.
DEVICES indicates that rather than checking the contents of a device file by file, the checksums should be calculated over the raw storage blocks instead. Note that only file system devices can be used which store data in disk blocks. This includes "df0:", "df1:", etc. but not "ram:" or "prt:".
TO <name> specifies an output file or device for MD5SUM; by default, MD5SUM ouputs to the current window.
SORT sorts the list before printing.
BUFFERSIZE <size> sets the size of the read buffer being used. Default is 262144 bytes (256 kB). Larger values can increase performance.
CHECK <name> causes MD5SUM to read the contents of a list file <name> previously generated by MD5SUM and try to open each file listed in it, calculate its checksum and compare it with the value given in the list. If no matching file could be opened or the checksums do not match, an error message will be printed. Use the STATUS option to omit all output.
If the STATUS option is supplied, no output will be generated if a mismatch is found while a list is being checked. Instead, MD5SUM will immediately abort with WARN condition set; this can be tested in script files.
WARN causes MD5SUM to print a warning message for each line in the list to be checked which does not match the format MD5SUM expects.
QUIET prevents MD5SUM from printing progress reports while individual files or devices are being read. The local shell variable _Verbosity with a negative value has the same effect. Progress reports are printed in about each second. No progress reports are printed if the SORT option is effect.
ALGORITHM sets the checksumming algorithm to be used. The default algorithm is "MD5", but there may be more modern algorithms supported, too. To find out which algorithms are available, enter "MD5SUM ALGORITHM ?", which will list all the supported algorithms by name. At this time of writing the following algorithms are implemented:
| MD5 | Message Digest #5, as defined in RFC 1321.
Note: At this time of writing (2005-11-20) the MD5 algorithm can no longer be considered secure. |
| SHA-1 | Secure Hash Algorithm #1, as defined in U.S. Federal Information Processing Standard (FIPS) 180-1. This Algorithm produces 160 bits of checksum data.
Note: At this time of writing (2005-11-20) the SHA-1 algorithm can no longer be considered secure. |
| SHA-256 | Secure Hash Algorithm, as defined in U.S. Federal Information Processing Standard (FIPS) 180-2. This Algorithm produces 256 bits of checksum data. |
| SHA-384 | Secure Hash Algorithm, as defined in U.S. Federal Information Processing Standard (FIPS) 180-2. This Algorithm produces 384 bits of checksum data. |
| SHA-512 | Secure Hash Algorithm, as defined in U.S. Federal Information Processing Standard (FIPS) 180-2. This Algorithm produces 512 bits of checksum data. |
| Whirlpool | As defined in ISO/IEC 10118-3. This algorithm produces 512 bits of checksum data.
You can choose an algorithm by the name given. Note that the output produced by this MD5SUM program may not be compatible with other "md5sum" shell commands from the Unix world if you choose any checksumming algorithm other than "MD5" here. Good reasons why you might want to use a different checksumming algorithm are in the security of the original "MD5" algorithm. At this time of writing (2005-11-20) it is believed that both the "MD5" and "SHA-1" algorithms can no longer be considered secure and it is recommended that you use a more secure algorithm such as "SHA-256" or "Whirlpool" instead. Support for the "MD5" algorithm is preserved in this command only because "MD5" file checksums are still very common on the Internet. |
| Note |
|---|
| The format of the data produced and used by the MD5SUM command is compatible with the Unix "md5sum" program. |
- Example 1
Calculate checksums for all files in the C: directory and sort the list by file name before printing it:
1> MD5SUM C: SORT 1bd137145fbb3c409771b6bd889adb07 c:AddBuffers 7ab3d10a31518a011a63e5a099beb876 c:AddDataTypes 0ca24f1b23fb52642b895010edf79b89 c:Assign 98abb6f23ca1097898cdf98a84c6d69f c:Avail 891ec3cb98bd0744cbb5f7407e678c71 c:BindDrivers
- Example 2
Calculate the checksums for all files on the Work: partition, sort the list and store it in a file:
1> MD5SUM Work: SORT TO Work.Checksums
- Example 3
Calculate and compare the checksums for all files listed in the file 'Work.Checksums' and print the differences:
1> MD5SUM CHECK Work.Checksums
- Example 4
Calculate the checksums for the disks in the drives DF0 and DF1:
1> MD5SUM DEVICES df0: df1: b0af4fc275bf1cb26016bd6abccc2548 df0: fc2b0af47b01ab5bf1cc6b48d6cc2526 df1:
- Example 5
List all the supported checksumming algorithms:
1> MD5SUM Algorithm ? MD5SUM: Supported algorithms are MD5, SHA-1, SHA-256, SHA-384, SHA-512, Whirlpool.
MEMSTAT
?
- Format
- [VERBOSE] [KB] [DETAILED]
- Template
- VERBOSE/S,KB/S,DETAILED/S
- Location
- C:
Missing description.
MKNTFS
Creates an NTFS file system.
- Format
- MKNTFS [options] device [number-of-sectors]
- MKNTFS [ -C ] [ -c cluster-size ] [ -F ] [ -f ] [ -H heads ] [ -h ] [ -I ]
- [ -L volume-label ] [ -l ] [ -n ] [ -p part-start-sect ] [ -Q ] [ -q ]
- [ -S sectors-per-track ] [ -s sector-size ] [ -T ] [ -U ] [ -V ] [ -v ]
- [ -z mft-zone-multiplier ] [ --debug ] device [ number-of-sectors ]
- Template
- Missing
- Location
- C:
MKNTFS is used to create an NTFS file system on a device (usually a disk partition) or file. device is the special file corresponding to the device (e.g /dev/hdXX). number-of-sectors is the number of sectors on the device. If omitted, MKNTFS automagically figures the file system size.
Below is a summary of all the options that MKNTFS accepts. Nearly all options have two equivalent names. The short name is preceded by - and the long name is preceded by --. Any single letter options, that don‚t take an argument, can be combined into a single command, e.g. -fv is equivalent to -f -v. Long named options can be abbreviated to any unique prefix of their name.
- Basic options
| -f, --fast, -Q, or --quick | Perform quick (fast) format. This will skip both zeroing of the volume and bad sector checking. |
| -L, --label STRING | Set the volume label for the filesystem. |
| -C or --enable-compression | Enable compression on the volume. |
| -n or --no-action | Causes MKNTFS to not actually create a filesystem, but display what it would do if it were to create a filesystem. All steps of the format are carried out except the actual writing to the device. |
- Advanced options
| -c, --cluster-size BYTES | Specify the size of clusters in bytes. Valid cluster size values are powers of two, with at least 256, and at most 65536 bytes per cluster. If omitted, MKNTFS uses 4096 bytes as the default cluster size.
Note that the default cluster size is set to be at least equal to the sector size as a cluster cannot be smaller than a sector. Also, note that values greater than 4096 have the side effect that compression is disabled on the volume (due to limitations in the NTFS compression algorithm currently in use by Windows). | ||||||||||
| -s, --sector-size BYTES | Specify the size of sectors in bytes. Valid sector size values are 256, 512, 1024, 2048 and 4096 bytes per sector. If omitted, MKNTFS attempts to determine the sector-size automatically and if that fails a default of 512 bytes per sector is used. | ||||||||||
| -p, --partition-start SECTOR | Specify the partition start sector. The maximum is 4294967295 (2^32-1). If omitted, MKNTFS attempts to determine part-start-sect automatically and if that fails a default of 0 is used. Note that part-start-sect is required for Windows to be able to boot from the created volume. | ||||||||||
| -H, --heads NUM | Specify the number of heads. The maximum is 65535 (0xffff). If omitted, MKNTFS attempts to determine the number of heads automatically and if that fails a default of 0 is used. Note that heads is required for Windows to be able to boot from the created volume. | ||||||||||
| -S, --sectors-per-track NUM | Specify the number of sectors per track. The maximum is 65535 (0xffff). If omitted, MKNTFS attempts to determine the number of sectors-per-track automatically and if that fails a default of 0 is used. Note that sectors-per-track is required for Windows to be able to boot from the created volume. | ||||||||||
| -z, --mft-zone-multiplier NUM | Set the MFT zone multiplier, which determines the size of the MFT zone to use on the volume. The MFT zone is the area at the beginning of the volume reserved for the master file table (MFT), which stores the on disk inodes (MFT records). It is noteworthy that small files are stored entirely within the inode; thus, if you expect to use the volume for storing large numbers of very small files, it is useful to set the zone multiplier to a higher value. Note, that the MFT zone is resized on the fly as required during operation of the NTFS driver but choosing a good value will reduce fragmentation. Valid values are 1, 2, 3 and 4. The values have the following meaning:
| ||||||||||
| -T or --zero-time | Fake the time to be 00:00:00 UTC, Jan 1, 1970 instead of the current system time. This is only really useful for debugging purposes. | ||||||||||
| -U or --with-uuid | Generate a random volume UUID. | ||||||||||
| -I or --no-indexing | Disable content indexing on the volume. (This is only meaningful on Windows 2000 and later. Windows NT 4.0 and earlier ignore this as they do not implement content indexing at all.) | ||||||||||
| -F or --force | Force MKNTFS to run, even if the specified device is not a block special device, or appears to be mounted. |
- Output options
| -q or --quiet | Quiet execution; only errors are written to stderr, no output to stdout occurs at all. Useful if MKNTFS is run in a script. |
| -v or --verbose | Verbose execution. |
| --debug | Really verbose execution; includes the verbose output from the -v option as well as additional output useful for debugging MKNTFS. |
- Help options
| -V or --version | Print the version number of MKNTFS and exit. |
| -l or --license | Print the licensing information of MKNTFS and exit. |
| -h or --help | Show a list of options with a brief description of each one. |
- Known Issues
When applying CHKDSK to a file system, it sometimes throws a warning "Correcting errors in the uppercase file." The uppercase file is created while formatting and it defines the mapping of lower case characters to upper case ones, as needed to sort file names in directories. The warning means that the uppercase file defined on the file system is not the same as the one used by the Windows OS on which chkdsk is running, and this may happen because newer versions of Windows take into account new characters defined by the Unicode consortium.
Currently, MKNTFS creates the uppercase table so that no warning is thrown by Windows Vista, Windows 7 or Windows 8. A warning may be thrown by other Windows versions, or if chkdsk is applied in succession on different Windows versions.
MOUNT
Makes a device connected to the system available.
- Format
- MOUNT <device|pattern> [FROM <filename>] [QUIET] [REPLACE] [STARTUP <parameters>]
- Template
- DEVICE/A/M,FROM/K,DEBUG/S,QUIET/S,REPLACE/S,STARTUP/K/F
- Location
- C:
MOUNT causes AmigaDOS to recognize devices connected to the system. When the MOUNT command is issued, MOUNT looks in the DEVS:MountList file (or the optional FROM file) for the parameters of the device that is being mounted. It also looks for mount files named according to the respective device in the directories "DEVS:DOSDrivers" and "SYS:Storage/DOSDrivers". MOUNT commands are usually placed in the Startup-Sequence file.
In place of a device name, a wildcard pattern can be used to identify the names of the mount files to be used. For example, to mount all devices in "DEVS:DOSDrivers" you would use the following command:
1> Mount DEVS:DOSDrivers/~(#?.info)
MOUNT will complain if the device to be mounted has already been mounted (the warning message can be hidden by using the QUIET option). If you actually wanted to remount the device, perhaps with new parameters, you can use the REPLACE option: this will have the same effect as issuing the "ASSIGN <device name> DISMOUNT" command before the respective device is mounted again. Note that this is not normally a good idea since only few file systems and handlers will support it.
Some handlers need to receive additional instructions when they are started. Traditionally, such information goes into the mount file, following the "STARTUP = " text. At times it is more convenient to pass these instructions directly on the MOUNT command line, which then are passed down to the handler. This is what the STARTUP option will do. Note that all devices given on the MOUNT command line will receive these startup instructions and that these instructions will never override the startup instructions given in the mount file, etc.
MOUNT will look in both the mount file and in the tooltypes of the mount file icon for keywords. The DEBUG switch can be used to tell MOUNT that it shall complain about unknown tooltypes or tooltypes which are missing an equal sign.
MOUNTINFO
Creates mount files for the file systems.
- Format
- MOUNTINFO [<device>] [[TO=<file name> [ADDICON]] [ACTIVATE] [DEBUG]
- Template
- DEVICE/A,TO/K,ADDICON/S,ACTIVATE/S,DEBUG/S
- Location
- C:
MOUNTINFO gathers information on a device in order to create a mount file for it which can later be used to mount that device again. This is useful for removable media or data recovery in case the partition information for a hard disk was destroyed, but the contents of the partition survived.
In addition to creating mount files, MOUNTINFO can also provide debugging information for software developers and customer support.
The options are:
| DEVICE | This must be the name of the device to provide mount information for. It must be a device name with a trailing ':' character, such as "DF0:". |
| TO | This option tells MOUNTINFO to write the mount file data to a named file rather than just printing it on the console window. |
| ADDICON | If you told MOUNTINFO to write the mount file data to a named file, you might want to have an icon added to it as well, so that you can drop the resulting mount file into the "SYS:Storage/DOSDrivers" or "DEVS:DOSDrivers" drawers for later use. MOUNTINFO will try to use the default mount file icon stored in "ENV:sys/def_mountfile.info" and revert to use a generic project icon if the mount file icon cannot be found. |
| ACTIVATE | If this option is used MOUNTINFO will store the mount file in a manner which will activate the file system as soon as it has been mounted. If an icon is added to the mount file (by using the ADDICON option) then the "Activate=Yes" tool type will be added to the icon. If the ADDICON is not used, the "Activate=Yes" line will be added to the end of the mount file data. |
| DEBUG | If this option is used, the TO and ADDICON options will be ignored. The mount information for the device, assignment or volume you provided will be gathered and printed in a special format instead, suitable for use by software developers and customer support. For disk drives the MOUNTINFO command will try to determine which file system is responsible for managing the volume and print both the signature of the file system assigned to the volume and the signature of the file system, as stored on the first block of the partition. Note that not all file systems store a signature value in the first block of the partition, so the information provided may not be relevant. |
| NOTES | Not all file system devices can be asked to provide mount information. An exception is, for example, the RAM: device. |
- Example 1
1> MOUNTINFO DF0: \* DF0: (02/03/06 12:51 PM) *\ Surfaces = 2 SectorsPerTrack = 11 LowCyl = 0 HighCyl = 79 BufMemType = 1 MaxTransfer = 2097152 Mask = 0x7FFFFFFE BootPri = 5 BootBlocks = 2 Device = "trackdisk.device" GlobVec = 0
- Example 2
1> MOUNTINFO RAM: RAM: object is not of required type
- Example 3
1> MOUNTINFO WB_2.x: DEBUG
dol_Type = DLT_DEVICE
dol_Task = 0x802B6CC
dol_Lock = NULL
dol_Handler = NULL
dol_StackSize = 600
dol_Priority = 10
fssm_Device = "scsi.device"
fssm_Unit = 0
fssm_Flags = 0
de_TableSize = 16
de_SizeBlock = 512 bytes
de_SecOrg = 0
de_Surfaces = 19
de_SectorPerBlock = 1
de_BlocksPerTrack = 240
de_Reserved = 2
de_PreAlloc = 0
de_Interleave = 0
de_LowCyl = 2
de_HighCyl = 46
de_NumBuffers = 100
de_BufMemType = MEMF_ANY
de_MaxTransfer = 16777215
de_Mask = 0x7FFFFFFE
de_BootPri = 1
de_DosType = DOS\1 0x444F5301
(different signature on disk = DOS\3 0x444F5303)
dol_SegList = 0xF9DC44
dol_GlobVec = 0
dol_Name = "WB_2.x"
MOVE
Moves files or directories.
- Format
- MOVE [FROM] {<name|pattern>} [TO] <name> [QUIET] [BUF|BUFFER=<n>]
- [NOREQ] [NOREPLACE] [INTERACTIVE] [FORCE] [COPYLINKS] [FOLLOWLINKS]
- Template
- FROM/A/M,TO/A,QUIET/S,BUF=BUFFERS/K/N,NOREQ/S,NOREPLACE/S,INTERACTIVE/S,FORCE/S,COPYLINKS/S,FOLLOWLINKS/S
- Location
- C:
MOVE copies the file or directory specified with the FROM argument to the file or directory specified by the TO argument, removing the source file after the copy has been created (thus, 'moving' the files). You can move several items at once by giving more than one FROM argument; each argument should be separated by spaces. You can use pattern matching to move or exclude items whose names share a common set of characters or symbols.
If a TO filename already exists, MOVE overwrites the TO file with the FROM file. If you name a destination directory that does not exist, MOVE will create a directory with that name. You can also use a pair of double quotes ("") to refer to the current directory when specifying a destination. (Do not put any spaces between the double quotes.)
If the FROM argument is a directory, its files, subdirectories, and the subdirectories' files will be moved. If you want to move a directory and you want the copy to have the same name as the original, you must include the directory name in the TO argument.
MOVE prints to the screen the name of each file as it is moved. This can be overridden by the QUIET option or the local shell variable _Verbosity with a negative value.
The BUF= option is used to set the number of 512-byte buffers used during the copy. (Default is 200 buffers, approximately 100K of RAM.) It is often useful to limit the number of buffers when copying to RAM:. BUF=0 uses a buffer the same size as the file to be copied.
The options are:
| NOREPLACE | Checks if the destination file already exists. If this is the case, then the file is not moved. |
| INTERACTIVE | Checks if the destination file already exists. In this case, you will be prompted to confirm that you want the file to be overwritten (answer 'y' for 'yes'). |
| FORCE | If the destination file could not be created because there already is a file of that name which is protected against deletion or writing, then the protection will be removed first before the destination file is created. |
| COPYLINKS | If files need to be copied, copy the contents of a file referenced by a hard or soft link; the default is to skip copying linked files. |
| FOLLOWLINKS | Follow hard and soft links to directories; the default is to skip links to directories.
Normally, MOVE displays a requester if the MOVE cannot continue for some reason. When the NOREQ option is given, all requesters are suppressed. This is useful in scripts and can prevent a MOVE failure from stopping the script while it waits for a response. For instance, if a script calls for a certain file to be moved and the system cannot find that file, normally the script would display a requester and would wait until a response was given. With the NOREQ option, the MOVE command would be aborted and the script would continue. |
- Example 1
1> MOVE File1 TO :Work/File2
moves File1 in the current directory to File2 in the Work directory.
- Example 2
1> MOVE (#?.info) TO DF1:Backup
moves all the files not ending in .info in the current directory to the Backup directory on the disk in DF1:. This is a convenient use of pattern matching to save storage space when icons are not necessary.
- Example 3
1> MOVE Work:Test TO DF0:Test
moves all the files and any subdirectories of the Test directory on Work to the Test directory on DF0:. If a Test directory does not already exist on DF0:, AmigaDOS will create one.
- Example 4
1> MOVE DF0: TO DF1: QUIET
moves all files and directories on the disk in DF0: to DF1:, without displaying on the screen any file/directory names as they are moved.
NETLOGVIEWER
Captures any debug or notification messages sent by the bsdsocket.library or its clients.
- Format
- NETLOGVIEWER [<popup key>] [<priority>] [CX_POPUP=<no | yes>]
- Template
- CX_POPKEY/K,CX_PRIORITY/K/N,CX_POPUP/K
- Location
- C:
Normally, any message that bsdsocket.library or its clients produce is displayed in a console window. This program will capture and display any of these messages in a special window where the messages can be reviewed and even saved to disk.
The options are:
| CX_POPKEY | Key combination to be pressed in order to show the log message window. Default is "shift alt f8". |
| CX_PRIORITY | Priority this tool's input event handler has in the Commodities filter chain. Default is 0, which should not be changed. |
| CX_POPUP | Whether or not the log window should appear when the program is first started. Defaults to "yes" (use "no" to hide the window) |
| Note |
|---|
| The NETLOGVIEWER program can be started from Workbench, too. In this case it will check its icon for tool types whose names and purposes match the command template described above. |
| Note |
|---|
| You can and should start the NETLOGVIEWER program before you add the first networking interface (in order to capture any error output). Note, however, that if you shut down the bsdsocket.library (by using the NETLOGVIEWER command) the NETLOGVIEWER program will exit, too. |
NETSHUTDOWN
Shuts down the network in an orderly fashion.
- Format
- NETSHUTDOWN [<seconds>] [QUIET]
- Template
- TIMEOUT/N,QUIET/S
- Location
- C:
The command will stop all running interfaces. The options are:
| TIMEOUT | How many seconds this command should wait until it gives up. By default, it will wait up to 5 seconds for the network to shut down once it has triggered the shutdown process. |
| QUIET | Use this parameter to stop the command from reporting what it is currently doing. |
The NETSHUTDOWN command will trigger the shutdown process of the network. This process cannot be stopped once it has started. However, this command can make an attempt to wait until the shutdown has completed. Normally, the shutdown should be finished in a fraction of a second, but at times when other clients still hang onto the network resources, the shutdown can fail to complete quite so quickly. In that case, the NETSHUTDOWN command will tell you that it could not complete its task within the allocated time frame (within five seconds, or whatever timeout you specified). The shutdown, however, will proceed and may conclude at a later time.
When this command starts up it begins by checking if the network is currently operational. If this is not the case, it will exit immediately, printing a message to this effect.
- See also
NEWCLI
Opens a new Shell window.
- Format
- NEWCLI [<window specification>] [FROM <filename>]
- Template
- WINDOW,FROM
- Location
- Internal
NEWCLI starts a new Shell process. It is the same as using the NEWSHELL command.
NEWSHELL
Opens a new Shell window.
- Format
- NEWSHELL [<window specification>] [FROM <filename>]
- Template
- WINDOW,FROM
- Location
- Internal
The new Shell window becomes the currently-selected window and process. The new window has the same current directory, prompt string, path, local environment variables, and stack size as the one from which it is invoked. However, each Shell window is independent, allowing separate input, output, and program execution.
The window can be sized, dragged, zoomed, and depth-adjusted like most other Amiga windows.
To create a custom window, you can include the <window specification> argument. Specify the initial dimensions, location, and title of the window with this <window specification> syntax:
CON:x/y/width/height/title/options
where:
| x | Is the number of pixels from the left edge of the screen to the left border of the Shell window. Use a value (//) to specify the minimum possible pixels. |
| y | Is the number of pixels from the top of the screen to the top of the Shell window. Use no value (//) to specify the minimum possible pixels. |
| width | Is the width of the Shell window, in pixels. Use no value (//) to specify the full width of the screen. |
| height | Is the height of the Shell window, in pixels. Use no value (//) to specify minimum possible height. |
| title | Is the text that appears in the Shell window title bar. |
Use slashes to separate the parameters and options. If any spaces appear in the specification argument, the entire argument must be enclosed in double quotation marks (").
The allowable options are:
| AUTO | The window automatically appears when the program needs input or produces output. With the Shell window, it opens for input immediately. The window can only be closed with the ENDSHELL command. Selecting the Shell's close gadget closes the window, but it re-opens immediately since it is expecting input. |
| ALT | The window appears in the specified size and position when the zoom gadget is clicked. The four parameters must be separated with slashes (for example, ALT30/30/200/200). |
| BACKDROP | The window appears on the backdrop, behind all the Workbench windows. This Shell window cannot be brought to the front of the screen; you have to resize the Workbench windows to see it. |
| CLOSE | The window has all the standard gadgets, including a close gadget. This is the default for Shell windows, but you must specify it to get a standard Shell if you use the WINDOW argument. |
| INACTIVE | The window opens, but is not made the active window. |
| NOBORDER | The window opens without any left or bottom window border. Only the zoom, depth, and sizing gadgets are available. |
| NOCLOSE | The window does not have a close gadget. If you open a console normally, there is no close gadget. If you open a console using the AUTO option, there is automatically a close gadget on the window. |
| NODEPTH | The window has no window depth gadget. |
| NODRAG | The window cannot be dragged. It has zoom, depth and sizing gadgets, but no close gadget. |
| NOSIZE | The window only has a depth gadget. |
| SCREEN | The window opens on a public screen. The screen must already exist. You must specify the name of the screen after the SCREEN keyword. |
| SIMPLE | If you enlarge the window, the text expands to fill the newly available space, allowing you to see text that had been scrolled out of the window. This is the default for standard Shells. |
| SMART | If you enlarge the window, the text does not expand to fill the newly available space. This saves memory. |
| WAIT | The window can only be closed by selecting the close gadget or entering Ctrl-\. If WAIT is the only option, there is no close gadget. |
NEWSHELL uses the default startup file S:Shell-startup, unless a FROM file name is specified. S:Shell-startup is a standard AmigaDOS script file. For example, you can have several different Shell-startup files, each having different command aliases. You can call such customized Shell environments with FROM.
The NEWCLI command has the same effect as NEWSHELL; it invokes a new Shell process.
- Example 1
1> NEWSHELL
opens a new Shell window with the default window specification.
- Example 2
1> NEWSHELL "CON://640/200/My Shell/CLOSE"
A window starting in the upper left corner of the screen and measuring 640 pixels wide and 200 pixels high opens. The window is titled My Shell and it has a close gadget. The entire argument is enclosed in quotation marks because the title contains a space. If you add the command to your User-startup file, a Shell window opens automatically when your Amiga is booted.
- Example 3
1> NEWSHELL FROM S:Programming.startup
opens a new Shell, but instead of executing the Shell-startup file, the Programming.startup file is executed. You can have aliases and prompt commands in the Programming.startup file that are used only when you are programming.
For more examples using NEWSHELL, see Chapter 8.
NTFSCAT
Prints NTFS files and streams.
- Format
- NTFSCAT [options] <device> [<file>]
- Template
- -a=--attribute,-n=--attribute-name,-i=--inode,-f=--force,-h=--help,-q=--quiet,-V=--version,-v=--verbose,DEVICE,FILE
- Location
- C:
NTFSCAT reads a file or a stream from an NTFS volume and displays the content on the standard output.
The case of the filename passed to NTFSCAT is ignored.
Below is a summary of all the options that NTFSCAT accepts. Nearly all options have two equivalent names. The short name is preceded by - and the long name is preceded by --. Any single letter options, that don’t take an argument, can be combined into a single command, e.g. -fv is equivalent to -f -v. Long named options can be abbreviated to any unique prefix of their name.
| -a <type> or --attribute <type> | Display the contents of a particular attribute type. By default, the unnamed $DATA attribute will be shown. The attribute can be specified by a number in decimal or hexadecimal, or by name.
| |||||||||||||||||||||||||||||||||||||||||||||||||||||
| -n <name> or --attribute-name <name> | Display this named attribute, stream. | |||||||||||||||||||||||||||||||||||||||||||||||||||||
| -i <number> or --inode <number> | Specify a file by its inode number <number> instead of its name. | |||||||||||||||||||||||||||||||||||||||||||||||||||||
| -f or --force | This will override some sensible defaults, such as not using a mounted volume. Use this option with caution. | |||||||||||||||||||||||||||||||||||||||||||||||||||||
| -h or --help | Show a list of options with a brief description of each one. | |||||||||||||||||||||||||||||||||||||||||||||||||||||
| -q or --quiet | Suppress some debug/warning/error messages. | |||||||||||||||||||||||||||||||||||||||||||||||||||||
| -V or --version | Show the version number, copyright and license ntfscat. | |||||||||||||||||||||||||||||||||||||||||||||||||||||
| -v or --verbose | Display more debug/warning/error messages. |
- Example 1
Display the contents of a file in the root of an NTFS volume.
1> ntfscat /dev/hda1 boot.ini
- Example 2
Display the contents of a file in a subdirectory of an NTFS volume.
1> ntfscat /dev/hda1 /winnt/system32/drivers/etc/hosts
- Example 3
Display the contents of the $INDEX_ROOT attribute of the root directory (inode 5).
1> ntfscat /dev/hda1 -a INDEX_ROOT -i 5 | hexdump -C
NTFSCK
?
- Format
- ?
- Template
- ?
- Location
- C:
Missing description.
NTFSCLUSTER
?
- Format
- ?
- Template
- ?
- Location
- C:
Missing description.
NTFSFIX
?
- Format
- ?
- Template
- ?
- Location
- C:
Missing description.
NTFSINFO
?
- Format
- ?
- Template
- ?
- Location
- C:
Missing description.
NTFSLABEL
?
- Format
- ?
- Template
- ?
- Location
- C:
Missing description.
NTFSLS
?
- Format
- ?
- Template
- ?
- Location
- C:
Missing description.
NTFSUNDELETE
?
- Format
- ?
- Template
- ?
- Location
- C:
Missing description.
NTFSWIPE
?
- Format
- ?
- Template
- ?
- Location
- C:
Missing description.
NVGETVAR
Prints the value of all or a named UBoot environment variable.
- Format
- NVGETVAR <name>
- Template
- NAME
- Location
- C:
NVGETVAR <name> will print the value of the UBoot environment variable "name". If nothing is provided for the <name>, all variables are printed.
If the requested variable does not exists, NVGETVAR will print nothing, and set the condition flag to 5 (WARN).
- Example
1> NVGETVAR boot_config AmigaOS 4.1 FE
prints the value of the boot_config variable.
NVSETVAR
Set the value of, create, or delete a named UBoot environment variable.
- Format
- NVSETVAR <name> <value>
- Template
- NAME/A,VALUE/F
- Location
- C:
NVSETVAR <name> <value> will set the value of the UBoot environment variable <name>. If <name> exists and nothing is provided for the <value>, the variable <name> will be deleted. If <name> does not exist and something is provided for the <value>, a new variable <name> with a value <value> will be created.
If the variable <name> is not provided, or does not exist and no <value> is provided, NVSETVAR will print nothing, and set the condition flag to 5 (WARN).
- Example
1> NVSETVAR boot_config "AmigaOS 4.1 FE"
Sets the value of the boot_config variable to "AmigaOS 4.1 FE".
OPENSSL
?
- Format
- ?
- Template
- ?
- Location
- C:
Missing description.
OWNER
Changes the ownership of a file or directory.
- Format
- OWNER [FILE] {<file | pattern>} [OWNER] <name or number> [ALL] [QUIET]
- Template
- FILE/A/M,OWNER/A,ALL/S,QUIET/S
- Location
- C:
Each file or directory bears information which describes who owns it. This information can be displayed by the LIST command. The ownership of a file or a directory is important when the file or directory is made accessible through a networked file system.
The OWNER command will change the ownership of one or more files or directories. The "owner" must be given either as a name or a number. The file system needs to understand the given name. If not, you will see an error message. If you know which numeric owner ID should be used in place of a name, you can provide this instead. Note that owner names cannot be longer than 31 characters and that numeric owner IDs must be in the range of 0 to 65535. An empty name given for the owner will remove the ownership information.
The options are:
| ALL | If the ALL option is given, OWNER will change the ownership of all the files in the specified directory. |
| QUIET | If the QUIET option is given, screen output is suppressed. The local shell variable _Verbosity with a negative value has the same effect. |
- Example 1
1> OWNER textfile admin
Assigns the ownership of "textfile" to the user "admin".
- Example 2
1> OWNER textfile ""
Removes any ownership information from "textfile".
PATH
Controls the directory list that the Shell searches to find commands.
- Format
- PATH [{<dir>}] [ADD] [SHOW] [RESET] [REMOVE] [QUIET]
- Template
- PATH/M,ADD/S,SHOW/S,RESET/S,REMOVE/S,QUIET/S
- Location
- Internal
PATH lets you see, add to, or change the search path the AmigaDOS follows when looking for a command or program to execute. When a directory is in the search path, you do not need to specify the complete path to any command within that directory. Entering the name alone makes AmigaDOS look through the directories in the search path until it finds the file.
| Note |
|---|
| The search path is only relevant when AmigaDOS is searching for a command or program to execute. Full path specifications are always necessary in arguments for commands such as COPY and DELETE. |
Enter the PATH command alone or with the SHOW option to display directory names in the current search path. Normally, when PATH is displaying the directory names, a requester appears if a volume that is part of the search path cannot be found. For example, if you add a floppy disk to the search path and then remove that disk from the disk drive, a requester asks you to insert the disk.
If you specify the QUIET option, PATH does not display requesters for volumes that are not currently mounted. If PATH encounters an unmounted volume, it displays the message device (or volume) is not mounted . The names of any directories on that volume included in the PATH are not displayed.
The ADD option specifies directory to be added to the current PATH. You can add any number of directories with one PATH ADD command (the ADD keyword is optional); names of the directories must be separated by at least one space. When you issue the PATH command, AmigaDOS searches for each of the ADDed directories.
To replace the existing search path with a new one, use PATH RESET followed by the names of the new directories. The existing search path, except for the current directory and C:, is erased and the new one is substituted.
The REMOVE option eliminates the named directory from the search path.
- Example
1> PATH EXTRAS:Tools ADD
adds the Tools directory in the Extras drawer to the search path of the Shell. If the EXTRAS: is not in a disk drive, a requester asks you to insert it in any drive.
If you remove EXTRAS: from the drive and enter:
1> PATH
a list of directories in the search path is displayed. A requester asks you to insert EXTRAS:. If you enter:
1> PATH QUIET
the list of directories in the search path is displayed. However, when the path comes to Extras:Tools, the error message appears in the list.
- See also
PATHPART
Splits and assembles directory and file names.
- Format
- PATHPART [DIR <path name>] [FILE <path name>] [ADD {<directory name | file name}]
- Template
- DIR/K,FILE/K,ADD/K/N
- Location
- C:
PATHPART can break down directory and file names into their respective directory and file name components, and is also able to (re-) assemble the individual names into combined path names again. This can be of great use in script files.
- Example 1
Obtain the directory name component of a path name:
1> PATHPART DIR Work:Files/Data Work:Files
- Example 2
Obtain the file name component of a path name:
1> PATHPART FILE Work:Files/Data Data
- Example 3
Build a complete path name from components:
1> PATHPART ADD Work: Files Data Work:Files/Data
- Example 4
Remove the last part of a path name, then replace it with a new name:
1> PATHPART ADD `PATHPART DIR Work:Files/Data` Information Work:Files/Information
PETUNE
Changes the debug options of the Motorola 68040 CPU emulation.
- Format
- ?
- Template
- GLOBALDEBUGLEVEL=GDL/K/N,DEBUGLEVEL=DL/K/N,DEBUGOFFSET=DO/K,INSTSTATS/K,EMULATOR=EMU/K,SEGMENTLIST=SL/S
- Location
- C:
Missing description.
PING
Sends ICMP ECHO_REQUEST packets to network hosts.
- Format
- PING [-c | COUNT <number>] [-d | DEBUG] [-i | INTERVAL <wait>]
- [-l | LOAD <preload>] [-n | NUMERICONLY | NUMERIC] [-q | QUIET]
- [-R | RECORDROUTE] [DONTROUTE] [-s | SIZE <packet size>]
- [-v | VERBOSE] [BELL] [HOST] <host name or IP address>
- Template
- -c=COUNT/K/N,-d=DEBUG/S,-i=INTERVAL/K/N,-l=LOAD/K/N,-n=NUMERICONLY/S=NUMERIC/S,-q=QUIET/S,-R=RECORDROUTE/S,DONTROUTE/S,-s=SIZE/K/N,-v=VERBOSE/S,BELL/S,HOST/A
- Location
- C:
Missing description.
PIPE
Connects input and output streams of Shell commands.
- Format
- PIPE <command>
- Template
- COMMAND/A/F
- Location
- Internal
The PIPE command is used by the shell to connect the input and output streams of shell commands. It is not useful beyond that point and should not be used by user shell scripts.
Warning
The PIPE command may be removed in a future shell version.
POOLSTAT
?
- Format
- ?
- Template
- ?
- Location
- C:
Missing description.
POPCD
Returns the directory last recently saved with the PUSHCD command.
- Format
- POPCD
- Template
- (none)
- Location
- Internal
POPCD is the counterpart to the PUSHCD command. It will recall the directory least recently saved by PUSHCD and return to it. If no directory can be popped from the stack, PUSHCD will return to the SYS: directory instead.
- See also
PROMPT
Changes the prompt string of the current Shell.
- Format
- PROMPT [<prompt>]
- Template
- PROMPT
- Location
- Internal
PROMPT allows you to customize the prompt string, the text printed by the Shell at the beginning of a command line. The prompt string can contain any characters, including escape sequences.
This manual shows the prompt string as 1>.
The default prompt string is:
"%N.%S>"
which displays the Shell number, a period, the current directory, a right angle-bracket, and a space. Entering PROMPT without a string argument resets the prompt to this default.
The substitutions available for the <prompt> string are:
| %N | Displays the process number for the Shell. |
| %S | Displays the current directory. |
| %R | Displays the return code for the last operation. |
A space is not automatically added to the end of the string. If you want a space between the prompt and typed-in text, place it in the string, and enclose the string in double quotation marks,
You can embed commands in the prompt string by enclosing the command in back apostrophes (`).
- Example 1
1> PROMPT %N 1
Only the Shell number is shown. The > is removed from the prompt.
- Example 2
1> PROMPT "%N.%S.%R>" 1.Work:Snim.0>
The Shell number, current directory, and return code of the previous command are shown. A space is included after the >.
For more examples using the PROMPT command, see Chapter 8.
PROTECT
Changes the protection bits of a file or directory.
- Format
- PROTECT [FILE] <file|pattern> [FLAGS] [+|-] [<flags>] [CLEAR] [FILES] [DIRS]
- Template
- FILE/A,FLAGS,ADD/S,SUB/S,ALL/S,QUIET/S,USER/S,GROUP/S,OTHER/S,CLONE/S,CLEAR/S,FILES/S,DIRS/S
- Location
- C:
All files have a series of protection bits stored with them which control their attributes. These bits can be altered to indicate the type of file and the file operations permitted. PROTECT is used to set or clear the protection bits of a file.
The protection bits are represented by letters:
| r | The file can be read. |
| w | The file can be written to (altered). |
| e | The file is executable (a program). |
| d | The file can be deleted. |
| s | The file is a script. |
| p | The file is a pure command and can be made resident. |
| a | The file has been archived. |
| h | The command file should be held resident in memory after it has been used (requires that the 'p' bit is set, too) |
To see the protection bits associated with a file, use the LIST command. The protection field is displayed with set (on) bits shown by their letters and clear (off) bits shown by hyphens. For instance, a file that is readable, writable and deletable, will have ----rw-d in the protection field.
To specify the entire protection field at once, simply give the letters of the bits you want set as the FLAGS argument, without any other keywords. The named bits will be set, and all the others will be cleared.
The symbols + and - (or the equivalent keywords ADD and SUB) are used to control specific bits without affecting the state of unspecified bits. Follow + or - with the letter(s) of the bit(s) to set or clear, respectively, and only those bits will be changed. Don't put a space after the symbol or between the letters. The order of the letters does not matter. ADD and SUB work similarly, but there must be a space between the keyword and the letter(s). You cannot both set and clear bits in the same command.
The options are:
| ALL | Change the protection bits of all subdirectories and their files. |
| QUIET | Do not display progress report messages. The local shell variable _Verbosity with a negative value has the same effect. |
| USER | Only modify the 'user' protection bits (default). |
| GROUP | Only modify the 'group' protection bits |
| OTHER | Only modify the 'other' protection bits. |
| CLONE | Change the 'group' and/or 'other' protection bits to the same value as the 'user' protection bits. Requires at least one of the USER and GROUP options, and no protection bits specified. |
| CLEAR | Clear all protection bits. |
| FILES | Only change the protection bits of the files found. |
| DIRS | Only change the protection bits of the directories found. |
| Note |
|---|
| The FILES and DIRS options work together: if you use FILES and omit DIRS, then only the files will be affected and the other way round. If none of FILES and DIRS is used, all files and directories will have their protection bits changed. |
| Note |
|---|
Since version 51.9 PROTECT doesnt allow to set the h, s, and p bits of directories. For files,
|
- Example 1
1> PROTECT DF0:Memo +rw
sets only the protection bits r (readable) and w (writable) to the file Memo on DF0:. No other protection bits are changed.
- Example 2
1> PROTECT L:#? e SUB
clears the e (executable) protection bit from all the files in the L: directory.
- Example 3
1> PROTECT Work:Paint rwed
The protection status of Paint becomes "----rwed".
- Example 4
1> PROTECT Work:Write CLONE GROUP OTHER
The group and other protection bits of Write become a copy of the user protection bits.
- Example 5
1> PROTECT Work:Save CLEAR
Clear all the protection bits of Save.
- See also
PUSHCD
Saves the current directory on a stack and optionally changes it.
- Format
- PUSHCD [<dir | pattern>]
- Template
- DIR
- Location
- Internal
PUSHCD saves the current directory on a stack. If an optional directory name or pattern is provided, the current directory will be saved first and then changed. The PUSHCD command can be undone with the POPCD command.
Up to 100 directories can be pushed onto the stack.
- See also
PYTHON
Launches a Python program.
- Format
- PYTHON [<option>] ... [-c <command> | -m <module> | <file> | <stdin>] [<arguments to program>]
- Template
- -c,-d,-E,-h,-i,-m,-O,-OO,-Q,-S,-t,-u,-v,-V,-W,-x,file,args
- Location
- C:
Missing description.
QUIT
Exits from a script file with a specified return code.
- Format
- QUIT [<return code>]
- Template
- RC/N
- Location
- Internal
QUIT stops the execution of the script at the specified return code. The default return code is zero. We recommend you use the standard return code values of 5, 10, and 20.
- Example
ASK "Do you want to stop now?"
IF WARN
QUIT 5
ENDIF
ECHO "OK"
ECHO "The script is continuing."
If you press Y at the prompt, the script is aborted, since WARN is equal to a return code of 5. If you press N or press Return:
OK The script is continuing.
Is displayed in the Shell window.
REBOOT
Reboots your Amiga.
- Format
- REBOOT [FAST=WARMREBOOT] [WAIT=<seconds>] [SYNC]
- Template
- FAST=WARMREBOOT/S,WAIT/N/K,SYNC/S
- Location
- C:
REBOOT will reboot the Amiga system. You can either reboot the machine completely or only the operating system. If you do not use the FAST (WARMREBOOT) argument, your Amiga will be restarted completely.
REBOOT has the same effect as if you turned your Amiga off and on again. If you specify the FAST argument, only AmigaOS will be restarted which will boot AmigaOS again with the same kernel modules.
With the WAIT argument, the reboot can be delayed for a specified number of seconds.
With the SYNC argument, REBOOT will try to inhibit all partitions in order to reboot more safely (with no current disk operations).
- Example 1
To reboot only the operating system after 2 seconds delay:
1> Reboot FAST WAIT 2
- Example 2
To reboot completely after all disk operations are finished:
1> Reboot SYNC
RECORDER
Captures console output and stores it in a file.
- Format
- RECORDER [[TO] <file>] [APPEND] [OFF] [LINE] [SIZE <number>] [FLUSH]
- Template
- TO,APPEND/S,OFF/S,LINE/S,SIZE/N/K,FLUSH/S
- Location
- Internal
Missing description.
RELABEL
Changes the volume name of the disk in the given drive to the specified name.
- Format
- RELABEL [DRIVE] <drive> [NAME] <name>
- Template
- DRIVE/A,NAME/A
- Location
- C:
Volume names are set when disks are initially formatted. RELABEL allows you to change a disk's volume name to any name specified.
On floppy-only systems with one drive, be sure to specify the disks by volume name instead of drive name.
- Example 1
1> RELABEL Workbench: MyDisk
changes the name of the Workbench disk to MyDisk. No colon is necessary after the second name.
- Example 2
1> RELABEL DF2: DataDisk
changes the name of the disk in DF2: to DataDisk.
RELOADAPPLIST
?
- Format
- ?
- Template
- ?
- Location
- C:
Missing description.
REMOVENETINTERFACE
?
- Format
- ?
- Template
- ?
- Location
- C:
Missing description.
REMRAD
Removes the recoverable RAM disk.
- Format
- REMRAD [<device>] [FORCE]
- Template
- DEVICE,FORCE/S
- Location
- C:
REMRAD allows you to remove the recoverable RAM disk (usually mounted as RAD:) from memory without powering off the system. If you have mounted more than one recoverable RAM disk, use the DEVICE specification.
REMRAD instructs RAD: to delete all of its files and become inactive. However, the RAD: RAM_0 disk icon does not disappear. The next time the Amiga is rebooted. RAD: is removed from memory completely and the icon is no longer displayed.
If the device is in use when the REMRAD command is given, the operation aborts with a device in use message. To remove it if it is in use, you must use the FORCE option.
RENAME
Changes the name of or moves a file or directory.
- Format
- RENAME [FROM] {<name} [TO | AS] <name>
- Template
- FROM/A/M,TO=AS/A,QUIET/S
- Location
- C:
RENAME renames the FROM file or directory with the specified TO name. The FROM and TO files or directories must be on the same volume. If the name refers to a directory, RENAME changes the directory name without changing the names of the files or subdirectories in that directory. When there are multiple items in the FROM argument, the TO argument must be a directory.
If you rename a directory or if you use RENAME to give a file another directory name, AmigaDOS changes the position of that directory or file in the filing system hierarchy. This effectively moves the items.
- Example 1
1> RENAME Work/Ex1 AS :Test/Ex2
renames the file Ex1 as Ex2 and moves it from the Work directory to the Test directory. The Test directory must exist in the root directory for this command to work.
- Example 2
1> RENAME 3.doc 5.doc a.doc TO Docs
moves the 3.doc, 5.doc, and a.doc files to the Docs directory. The Docs directory must already exist.
REQUESTCHOICE
Allows AmigaDOS and ARexx scripts to use custom requesters.
- Format
- REQUESTCHOICE <title text> <body text> {<gadgets>} [TYPE <type>] [TO <file>] [PUBSCREEN <public screen name>] [TIMEOUTSECS <seconds>] [CHARSET <character set>] [INACTIVE]
- Template
- TITLE/A,BODY/A,GADGETS/A/M,TYPE/K,TO/K,PUBSCREEN/K,TIMEOUTSECS/K/N,CHARSET/K,INACTIVE/S
- Location
- C:
The TITLE argument specifies the title of the requester.
The BODY argument specifies the text of the requester. Line feeds can be embedded using *N. For other formatting options see the requester class autodoc: requester_cl.doc
The GADGETS argument specifies the text for the different gadgets. The gadget labels are separated with spaces.
The TYPE argument specifies the type of requester to display. Possible types are INFO, QUESTION, WARNING, ERROR, and INSERTDISK. If not specified, INFO is assumed when a single gadget is specified, QUESTION otherwise.
The TO argument specifies an output file where the result is written to.
The TIMEOUTSECS argument specifies the maximum number of seconds to display the requester before its closed and the result -1 is returned. Specifying 0 timeout seconds means no timeout.
The PUBSCREEN argument allows the requester to open its window on a public screen.
The CHARSET argument allows to specify the character set of the strings given in the BODY and GADGETS arguments. The TITLE argument is always displayed in the character set of the screen font.
The INACTIVE argument specifies that the requester window should not be activated when opened.
The number of the selected gadget is printed as a result to the console or written to the output file. The gadgets are numbered from left to right as 1, 2, 3, ..., 0. The special result -1 is printed when the TYPE argument was INSERTDISK and a disk was inserted. For evaluation in a script file, you can redirect this output into an environment variable. If the requester cannot be opened, the command generates a return code of 20, 0 otherwise.
- Example
1> RequestChoice >ENV:rcnum "New Title" "This is my requester.*nSelect a gadget." "_OK" "_Maybe" "_Cancel"
The local Shell variable rcnum contains 1, 2, or 0 (respectively) after a gadget is selected. The script can use this value to control its later execution.
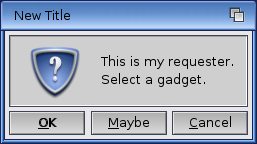
ENV:rcnum contains 0, 1, or 2 after a gadget is selected. The script can use this value to control its later execution.
REQUESTFILE
Allows AmigaDOS and ARexx scripts to use a file requester.
- Format
- REQUESTFILE [DRAWER <drawer name>] [FILE <file>] [PATTERN <pattern>] [TITLE <title>] [POSITIVE <text>] [NEGATIVE <text>] [ACCEPTPATTERN <pattern>] [REJECTPATTERN <pattern>] [SAVEMODE] [MULTISELECT] [DRAWERSONLY] [NOICONS] [PUBSCREEN <public screen name>]
- Template
- DRAWER,FILE/K,PATTERN/K,TITLE/K,POSITIVE/K,NEGATIVE/K,ACCEPTPATTERN/K,REJECTPATTERN/K,SAVEMODE/S,MULTISELECT/S,DRAWERSONLY/S,NOICONS/S,PUBSCREEN/K
- Location
- C:
When entered with no arguments, a file requester with OK, Volumes, Parent, and Cancel buttons is created. Ist Drawer and File gadgets are empty and it displays the contents of the current directory.
The DRAWER argument specifies the initial contents of the Drawer gadget.
The FILE option specifies the initial contents of the File gadget.
The PATTERN option allows the use of a standard AmigaDOS pattern. It includes a Pattern gadget in the requester and specifies the initial contents of the gadget. If this option is not provided, the file requester does not have any Pattern gadget.
The TITLE option specifies the title of the requester.
The POSITIVE option specifies the text to appear in the positive (left) choice in the file requester.
The NEGATIVE option specifies the text to appear in the negative (right) choice in the file requester.
The ACCEPTPATTERN option specifies a standard AmigaDOS pattern. Only files matching this pattern are displayed in the file requester.
The REJECTPATTERN option specifies a standard AmigaDOS pattern. Files matching this pattern are not displayed in the file requester.
If SAVEMODE is specified, the requester is used for writing files to disk. If MULTISELECT is specified, the requester allows multiple files to be selected at once. If DRAWERSONLY is specified, the requester does not have a File gadget. This effectively turns the file requester into a directory requester. If NOICONS is specified, the requester does not display icons (.info files).
The selected files are returned on the command line, enclosed in double quotation marks and separated with spaces. The command generates a return code of 0 if you select a file or 5 if you cancel the requester.
The PUBSCREEN argument allows the requester to open its window on a public screen.
- Example
1> REQUESTFILE DRAWER Devs: TITLE "My Req" NOICONS
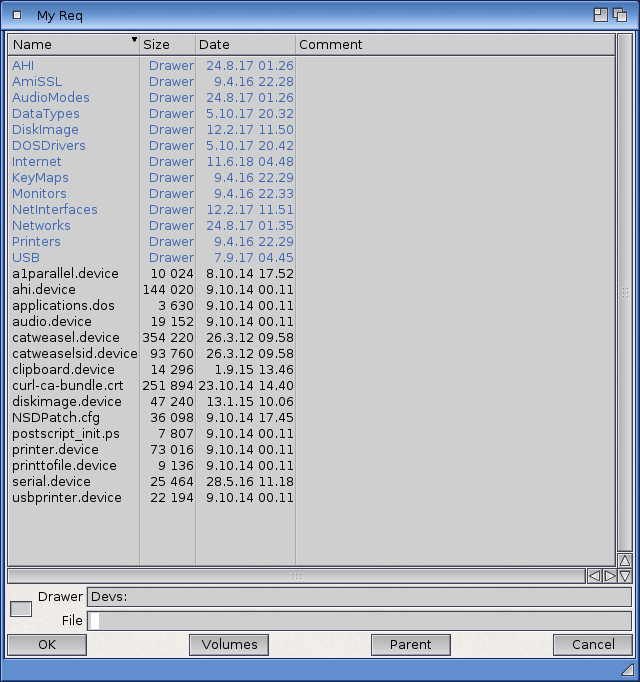
REQUESTSTRING
Allows AmigaDOS and ARexx scripts to use custom string requesters.
- Format
- REQUESTSTRING <title text> <body text> [POSITIVE <OK gadget text>] [NEGATIVE <Cancel gadget text>] [DEFSTRING <default text>] [MAXLEN=<n>] [NOTEMPTY] [INVISIBLE] [TO <filename>] [PUBSCREEN <public screen name>] [CHARSET <character set>] [INACTIVE]
- Template
- TITLE/A,BODY/A,POSITIVE/K,NEGATIVE/K,DEFSTRING/K,MAXLEN/K/N,NOTEMPTY/S,INVISIBLE/S,TO/K,PUBSCREEN/K,CHARSET/K,INACTIVE/S
- Location
- C:
The TITLE argument specifies the title of the requester.
The BODY argument specifies the text of the requester. Line feeds can be embedded using *N. For other formatting options see the requester class autodoc: requester_cl.doc
The POSITIVE argument specifies the text for the OK gadget. Default is the localized "_OK" text.
The NEGATIVE argument specifies the text for the Cancel gadget. Default is the localized "_Cancel" text.
The DEFSTRING argument specifies the default text for the string gadget. Default is empty string.
The MAXLEN argument specifies the maximum length of the string. Default is 256. The length does not include the NULL termination, e.g. "A" is considered to have a length of 1. Negative and zero values are silently ignored and replaced with the default value.
The NOTEMPTY switch does not allow the user to enter an empty string.
The INVISIBLE switch specifies that the text in the string gadget should be displayed with '*' characters, e.g. for entering passwords that should not be visible to a person behind the user.
The TO argument specifies the file where to store the result string. If not specified, the string is written to the default output.
The PUBSCREEN argument specifies the name of the public screen where to open the requester window. If not specified, the current default public screen is used. The screen is brought to the front before opening the window if necessary, and to the back after closing the window if it was brought to the front before.
The CHARSET argument allows to specify the character set of the string given in the BODY, POSITIVE, NEGATIVE, and DEFSTRING arguments. The TITLE argument is always displayed in the character set of the screen font.
The INACTIVE argument specifies that the requester window should not be activated when opened.
RequestString will return with RETURN_FAIL (20) on any failure, with RETURN_WARN (5) if the user clicked the Cancel gadget (the result string is the provided default string in this case), and with RETURN_OK (0) otherwise. The result string (or the default string, if the user did cancel the requester) will be enclosed in quotation marks, then terminated with linefeed, and written to the file specified with the TO argument or the default output.
- Example
1> Set Title "Edit file comment" 1> Set Body "Comment for MyFile:" 1> Set Def "`List MyFile LFORMAT %c`" 1> Set Note `RequestString "$Title" "$Body" DEFSTRING "$Def"` 1> FileNote MyFile "$Note"
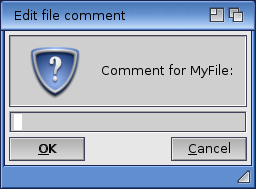
RESIDENT
Displays and modifies the list of resident commands.
- Format
- RESIDENT [<resident name>] [<filename>] [REMOVE] [ADD] [REPLACE] [PURE | FORCE] [SYSTEM]
- Template
- NAME,FILE,REMOVE/S,ADD/S,REPLACE/S,PURE=FORCE/S,SYSTEM/S
- Location
- Internal
RESIDENT loads a command into memory and adds it to the resident list maintained by the Shell. This allows the command to be executed without reloading it from disk each time. If RESIDENT is invoked with no options, it lists the programs on the resident list.
To be made resident, a command should be pure, meaning that it is both re-entrant and re-executable. A re-entrant command can properly support independent use by two or more programs at the same time. A re-executable command dies not have to be reloaded to be executed again. Commands that have these characteristics are called pure and have the p (pure) protection bit set.
The following commands cannot be made resident: BINDDRIVERS, CONCLIP, IPREFS, LOADRESOURCE, LOADWB, and SETPATCH.
LIST the C: directory to check for the presence of the p protection bit to determine which commands are pure.
Many of the commands in the C: directory, as well as the MORE command in Utilities, are pure commands and can be made resident. If a command does not have its pure bit set, it probably cannot be made resident safely. (Setting the pure bit does not make a command or program pure.)
The REPLACE option is the default option and does not need to be explicitly stated. If no <resident name> is specified (for example, only a file name is specified), RESIDENT uses the file name portion as the name on the resident list. The full path to the file must be used.
If a <resident name> is specified and RESIDENT finds a program with that name already on the list, it attempts to replace the command. That <resident name> must be used to reference the resident version of the command. The replacement succeeds only if the already-resident command is not in use.
To override REPLACEment and make several versions of a command resident simultaneously, use the ADD option, giving a different <resident name> for each version loaded.
If the System option is specified, the command is added to the system portion of the resident list and becomes available as a system component. Any commands added to the resident list with the SYSTEM option cannot be removed. To list these files on the RESIDENT list, you must specify the SYSTEM option.
The PURE option forces RESIDENT to load commands that are not marked as pure and use them to test the pureness of other commands and programs. Use the PURE option with caution. Be sure the programs that you make RESIDENT meet the criteria to be resident or be careful to use the command in only one process at a time.
The availability of internal commands can also be controlled with RESIDENT. To deactivate an Internal command (for example, if an application has its own command of the same name), use RESIDENT <command> REMOVE. The command can be reactivated with the REPLACE option.
- Example 1
1> RESIDENT C:COPY
makes the COPY command resident (replaces any previous version).
- Example 2
1> RESIDENT Copy2 DF1:C/COPY ADD
adds another version of COPY to the resident list, under the name Copy2.
- Example 3
1> RESIDENT Xdir DF1:C/Xdir PURE
makes an experimental, non-pure version of the DIR command resident.
- Example 4
1> RESIDENT CD REMOVE
makes the Internal CD command unavailable.
- Example 5
1> RESIDENT CD REPLACE
restores the CD command to the system.
- See also
ROADSHOWCONTROL
Displays and changes the internal configuration options of the TCP/IP stack.
- Format
- ROADSHOWCONTROL [GET <option>] [SET <option>=<value>] [SAVE] [QUIET]
- Template
- GET/K,SET/K/F,SAVE/S,QUIET/S
- Location
- C:
Missing description.
RUN
Executes commands as background processes.
- Format
- RUN <command...> [{+ <command>}]
- Template
- COMMAND/F
- Location
- Internal
RUN is used to start background processes. A background process does not open its own window for input or output and does not take over the parent Shell.
RUN attempts to execute the <command> and any arguments entered on the command line. You can RUN multiple command lines by separating them with plus signs (+). If you press Return after a plus sign, RUN interprets the next line as a continuation of the same command line.
To make it possible to close the Shell window in which the process was started, redirect the output of RUN with RUN >NIL: <command>.
A new background Shell has the same search path and command stack size as the Shell from which RUN is given.
You can RUN commands stored to the resident list. Resident commands are checked before commands in the command path. A Shell started with RUN NEWSHELL uses the default startup file, S:Shell-startup.
- Example 1
1> RUN COPY Text TO PRT:+ DELETE Text + ECHO "Printing finished"
prints the Text file by copying it to the printer device, deletes it, then displays the given message. Plus signs string together the command lines, causing each command to be run after the previous command finishes.
- Example 2
1> RUN EXECUTE Comseq
executes, in the background, all the commands in the script file Comseq.
For more examples using the RUN command, see Chapter 8.
RX
Launches an ARexx program.
- Format
- RX <name> [<arguments>]
- Template
- NAME,ARG/F
- Location
- C:
RX launches an ARexx program. If the specified name includes an explicit path, only that directory is searched for the program; otherwise, the current directory and REXX: are checked for a program with the given name. The optional argument string is passed to the program.
In place of the name of an ARexx program to be launched you can also write a short list of ARexx statements which will be executed as a single line command. To do so, enclose the statements in double quotes.
The RX program will try to start the ARexx resident process before it will attempt to launch a program.
You can also use the RX program from Workbench. Make it the default tool of an ARexx program, then double-click on the icon. The following tool types are supported:
| CONSOLE | Overrides the default output console window specification, "CON://640/100/WAIT/RX Output". |
| CMD | Use the command given in the tool type text rather than attempt to execute the ARexx program the icon is attached to. |
| STARTUP | If present, try to run a different program before the ARexx program is launched. If this is omitted, "RexxMast" will be launched. |
- Example 1
Launch the ARexx command "script.rexx" with argument "Names.txt".
1> RX script.rexx Names.txt
- Example 2
Launch the ARexx command "script.rexx". Note that the command name suffix is omitted and defaults to ".rexx"
1> RX script
- Example 3
Evaluate an ARexx expression.
1> RX "say 17 / 23"
RXC
Closes the ARexx resident process.
- Format
- RXC
- Template
- (none)
- Location
- C:
RXC closes the ARexx resident process. The "REXX" public port is withdrawn immediately and the resident process exits as soon as the last ARexx program finishes. No new programs can be launched after a close request.
RXLIB
Manages and lists ARexx function libraries and hosts.
- Format
- RXLIB <name> [<priority> [<offset> [<version>]]]
- Template
- NAME,PRIORITY,OFFSET/N,VERSION/N
- Location
- C:
RXLIB manages function libraries and hosts, so that they can be called from ARexx, and it can also be used to list which libraries are currently defined.
To add a new library, specify its name, priority and offset value. The priority must be in the range -100.100. For your library to be invoked before the resident process has a look at a command, make sure that the priority is greater than -60. The offset value is the actual library vector offset and should be documented with each library. The last parameter, the required library version, can usually be omitted in which case 0 will be used (any library version is acceptable).
| Note |
|---|
| Do not get the library offset value wrong or ARexx will crash when the next attempt is made to call a function library! |
To add a new host, specify its name and priority, but omit the offset value and version number. Note that at the time the host is added no test is performed to verify that a public message port of that name exists.
| Note |
|---|
| You cannot directly replace an existing function library or host with a new entry. The old entry needs to be removed before the new entry can be added. |
To remove a library or host, specify its name and omit the priority, offset, and version parameters.
To list all function libraries and hosts, omit the library name, priority, offset, and version parameters.
- Example 1
Add "rexxsupport.library":
1> RXLIB rexxsupport.library 0 -30
- Example 2
Show all active libraries and hosts:
1> RXLIB rexxsupport.library (library) REXX (host)
- Example 3
Remove "rexxsupport.library":
1> RXLIB rexxsupport.library
- Example 4
Add a new host by the name of "MORE":
1> RXLIB MORE -1
RXSET
Manage or list the Clip List.
- Format
- RXSET [<name> [[=] <value>]]
- Template
- NAME,VALUE/F
- Location
- C:
RXSET adds a name-value pair to the Clip List. Name strings are assumed to be in mixed case. If a pair with the same name already exists, its value is replaced with the current string. If a name without a value string is given, the entry is removed from the Clip List. If RXSET is invoked without arguments, it will list all name-value pairs in the Clip List.
| Note |
|---|
| The original RXSET command would preserve the exact number of blank spaces in the 'value' string. This is not the case with this new version of the command, which will always put exactly one blank space between the words in the 'value' string. If you need an exact number of blank spaces, you should put them into double quotes. |
- Example 1
Add the name-value pair "answer=42" to the Clip List (more than one syntax is supported; all three examples are equivalent):
1> RXSET answer=42 1> RXSET answer = 42 1> RXSET answer 42
- Example 2
Show the current Clip List contents:
1> RXSET answer=42
SAMPLENETSPEED
?
- Format
- ?
- Template
- ?
- Location
- C:
Missing description.
SEARCH
Looks for the specified text string in the files of the specified directories.
- Format
- SEARCH [FROM] <name|pattern> [SEARCH|NAME] <string|pattern>
- [ALL] [NONUM] [QUIET] [QUICK] [FILE] [PATTERN] [CASE]
- Template
- FROM/M,SEARCH/A,ALL/S,NONUM/S,QUIET/S,QUICK/S,FILE/S,PATTERN/S,CASE/S
- Location
- C:
SEARCH looks through all the files in the FROM directory for the given SEARCH string. (The FROM and SEARCH keywords are optional.) If the ALL switch is given, SEARCH also looks through all the subdirectories of the FROM directory. SEARCH displays the name of the file being searched and any line that contains the text sought. You must place quotation marks around any search text containing a space. The search is case-indifferent (capitalization is ignored) unless the CASE switch was specified.
The options are as follows:
| NONUM | Line numbers are not printed with the strings. |
| QUIET | Searches quietly; filenames being searched are not displayed. The local shell variable _Verbosity with a negative value has the same effect. |
| QUICK | Uses a more compact output format. |
| FILE | Looks for a file by the specified name, rather than for a string in the file. |
| PATTERN | Uses pattern matching in the search. |
| CASE | Uses case sensitive string comparison in the search. |
SEARCH leaves a 0 in the condition flag if the object is found, and a 5 (WARN) otherwise. This makes it useful in scripts. To abandon the search of the current file and continue to the next file, if any, type Ctrl-D. SEARCH is aborted when a Ctrl-C is typed.
- Example 1
1> Search DEVS: alternative
Keymaps (dir)
Printers (dir)
clipboard.device..
MountList..
14 \* This is an example of an alternative type of non-filing device mount.
narrator.device..
parallel.device..
printer.device..
serial.device..
system-configuration..
searches through the DEVS: directory for the word alternative. It is found on line 14 of the MountList file.
- Example 2
1> SEARCH Universe: "Intelligent life" ALL
searches for Intelligent life (or intelligent life) in every file on the volume Universe:.
- Example 3
1> Work:#?.source SEARCH Progtest.c?? FILE PATTERN
locates all Progtest.c files with a two-character suffix in directories ending in .source in the Work volume.
SET
Sets a local vaiable.
- Format
- SET [<name>] [<string...>]
- Template
- NAME,STRING/F
- Location
- Internal
SET with no arguments lists the current local variables.
SET with <name> and <string> arguments creates a new environment variable. The first word after SET is taken as the <name>. Everything else on the command line is taken as the <string> argument. Quotation marks are not required.
An environment variable created with SET is local to the Shell in which it was created. If you create a new Shell with the NEWSHELL command, that Shell also recognizes any variables created in its parent Shell. However, if you create a new Shell with the Execute Command Workbench menu item or by opening the Shell icon, variables created with SET are not recognized in the new Shells.
You can call environment variables in a script or on a command line by placing a dollar sign ($) in front of the variable name.
To remove a local variable definition, use the UNSET command.
- Example
1> SET Origin This process launched from icon
creates the local variable Origin that sores a reminder that a Shell was invoked from an icon rather than a NEWSHELL.
1> ECHO $Origin This process launched from icon
- See also
SETCLOCK
Sets or reads the battery backed-up hardware clock.
- Format
- SETCLOCK LOAD | SAVE | RESET
- Template
- LOAD/S,SAVE/S,RESET/S
- Location
- C:
SETCLOCK SAVE sets the date and time of the battery backed-up hardware clock (if your system has one) from the current system time, which is set with the Time editor or with the DATE command. SETCLOCK SAVE is typically used after a DATE command.
SETCLOCK LOAD sets the current system time from the battery backed-up clock. This is done automatically during the boot process.
The RESET option resets the clock completely. Use this option if the clock is accidentally turned off or LOAD and SAVE do not appear to work correctly.
- Example
1> DATE 22-Jan-93 07:15:25 1> SETCLOCK SAVE
saves the date, January 22, 1993, and the time, 7:15 a.m., to the battery backed-up hardware clock. When the system is booted, the system clock is set with the time saved in the hardware clock.
Some Amiga models do not have battery backed-up clocks unless an expansion unit has been installed.
- See also
SETDATE
Change the timestamp of a file or directory.
- Format
- SETDATE <file|pattern> [<date>] [<time>] [ALL] [QUIET] [FILES] [DIRS]
- Template
- FILE/A,DATE,TIME,ALL/S,QUIET/S,FILES/S,DIRS/S
- Location
- C:
SETDATE changes the timestamp (date and time of creation or last change) of a file or directory. SETDATE <file> changes the date/time of the file to the current system date/time. SETDATE does not affect the software or hardware clocks.
The output of the DATE command may be used as input to SETDATE.
The options are:
| ALL | Change the dates of all subdirectories and their files. |
| QUIET | If the QUIET option is given, screen output is suppressed. The local shell variable _Verbosity with a negative value has the same effect. |
| FILES | Only change the dates of the files found. |
| DIRS | Only change the dates of the directories found. |
| Note |
|---|
| The FILES and DIRS options work together: if you use FILES and omit DIRS, then only the files will be affected and the other way round. If none of FILES and DIRS is used, all files and directories will have their dates changed. |
- Example 1
1> SETDATE TestFile
changes the date and time associated with TestFile to the current date and time.
- Example 2
1> SETDATE TestFile 16-09-89 15:25:52
change the date and time associated with TestFile to September 16, 1989, 3:25 p.m.
- See also
SETDOSDEBUG
?
- Format
- ?
- Template
- ?
- Location
- C:
Missing description.
SETENV
Sets a global variable.
- Format
- SETENV [<name>] [<string...>]
- Template
- NAME,STRING/F
- Location
- Internal
SETENV with no arguments lists the current global variables.
SETENV with <name> and <string> arguments creates a new global environment variable. The first word after SETENV is taken as the <name>. Everything else on the command line is taken as the <string> argument. Quotation marks are not required.
Global variables are stored in the ENV: directory and are available to all processes. However, if a local variable (defined by SET) and a global variable share the same name, the local variable is used.
Environment variables are called by scripts or other commands by including a dollar sign ($) in front of the variable name.
To remove a global variable definition, use the UNSETENV command.
- Example 1
1> SETENV Editor Extras:Tools/MEmacs
creates the environment variable Editor That can be used with the MORE utility. This specifies the editor as MEmacs, located in the Tools drawer of EXTRAS:. The variable Editor is available in any Shell.
- Example 2
1> SETENV Editor C:ED
same as above, only the editor specified is ED.
1> ECHO $Editor C:ED
- See also
SETFONT
Changes the font of the current Shell.
- Format
- SETFONT <size> [SCALE] [PROP] [ITALIC] [BOLD] [UNDERLINE] [CHARSET]
- Template
- NAME/A,SIZE/A,SCALE/S,PROP/S,ITALIC/S,BOLD/S,UNDERLINE/S,CHARSET/K
- Location
- C:
SETFONT lets you change the font used in a particular Shell window, overriding the System Default Font setting specified in the Font preferences editor. SETFONT is only effective in the window in which it is invoked.
You must specify both a font name and a size when using the SETFONT command.
Invoking SETFONT will clear the Shell window of its current contents and display a new prompt, in the new font, at the top of the window.
The other options are:
| SCALE | Enables bitmap font scaling. |
| PROP | Allows proportional fonts. |
| ITALIC | The font will be italic. |
| BOLD | The font will be boldface. |
| UNDERLINE | The font will be underlined. |
| CHARSET | The font will be in the specified charset, not in the current default charset. |
- Example
1> SETFONT Fixed 13 BOLD UNDERLINE CHARSET ISO-8859-7
The Shell window will clear, and the new prompt will be in 13 pixels Fixed.font, underlined and boldface, with greek glyphs for the characters above 0xA0.
SETFONTCHARSET
Adds charset tag and version string to a FontContentsHeader file.
- Format
- SETFONTCHARSET <sourcefontfile> <charset> [VERSTRING]
- Template
- BITMAPFONTFILENAME/A,CHARSET/A,VERSTRING/K
- Location
- C:
SETKEYBOARD
Changes the keymap used by the current Amiga console.
- Format
- SETKEYBOARD <keymap> [CHARSET]
- Template
- KEYMAP/A,CHARSET/K
- Location
- C:
SETKEYBOARD specifies the keymap used by the Amiga for the current console. The keymap file must be present in KEYMAPS: for SETKEYBOARD to find it.
The other options are:
| CHARSET | The keymap will be adjusted to the specified charset, not to the current default charset. You should only use this option when you also selected a different font charset with the SETFONT command. The adjustment does e.g. include the deadkey combinations which otherwise would produce confusing results. |
- Example 1
To change to a French Canadian keymap, enter:
1> SETKEYBOARD cdn_f
- Example 2
To switch the current console to ISO-8859-15 charset and german keymap, type:
1> SETFONT topaz 8 CHARSET ISO-8859-15 1> SETKEYBOARD d_ISO-8859-15 CHARSET ISO-8859-15
SHOW68LOADS
?
- Format
- ?
- Template
- ?
- Location
- C:
Missing description.
SHOWAPPLIST
?
- Format
- ?
- Template
- ?
- Location
- C:
Missing description.
SHOWNETSTATUS
Displays various information about the status of the network configuration.
- Format
- SHOWNETSTATUS [INTERFACE=<itf>[,<itf>...]] [INTERFACES] [ARPCACHE=ARP]
- [ROUTES] [DNS=DOMAINNAMESERVERS] [ICMP] [IGMP] [IP] [MB=MEMORY] [MR=MULTICASTROUTING]
- [RT=ROUTING] [TCP] [UDP] [TCPSOCKETS] [UDPSOCKETS] [NAMES] [ALL] [REPEAT] [QUIET]
- Template
- INTERFACE/M,INTERFACES/S,ARPCACHE=ARP/S,ROUTES/S,DNS=DOMAINNAMESERVERS/S,ICMP/S,IGMP/S,IP/S,MB=MEMORY/S,MR=MULTICASTROUTING/S,RT=ROUTING/S,TCP/S,UDP/S,TCPSOCKETS/S,UDPSOCKETS/S,NAMES/S,ALL/S,REPEAT/S,QUIET/S
- Location
- C:
Missing description.
SKIP
Skips to a label when executing script files.
- Format
- SKIP [<label>] [BACK]
- Template
- LABEL,BACK/S
- Location
- Internal
SKIP is used in scripts to allow you to skip ahead in the script to a <label> defined by a LAB statement. If no <label> is specified, SKIP jumps to the next LAB statement.
SKIP always searches forward from the current line of the file. However, when the BACK option is used, SKIP starts searching for the label from the beginning of the file. This allows SKIPs to points prior to the SKIP command.
You can only SKIP as far back as the last EXECUTE statement. If there are no EXECUTE statements in a script, you SKIP back to the beginning of the file.
If SKIP does not find the label specified, the command sequence terminates and the message Label <label> not found by Skip is displayed.
- Example
Assume you have the following script, called CheckFile:
.KEY name
IF exists <name>
SKIP message
ELSE
ECHO "<name> is not in this directory."
QUIT
ENDIF
LAB message
ECHO "The <name> file exists."
You can run the script by entering:
1> EXECUTE CheckFile Document
If the Document file exists in the current directory, the execution of the script SKIPs ahead to the LAB command. The message:
The Document file exists.
Is displayed in the Shell window.
If the Document file is not in the current directory, the execution of the script jumps to the line after the ELSE statement, displaying the message:
Document is not in this directory.
- See also
SMARTCTL
Control and monitor SMART disks.
- Format
- SMARTCTL [<options>] <device>
- Template
- -h,-V,-i,--identify,-g,-a,-x,--scan,--scan-open,
- -q,-d,-T,-b,-r,-n,
- -s,-o,-S,
- -H,-c,-A,-f,-l,-v,-F,-P,-B,
- -t,-C,-X,
- DEVICE
- Location
- C:
Missing description.
SORT
Alphabetically sorts the lines of a file.
- Format
- SORT [FROM] <file | pattern> [TO] <filename> [COLSTART <n>] [CASE] [NUMERIC]
- Template
- FROM/A,TO/A,COLSTART/K,CASE/S,NUMERIC/S
- Location
- C:
SORT sorts the FROM file alphabetically, line-by-line, sending the sorted results to the TO file. SORT assumes the file is a normal text file in which lines are separated by line feeds. SORT normally disregards case. If the CASE switch is given, upper-cased items are output first.
The COLSTART keyword specifies the character column at which the comparison begins. SORT starts comparing the lines from that point, wrapping around to the beginning of the line if the compared lines match to the end.
When the NUMERIC option is specified, the lines are interpreted as numbers from the first column reading to the right, stopping at the first non-numeric character. Lines not beginning with numbers are treated as 0. The lines are output in numerical order. CASE is ignored when NUMERIC is specified.
- Example
1> SORT DF0:Glossary TO DF0:Glossary.alpha
sorts the lines in the Glossary file, arranges them alphabetically, and outputs them to a next file called Glossary.alpha. The case of the words is disregarded.
For more examples using the SORT command, see Chapter 8.
SOUNDPLAYER
Plays a sound sample.
- Format
- SOUNDPLAYER [VERBOSE] [QUIET] [R | RATE | SAMPLERATE <sample rate>] [<sample file>] [VOL | VOLUME <volume>]
- Template
- V=VERBOSE/S,Q=QUIET/S,SR=RATE=SAMPLERATE/K/N,FROM/M,VOL=VOLUME/K/N
- Location
- C:
Missing description.
STACK
Displays or sets the stack size within the current Shell.
- Format
- STACK [[SIZE] <stack size>]
- Template
- SIZE/N
- Location
- Internal
A Shell uses a certain amount of stack, a special area in memory allocated for it. Each Shell has a specific stack size. If a program causes a system failure, changing the Shell's stack size may solve the problem. Commands performing operations consisting of multiple levels can require additional stack space.
Stack sizes typically range from 4096 to 40000 bytes. If the stack size is too small, a system failure can occur. If the stack size is too large, it can use too much memory.
| Note |
|---|
| A software failure message is displayed if you run out of stack space. Increase the stack space for the Shell that caused the error. |
Entering the STACK command with no arguments displays the current stack size.
STATUS
Lists information about Shell processes.
- Format
- STATUS [<process>] [FULL] [TCB] [CLI | ALL] [COM | COMMAND <command>]
- Template
- PROCESS/N,FULL/S,TCB/S,CLI=ALL/S,COM=COMMAND/K
- Location
- C:
STATUS without any arguments lists the numbers of the current Shell processes and the program or command running in each. The <process> argument specifies a process number, limiting STATUS to giving information about that process only.
For information on the stack size, global vector size, priority, and the current command for each process, use the FULL keyword. The TCB keyword is similar, omitting the command information. The CLI=ALL keyword gives only the command information.
STATUS searches for a command when you use the COMMAND option. STATUS scans the Shell list, looking for the specified <command>. If the command is found, the Shell's process number is output, and the condition flag is set to 0. Otherwise, the flag is set to 5 (WARN).
- Example 1
1> STATUS 1 Process 1: Loaded as command: status
- Example 2
1> STATUS 1 FULL Process 1: stk 4000, gv 150, pri 0 Loaded as command: status
- Example 3
1> STATUS >RAM:Xyz COMMAND=COPY 1> BREAK <RAM:Xyz >NIL: ?
sends a break to the process executing COPY.
SWAPCD
Interchanges the current directory and a stacked directory.
- Format
- SWAPCD [<dir | pattern>] [LEVEL <number>]
- Template
- DIR,LEVEL/N
- Location
- Internal
Missing description.
TCC
Closes the ARexx tracing console window.
- Format
- TCC
- Template
- (none)
- Location
- C:
TCC closes the global ARexx tracing console as soon as all active programs are no longer using it. All read requests queued to the console must be satisfied before it can be closed.
TCO
Opens the ARexx tracing console window.
- Format
- TCO
- Template
- (none)
- Location
- C:
TCO opens the global ARexx tracing console. The tracing output from all active ARexx programs is diverted automatically to the new console. The console window can be moved and resized by the user and can be closed with the TCC command.
- Example
1> TCO
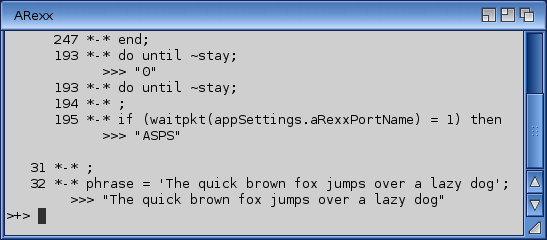
TCPDUMP
Dumps traffic on a network.
- Format
- TCPDUMP [-aAdDeflLnNOpqRStuUvxX] [-c <count>] [-C <file_size>] [-E <algo:secret>] [-F <file>] [-i <interface>] [-r <file>] [-s <snaplen>] [-T <type>] [-w <file>] [-y <datalinktype>] [<expression>]
- Template
- -a,-A,-d,-D,-e,-f,-l,-L,-n,-N,-O,-p,-q,-R,-S,-t,-u,-U,-v,-x,-X,-c,-C,-E,-F,-i,-r,-s,-T,-w,-y
- Location
- C:
Missing description.
TE
Clears the ARexx global tracing flag.
- Format
- TE
- Template
- (none)
- Location
- C:
TE clears the global ARexx tracing flag, which forces the tracing mode to OFF for all active ARexx programs.
TEE
Sends data from the standard input to the standard output and prints it to the console.
- Format
- TEE [SIZE=<number>] [LINE]
- Template
- SIZE/N/K,LINE/S
- Location
- Internal
The TEE command will read data from its standard input and send it to its standard output, but additionally it will also send a copy of the data to the console. This allows for pipe commands to be monitored.
By default the TEE command reads data in chunks of 512 bytes each, which can be changed with the SIZE parameter; it controls how many bytes will be read apiece. Alternatively, you can tell the TEE command to read the input line by line. The LINE parameter activates this mode of operation.
- See also
TRACEROUTE
Prints the route packets take to network host.
- Format
- TRACEROUTE [-d | DEBUG] [-m | MAXTTL <ttl>] [-n | NUMERIC] [-p | PORT <number>]
- [-q | QUERIES <number>] [-r | DONTROUTE] [-s | SOURCE <address>]
- [-t | TOS <type>] [-v | VERBOSE] [-w | WAIT
- [PACKETSIZE <size>]
- Template
- -d=DEBUG/S,-m=MAXTTL/K/N,-n=NUMERIC/S,-p=PORT/K/N,-q=QUERIES/K/N,-r=DONTROUTE/S,-s=SOURCE/K,-t=TOS/K/N,-v=VERBOSE/S,-w=WAIT/K/N,HOST/A,PACKETSIZE/N
- Location
- C:
The Internet is a large and complex aggregation of network hardware, connected together by gateways. Tracking the route one's packets follow (or finding the miscreant gateway that's discarding your packets) can be difficult. TRACEROUTE utilizes the IP protocol `time to live' field and attempts to elicit an ICMP TIME_EXCEEDED response from each gateway along the path to some host.
The only mandatory parameter is the destination host name or IP number. The default probe datagram length is 38 bytes, but this may be increased by specifying a packet size (in bytes) after the destination host name.
TRACEROUTE options are:
| -m, MAXTTL | Set the max time-to-live (max number of hops) used in outgoing probe packets. The default is 30 hops (the same default used for TCP connections). |
| -n, NUMERIC | Print hop addresses numerically rather than symbolically and numerically (saves a nameserver address-to-name lookup for each gateway found on the path). |
| -p, PORT | Set the base UDP port number used in probes (default is 33434). TRACEROUTE hopes that nothing is listening on UDP ports base to base+nhops-1 at the destination host (so an ICMP PORT_UNREACHABLE message will be returned to terminate the route tracing). If something is listening on a port in the default range, this option can be used to pick an unused port range. |
| -q, QUERIES | Set the number of probes per ``ttl (default is three probes). |
| -r, DONTROUTE | Bypass the normal routing tables and send directly to a host on an attached network. If the host is not on a directly-attached network, an error is returned. This option can be used to ping a local host through an interface that has no route through it. |
| -s, SOURCE | Use the following IP address (which must be given as an IP number, not a hostname) as the source address in outgoing probe packets. On hosts with more than one IP address, this option can be used to force the source address to be something other than the IP address of the interface the probe packet is sent on. If the IP address is not one of this machine's interface addresses, an error is returned and nothing is sent. |
| -t, TOS | Set the type-of-service in probe packets to the following value (default zero). The value must be a decimal integer in the range 0 to 255. This option can be used to see if different types-of-service result in different paths. Not all values of TOS are legal or meaningful - see the IP spec for definitions. Useful values are probably `-t 16' (low delay) and `-t 8' (high throughput). |
| -v, VERBOSE | Verbose output. Received ICMP packets other than TIME_EXCEEDED and UNREACHABLEs are listed. |
| -w, WAIT | Set the time (in seconds) to wait for a response to a probe (default 3 sec.). |
TRACEROUTE attempts to trace the route an IP packet would follow to some internet host by launching UDP probe packets with a small ttl (time to live) then listening for an ICMP "time exceeded" reply from a gateway. We start our probes with a ttl of one and increase by one until we get an ICMP "port unreachable" (which means we got to "host") or hit a max (which defaults to 30 hops & can be changed with the -m flag). Three probes (changed with -q flag) are sent at each ttl setting and a line is printed showing the ttl, address of the gateway and round trip time of each probe. If the probe answers come from different gateways, the address of each responding system will be printed. If there is no response within a 3 sec. timeout interval (changed with the -w flag), a "*" is printed for that probe.
We don't want the destination host to process the UDP probe packets so the destination port is set to an unlikely value (if some clod on the destination is using that value, it can be changed with the -p flag).
A sample use and output might be:
1> TRACEROUTE nis.nsf.net. traceroute to nis.nsf.net (35.1.1.48), 30 hops max, 56 byte packet 1 helios.ee.lbl.gov (128.3.112.1) 19 ms 19 ms 0 ms 2 lilac-dmc.Berkeley.EDU (128.32.216.1) 39 ms 39 ms 19 ms 3 lilac-dmc.Berkeley.EDU (128.32.216.1) 39 ms 39 ms 19 ms 4 ccngw-ner-cc.Berkeley.EDU (128.32.136.23) 39 ms 40 ms 39 ms 5 ccn-nerif22.Berkeley.EDU (128.32.168.22) 39 ms 39 ms 39 ms 6 128.32.197.4 (128.32.197.4) 40 ms 59 ms 59 ms 7 131.119.2.5 (131.119.2.5) 59 ms 59 ms 59 ms 8 129.140.70.13 (129.140.70.13) 99 ms 99 ms 80 ms 9 129.140.71.6 (129.140.71.6) 139 ms 239 ms 319 ms 10 129.140.81.7 (129.140.81.7) 220 ms 199 ms 199 ms 11 nic.merit.edu (35.1.1.48) 239 ms 239 ms 239 ms
Note that lines 2 & 3 are the same. This is due to a buggy kernel on the 2nd hop system - lbl-csam.arpa - that forwards packets with a zero ttl (a bug in the distributed version of 4.3 BSD). Note that you have to guess what path the packets are taking cross-country since the NSFNet (129.140) doesn't supply address-to-name translations for its NSSes.
A more interesting example is:
1> TRACEROUTE allspice.lcs.mit.edu. traceroute to allspice.lcs.mit.edu (18.26.0.115), 30 hops max 1 helios.ee.lbl.gov (128.3.112.1) 0 ms 0 ms 0 ms 2 lilac-dmc.Berkeley.EDU (128.32.216.1) 19 ms 19 ms 19 ms 3 lilac-dmc.Berkeley.EDU (128.32.216.1) 39 ms 19 ms 19 ms 4 ccngw-ner-cc.Berkeley.EDU (128.32.136.23) 19 ms 39 ms 39 ms 5 ccn-nerif22.Berkeley.EDU (128.32.168.22) 20 ms 39 ms 39 ms 6 128.32.197.4 (128.32.197.4) 59 ms 119 ms 39 ms 7 131.119.2.5 (131.119.2.5) 59 ms 59 ms 39 ms 8 129.140.70.13 (129.140.70.13) 80 ms 79 ms 99 ms 9 129.140.71.6 (129.140.71.6) 139 ms 139 ms 159 ms 10 129.140.81.7 (129.140.81.7) 199 ms 180 ms 300 ms 11 129.140.72.17 (129.140.72.17) 300 ms 239 ms 239 ms 12 * * * 13 128.121.54.72 (128.121.54.72) 259 ms 499 ms 279 ms 14 * * * 15 * * * 16 * * * 17 * * * 18 ALLSPICE.LCS.MIT.EDU (18.26.0.115) 339 ms 279 ms 279 ms
Note that the gateways 12, 14, 15, 16 & 17 hops away either don't send ICMP "time exceeded" messages or send them with a ttl too small to reach us. 14 - 17 are running the MIT C Gateway code that doesn't send "time exceeded"s. God only knows what's going on with 12.
The silent gateway 12 in the above may be the result of a bug in the 4.[23] BSD network code (and its derivatives): 4.x (x <= 3) sends an unreachable message using whatever ttl remains in the original datagram. Since, for gateways, the remaining ttl is zero, the ICMP "time exceeded" is guaranteed to not make it back to us. The behavior of this bug is slightly more interesting when it appears on the destination system:
1 helios.ee.lbl.gov (128.3.112.1) 0 ms 0 ms 0 ms 2 lilac-dmc.Berkeley.EDU (128.32.216.1) 39 ms 19 ms 39 ms 3 lilac-dmc.Berkeley.EDU (128.32.216.1) 19 ms 39 ms 19 ms 4 ccngw-ner-cc.Berkeley.EDU (128.32.136.23) 39 ms 40 ms 19 ms 5 ccn-nerif35.Berkeley.EDU (128.32.168.35) 39 ms 39 ms 39 ms 6 csgw.Berkeley.EDU (128.32.133.254) 39 ms 59 ms 39 ms 7 * * * 8 * * * 9 * * * 10 * * * 11 * * * 12 * * * 13 rip.Berkeley.EDU (128.32.131.22) 59 ms ! 39 ms ! 39 ms !
Notice that there are 12 "gateways" (13 is the final destination) and exactly the last half of them are "missing". What's really happening is that rip (a Sun-3 running Sun OS3.5) is using the ttl from our arriving datagram as the ttl in its ICMP reply. So, the reply will time out on the return path (with no notice sent to anyone since ICMP's aren't sent for ICMP's) until we probe with a ttl that's at least twice the path length. I.e., rip is really only 7 hops away. A reply that returns with a ttl of 1 is a clue this problem exists. TRACEROUTE prints a "!" after the time if the ttl is <= 1. Since vendors ship a lot of obsolete (DEC's Ultrix, Sun 3.x) or non-standard (HPUX) software, expect to see this problem frequently and/or take care picking the target host of your probes. Other possible annotations after the time are !H, !N, !P (got a host, network or protocol unreachable, respectively), !S or !F (source route failed or fragmentation needed - neither of these should ever occur and the associated gateway is busted if you see one). If almost all the probes result in some kind of unreachable, TRACEROUTE will give up and exit.
This program is intended for use in network testing, measurement and management. It should be used primarily for manual fault isolation. Because of the load it could impose on the network, it is unwise to use TRACEROUTE during normal operations or from automated scripts.
TS
Starts ARexx's interactive tracing.
- Format
- TS
- Template
- (none)
- Location
- C:
TS starts interactive ARexx tracing by setting the external trace flag, which forces all active ARexx programs into interactive tracing mode. Programs will start producing trace output and will pause after the next statement.
This command is useful for regaining control over programs caught in infinite loops or otherwise misbehaving. The trace flag remains set until cleared by the TE command, so subsequent program invocations will be executed in interactive tracing mode.
TYPE
Displays a text file.
- Format
- TYPE {<file|pattern>} [TO <name>] [OPT H|N] [HEX] [NUMBER]
- [AUTO] [TEXTONLY] [WIDTH <line width>] [BUF|BUFFER=<n>]
- Template
- FROM/A/M,TO/K,OPT/K,HEX/S,NUMBER/S,AUTO/S,TEXTONLY/S,WIDTH/K/N,BUF=BUFFER/K/N,MULTI/S
- Location
- C:
TYPE will output the contents of the named file to the current window, if no destination is given, or to a specified output file. If more than one filename is specified, and the TO keyword is not used, the filenames will be typed in sequence.
The OPT H and OPT N options are also available by the HEX and NUMBER keywords, respectively. The HEX option causes the file to be typed as columns of hexadecimal numbers, with an ASCII character interpretation column. This is useful for analyzing object files. The NUMBER option will number the lines as they are output.
The AUTO option will make TYPE examine the first 256 characters of the file. If non-printable characters are found, TYPE will show the file as if the HEX option had been specified. Note that you can override the AUTO option with the HEX option, in which case you will always see the file(s) typed as columns of hexadecimal numbers.
The WIDTH option controls how long each line in HEX mode form should become. For example, WIDTH=120 will try to print as much data in hexadecimal form as will fit into a line of up to 120 characters in total. The default is to print up to 61 characters per line.
By default, TYPE will print the contents of the file as is read, including binary data (unprintable characters). To replace unprintable characters before output, use the TEXTONLY option. Any unprintable character will be replaced with '.'.
How much data is read and output at a time can be controlled with the BUFFER option. By default, a maximum of 2048 bytes will be read/written at a time.
To pause output, press the Space bar. To resume output, press Backspace, Return, or Ctrl-X. To stop output, press Ctrl-C (***BREAK is displayed).
The MULTI option was added in 54.1 and when specified, TYPE will also search multi-assignment paths for the file.
- Example
1> TYPE S:User-Startup
The contents of the User-Startup file in the S: directory will be displayed on the screen.
UNALIAS
Removes an alias.
- Format
- UNALIAS [<name>]
- Template
- NAME
- Location
- Internal
UNALIAS removes the named alias from the alias list. With no arguments, UNALIAS lists the current aliases.
- See also
UNSET
Removes a local variable.
- Format
- UNSET [<name>]
- Template
- NAME
- Location
- Internal
UNSET removes the named local variable from the variable list for the current process. With no arguments, UNSET lists the current variables.
- See also
UNSETENV
Removes a global variable.
- Format
- UNSETENV [<name>]
- Template
- NAME
- Location
- Internal
UNSETENV removes the named global variable from the current variable list. With no arguments, UNSETENV lists the current variables.
- See also
UPTIME
Tells how long the system has been running.
- Format
- UPTIME
- Template
- (none)
- Location
- C:
UPTIME will find out how much time has passed since the Amiga was started and print that information. This will be given as the system start time followed by the total amount of time that has passed since (in days and seconds).
- Example
1> UPTIME System has been up since 02-Sep-03 09:42:05 (total uptime 00:14:08)
URLOPEN
Opens a hypertext link.
- Format
- URLOPEN [PROTOCOL <protocol>] <link>
- Template
- PROTOCOL/K,LINK/F
- Location
- C:
URLOPEN opens a hypertext link using a viewer program configured in the URL Preferences editor. URLOPEN can be used in script files, applications' Tools menus, and as a project icon's default tool, among other things.
The link to be opened is given with the LINK parameter. URLOPEN identifies the link type (protocol) from the link's beginning automatically and summons the corresponding viewer. The protocol to be used can be supplied with the PROTOCOL parameter, too. The valid protocols are: FILE, HTTP, HTTPS, MAILTO, and WWW. FILE opens a local file, HTTP, HTTPS, and WWW a web page, and MAILTO an e-mail.
When URLOPEN is used as the icon's default tool, two tool types are available: PROTOCOL and FULLPATH. PROTOCOL tells the protocol to be used in viewing and FULLPATH controls the path resolution method. The default protocol is FILE and the other protocol options are the same as described earlier: HTTP, HTTPS, MAILTO, and WWW.
To use a device-centric path resolution, assign keyword DEVICENAME to the FULLPATH tool type. Assigning keyword VOLUMENAME instructs URLOPEN to use a volume-centric path resolution.
- Example 1
1> URLOPEN "http://www.hyperion-entertainment.biz"
opens the Hyperion Entertainment's web site with the configured viewer.
- Example 2
1> URLOPEN "Work:html_docs/data2.html"
opens the local file "data2.html" from the "Work:html_docs" directory with the configured viewer.
- Example 3
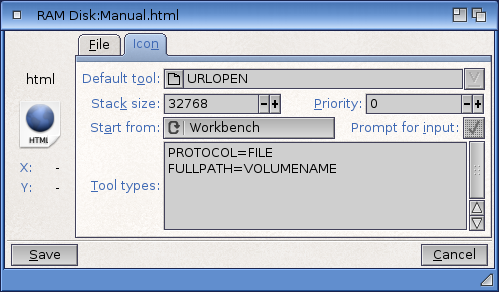
When the file Manual.html is double-clicked in Workbench, it will be opened with the FILE protocol viewer using a volume-centric path resolution.
USBCTRL
Controls the USB stack.
- Format
- USBCTRL [PREBOOT] [START] [RESTART] [STOP] [FLUSHLOG] [FORCE]
- Template
- PREBOOT/S,START/S,RESTART/S,STOP/S,FLUSHLOG/S,FORCE/S
- Location
- C:
USBCTRL allows you to start, restart, and stop the USB stack. It can also be used for flushing the USB log file.
USBCTRL START starts the USB stack. This is how the stack is started in the S:Startup-Sequence. USBCTRL PREBOOT starts the stack so that it will stay in PreBoot mode. The PreBoot mode is an initial operating mode which is active before the Startup-Sequence's USBCTRL START command is initiated.
USBSTRL RESTART restarts the USB stack. It is usually used for restarting the stack after installing a new USB device driver.
USBCTRL STOP tells the USB stack to terminate. If any client program has an open session with the stack, the stack will ask the program to close the session by sending a CTRL-F signal to the program. If the client program ignores the signal, the USB stack cannot terminate and it will remain active.
When a FORCE switch is used with the USBCTRL STOP, the USB stack terminates despite the active client sessions.
The USB stack has a log which can be viewed with the LogViewer utility. The log can be flushed with USBCTRL FLUSHLOG command.
- Example 1
1> USBCTRL RESTART
restarts the USB stack.
- Example 2
1> USBCTRL FLUSHLOG
flushes the USB stack's log.
VERSION
Finds software version and revision numbers.
- Format
- VERSION [<library | device | file>] [<version #>] [<revision #>]
- [FILE] [FULL] [<unit #>] [INTERNAL] [RES] [VSTRING]
- Template
- NAME,VERSION/N,REVISION/N,FILE/S,FULL/S,UNIT/N,INTERNAL/S,RES/S,VSTRING/S
- Location
- C:
VERSION finds the version and revision number of a library, device, command, or Workbench disk. VERSION can also test for a specific version/revision and set the condition flags if the version/revision is greater. This is useful in scripts.
VERSION with no <library | device | file> argument prints the Kickstart version number and the Workbench version number and sets the environment variables. If a name is specified, version attempts to open the library, device, drive, or file and read the version information.
When a <version #> (and possibly a <revision #>) is specified, VERSION sets the condition flag to 0 if the version (and revision) number of the Kickstart, library, or device driver is greater than or equal to the specified values. Otherwise, the flag is set to 5 (WARN). (If a revision number is not specified, no comparison on the revision number is performed.)
The <unit #> option allows you to specify a unit number other than 0. This may be necessary for accessing multi-unit devices.
The NAME may be a wildcard pattern, in which case VERSION will examine all files matching the pattern. If a version number is given, scanning will stop as soon as a file is found whose version number is smaller than the one specified.
By default, only the name and the version number are printed. Further information might be available, such as the last modification time. To print it as well, use the FULL option.
The FILE option makes the VERSION command ignore libraries and commands already loaded and specifically checks the named file instead (this is also the case if you use wildcard patterns with the NAME parameter).
The VSTRING keyword requires a NAME parameter that is not a wildcard pattern. If version information can be found for the named object, it will be printed in the standard format; if no such information is available, an empty line will be printed instead. This feature is useful for script files.
The INTERNAL and RES options are obsolete and are retained solely for the purpose of backwards compatibility with existing script files. Their original purpose was to restrict the search for commands to the internal shell command list or the list of currently resident commands.
- Example 1
1> VERSION Kickstart 53.70 Workbench 53.16
- Example 2
1> VERSION SYS:Prefs/Font Font 53.6
- Example 3
1> VERSION C:Version VSTRING $VER: Version 53.10 (7.12.2016)
WAIT
Waits for the specified time.
- Format
- WAIT [<n>] [SEC | SECS |MIN | MINS] [UNTIL
- Template
- /N,SEC=SECS/S,MIN=MINS/S,UNTIL/K
- Location
- C:
WAIT is used in command sequences or after RUN to wait for a certain period of time or until a specific time. The default waiting period is one second.
The <n> argument specifies the number of seconds or minutes to wait. These options are mutually exclusive; you can only enter seconds or minutes.
Use the keyword UNTIL to wait until a particular time of the day, given in the format HH:MM.
- Example 1
1> WAIT 10 MINS
waits ten minutes.
- Example 2
1> WAIT UNTIL 21:15
waits until 9:15 p.m.
WAITFORPORT
Wait for a public message port to appear.
- Format
- WAITFORPORT <name> [[TIMEOUT] <seconds>]
- Template
- NAME/A,TIMEOUT/N
- Location
- C:
WAITFORPORT waits 10 seconds for the specified message port to appear. A return code of 0 indicates that the port was found. A return code of 5 indicates that the application is not currently running or that the port does not exist.
| Note |
|---|
| Port names are case sensitive. |
You can choose how long WAITFORPORT will wait by using the TIMEOUT parameter.
To stop WAITFORPORT waiting, use the BREAK command or press Ctrl-C while the shell window is active that belongs to the WAITFORPORT command.
- Example 1
Wait for the message port "ED_1" to appear; wait for up to 10 seconds:
1> WAITFORPORT ED_1
- Example 2
Wait for 5 seconds for the message port "MyPort" to appear:
1> WAITFORPORT MyPort TIMEOUT 5
WBINFO
Opens Workbench information windows from a shell.
- Format
- WBINFO [<object> [<object>]...] [PUBSCREEN <public screen name>]
- Template
- FILE=DRAWER=OBJECT/M/A,PUBSCREEN/K
- Location
- C:
WBINFO opens Workbench information windows from a shell. For each given object (file, drawer, or disk) it will create a separate process which in turn requests Workbench to bring up the Icon information requester. Please note that WBINFO has to wait for the last requester to be satisfied before it can end.
The PUBSCREEN parameter allows to open the Icon information requesters on a named public screen.
- Example
1> WBINFO SYS:Utilities/Clock
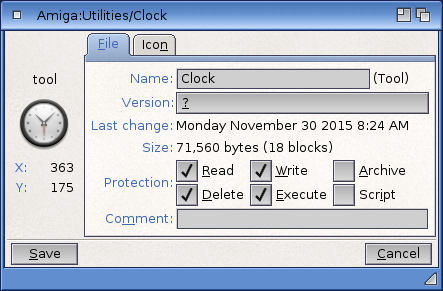
WBRUN
Runs programs from Shell as if they were executed from the Workbench.
- Format
- WBRUN <program> [<arg1> [| <arg2>...]] [SHOW=ICONS | ALL]
- [VIEWBY=ICON | NAME | DATE | SIZE | TYPE] [DELAY=<seconds>] [NOREQ]
- Template
- PROG/A,ARGS/M,SHOW/K,VIEWBY/K,DELAY/N/K,NOREQ/S
- Location
- C:
WBRUN will execute the program specified in argument, just like it would be if started from the WorkBench. So it will be exactly like if you double-clicked the program icon. It means that the processed program will be able to process WB messages.
When you run a program on the WorkBench, you can make it handle other icons you have selected. You can do the same with WBRUN, passing the filenames as arguments.
When used with a volume/directory name, WBRUN will open a volume/drawer window and display its content according to the SHOW and VIEWBY arguments.
SHOW allows you to open a WB window displaying there only icons (default) if "ICONS" is defined, or all files i.e. even files with no icon, if "ALL" is defined.
The VIEWBY argument allows you to define layout of the WB window that will be opened: either displaying ICON, or in list mode sorted by NAME, or sorted by DATE, or by size SIZE or by TYPE.
Also, you can define a DELAY (in seconds) WBRUN will wait before executing the program in argument.
If you don't want the executed program to open a console window for any output it may produce, specify the NOREQ argument.
- Example 1
Running a picture viewer with some images as arguments
1> WBRUN Work:picviewer Image1.iff Image2.png
- Example 2
Opening the SYS: drawer in list mode with all files
1> WBRUN Sys: SHOW=all VIEWBY=name
WBSTARTUPCTRL
Manipulates the startup configuration of Workbench.
- Format
- WBSTARTUPCTRL [PATH=<prefs file>] [ADD=<program>] [REMOVE=<program>] [QUIET]
- Template
- PATH/K,ADD/K,REMOVE/K,QUIET
- Location
- C:
WBSTARTUPCTRL allows manipulation of the configured startup modules that Workbench will load without having to open the WBStartup preferences editor.
The parameters that can be specified are as follows:
| PATH | This creates the updated preferences file at the location specified. This should be a path AND filename to save the file as. By default, it will use SYS:Prefs/Env-Archive/Sys/wbstartup.prefs. |
| ADD | This command will add the specified program to the internal list of modules that are executed when Workbench starts. This must be the full path to the program to add. If the file can not be found, an error message will be displayed. |
| REMOVE | This command removes the specified program from the internal list. The argument may contain the full path to the program to be removed, or if the path is not known, just the program name may be supplied and the list will be searched for a suitable match. |
| QUIET | Turn off any messages that may be output to the console. |
The use of the above parameters has been designed to allow installers or scripts to add or remove files from the configuration easily. Usually, when an installer has copied a program and its data, it will know the path that it has been copied to, and a simple call of this command with the correct arguments will add it to Workbench's list of programs to start.
Because the path may not be known when trying to remove a program from the list, the matching feature has been included. An addition or a removal will show a message to the standard output, which may be suppressed by using the QUIET switch.
- Example 1
Under script control, the ContextMenus commodity may be added with a call like so:
1> WBSTARTUPCTRL ADD SYS:Utilities/Commodities/ContextMenus
This program will now be launched each time Workbench starts.
- Example 2
A script may want to remove a program whose location is not known, like so:
1> WBSTARTUPCTRL REMOVE MouseBlanker
The first entry in the list that matches will be removed.
WHICH
Searches the command path for a particular item.
- Format
- WHICH <command> [NORES] [RES] [ALL]
- Template
- FILE/A,NORES/S,RES/S,ALL/S
- Location
- C:
WHICH lets you find a specific command, program, or directory by entering its name. If the named item is in the search path, WHICH displays the complete path to that item. WHICH lists resident commands as RESIDENT and internal commands as INTERNAL.
Normally, WHICH searches the resident list, the current directory, the command paths, and the C: directory. If the item is not found, WHICH sets the condition flag to 5 (WARN), but does not print any error message.
If the NORES option is specified, the resident list is not searched. If the RES option is specified, only the resident list is searched.
The ALL switch continues the search through the full search path, finding and listing all locations of a command or program. It can, however, lead to multiple listings of the same command if that command is reached by more than one route (such as C: and the current directory).
- Examples
1> WHICH avail C:Avail
1> WHICH C: Workbench:C
1> WHICH alias INTERNAL alias
WHY
Prints an error message explaining why the previous command failed.
- Format
- WHY
- Template
- (none)
- Location
- Internal
When a command fails, the screen displays a brief message. This message typically includes the name of the file, if that was the problem, but provides no details. If the reason for a failure is not evident, enter WHY for a more complete explanation.
XAD2LHA
?
- Format
- ?
- Template
- ?
- Location
- C:
Missing description.
XADLIBINFO
?
- Format
- ?
- Template
- ?
- Location
- C:
Missing description.
XADLIST
?
- Format
- ?
- Template
- ?
- Location
- C:
Missing description.
XADUNDISK
?
- Format
- ?
- Template
- ?
- Location
- C:
Missing description.
XADUNF
?
- Format
- ?
- Template
- ?
- Location
- C:
Missing description.
XADUNFILE
?
- Format
- ?
- Template
- ?
- Location
- C:
Missing description.
XADUNFILEM
?
- Format
- ?
- Template
- ?
- Location
- C:
Missing description.
XADUNTAR
?
- Format
- ?
- Template
- ?
- Location
- C:
Missing description.
XBENCH
?
- Format
- ?
- Template
- ?
- Location
- C:
Missing description.
XDIR
?
- Format
- ?
- Template
- ?
- Location
- C:
Missing description.
XLOADSEG
?
- Format
- ?
- Template
- ?
- Location
- C:
Missing description.
XPACK
?
- Format
- ?
- Template
- ?
- Location
- C:
Missing description.
XPK
?
- Format
- ?
- Template
- ?
- Location
- C:
Missing description.
XQUERY
?
- Format
- ?
- Template
- ?
- Location
- C:
Missing description.
XSCAN
?
- Format
- ?
- Template
- ?
- Location
- C:
Missing description.
XTYPE
?
- Format
- ?
- Template
- ?
- Location
- C:
Missing description.
XUP
?
- Format
- ?
- Template
- ?
- Location
- C:
Missing description.
System Commands
System commands are required for normal system operation. They are used by the standard Startup-sequence or called automatically by the system for applications. The user does not typically invoke these commands.
ADDDATATYPES
Makes new datatypes available to the system.
- Format
- ADDDATATYPES [<datatype> [<datatype>...]] [QUIET] [REFRESH] [LIST]
- Template
- FILES/M,QUIET/S,REFRESH/S,LIST/S
- Location
- C:
ADDDATATYPES can load datatype descriptors in memory. When they are loaded, applications can use them immediately.
ADDDATATYPES can also be loaded from Workbench which allows using it as default tool in an icon of a datatype descriptor file in DEVS:DataTypes/ or SYS:Storage/DataTypes/.
If the QUIET argument is used, or the local shell variable _Verbosity has a negative value, ADDDATATYPES will not display potential errors.
If the REFRESH argument is used, any newly added datatype will be added to the datatype list in memory. It has the same effect as defining all datatype names in the command line.
If the LIST argument is used, ADDDATATYPES will display the list of all datatypes in memory.
- Example
Add two newly added datatypes to the datatype list:
1> ADDDATATYPES iff jpeg
BINDDRIVERS
Binds device drivers to hardware.
- Format
- BINDDRIVERS
- Template
- (none)
- Location
- C:
BINDDRIVERS loads and runs device drivers for add-on hardware. These devices are automatically configured by the expansion library if their device drivers are in the SYS:Expansion directory.
The BINDDRIVERS command must appear in the Startup-sequence file to configure the hardware when the system is booted.
CONCLIP
Enables or disables cut/copy/paste functionality in console windows and string gadgets
- Format
- CONCLIP [[UNIT|CLIPUNIT] <unit number>] [ON|OFF]
- Template
- CLIPUNIT=UNIT/N,ON/S,OFF/S
- Location
- C:
Copy and paste operations in console windows will use the console's own private clipboard. While text can be exchanged between console windows, no other applications can access it. CONCLIP changes this by switching the console over to use the regular, system-wide clipboard functionality. Also, cut/copy/paste operations in string gadgets can be switched over to use the system-wide clipboard.
The options are:
| CLIPUNIT=<unit number> | Switch the clipboard unit number to use; default is 0. |
| ON and OFF | Turn the clipboard functionality either on or off. |
IPREFS
Communicates Preferences information stored in the individual editor files to the operating system.
- Format
- IPREFS [NEWMOUSE]
- Template
- NEWMOUSE/S
- Location
- C:
IPREFS reads the individual system Preferences files and passes the information to the system so that it can adapt accordingly. IPREFS is generally run in the Startup-sequence. Each time a user selects Save or Use from within an editor, IPREFS is notified and passes the information along to the system. If necessary, IPREFS will reset Workbench in order to implement the requested changes. If any project or tool windows are open, IPREFS will display a requester asking you to close any non-drawer windows.
If the NEWMOUSE command line option is specified, IPREFS generates NewMouse-style IECLASS_RAWKEY events for backwards compatibility to old applications that don't support standard AmigaOS mouse wheel events as introduced in Release 4.
LOADMONDRVS
Starts the monitor drivers.
- Format
- LOADMONDRVS [FROM=<path>] [EXCEPT=<file name>]
- Template
- FROM/K,EXCEPT
- Location
- C:
LOADMONDRVS starts the monitor drivers stored in the <path> directory. If the <path> argument is not given, drivers in the DEVS:Monitors directory will be started.
By default LOADMONDRVS starts all the drivers that it can find from the drivers' directory. To prevent LOADMONDRVS from starting a specific driver, use the EXCEPT parameter: <file name> is the name of the driver to be disabled.
- Example 1
1> LOADMONDRVS
starts all the monitor drives stored in the DEVS:Monitors directory.
- Example 2
1> LOADMONDRVS FROM="SYS:Storage/Monitors"
starts all the monitor drives stored in the SYS:Storage/Monitors directory.
- Example 3
1> LOADMONDRVS EXCEPT="VooDoo"
starts all the monitor drives stored in the DEVS:Monitors directory, except the VooDoo driver.
SETPATCH
Makes ROM patches in system software.
- Format
- SETPATCH [QUIET] [NOAGA] [NONSD] [PATCHCONFIGFILE=<NSDpatch file>]
- [PATCHCONFIGLINE="PatchLine"] [PATCHINFO] [WAITFORVALIDATE]
- [ADDCHIPRAM=<Size in MB>]
- Template
- QUIET/S,NOAGA/S,NONSD/S,PATCHCONFIGFILE=PCF/K,PATCHCONFIGLINE=PCL/K,PATCHINFO=PI/S,WAITFORVALIDATE/S,ADDCHIPRAM/N/K
- Location
- C:
SETPATCH installs temporary modifications to the operating system. It must be executed at the beginning of the Startup-sequence file.
By default SETPATCH enables the AGA video modes when running on an Amiga Classic with AGA chipset and the chipset was not disabled in the early startup menu. If you don't want to enable the AGA video modes, specify the NOAGA argument on the command line. When running on non-classic platforms, SETPATCH will not enable the AGA video modes (this may have happened already before) and the NOAGA argument has no effect.
SETPATCH can patch devices that don't follow the NewStyleDevice (NSD) specification released by Amiga Inc. Patches will be applied according to the list in the Devs:NSDPatch.cfg file.
Use the NONSD argument if you don't want to install patches for devices that are not NSD compliant.
To use a device list other than Devs:NSDPatch.cfg, use the PATCHCONFIGFILE argument and specify the full name of your alternate file. It is also possible to apply a patch giving it as argument to SETPATCH after the PATCHCONFIGLINE keyword. Just specify a line with the same syntax as in the NSDpatch file. Note that a complete description of the patch format is located in the Devs:NSDPatch.cfg file.
To display the patches applied by SETPATCH use the PATCHINFO argument.
When a disk is validating (after a system crash for example) it can be annoying to boot the operating system while the filesystem is busy to fix the damaged partition. In this case, the boot process may be very slow. Use the WAITFORVALIDATE switch to ask SETPATCH to wait for the end of the validation process before proceeding. Doing so you are sure that you start the system with sane partitions. Note: Pressing Ctrl-C (when an input shell window is present) or both mouse buttons will abort waiting for disk validation.
The ADDCHIPRAM option can be used on non-classic machines for backwards compatibility to old broken programs which peek system structures which were always declared as private, to be used by the operating system only. It installs an old-style MemHeader in SysBase->MemList. Note: You don't need to activate this compatibility hack for programs which simply want to allocate some Chip RAM.
By default, SETPATCH displays the operating system version and copyright as well as the list of applied patches. But if the QUIET argument is specified or the local shell variable _Verbosity has a negative value, no output will be produced.
- Example 1
Don't apply NSD patches and wait the end of the validation process.
1> SETPATCH NONSD WAITFORVALIDATE
- Example 2
Applies only the patch on audio.device.
1> SETPATCH PATCHCONFIGLINE="DEVICE audio.device DEVICETYPE NSDEVTYPE_AUDIO VERSION 50 REVISION 5 ISNSD"
- Example 3
Adds a MemHeader with 2MB Chip RAM as backwards compatibility hack for broken applications and suppresses the normal output.
1> SETPATCH QUIET ADDCHIPRAM=2